In today's interconnected world, using SSH for remote IoT management has become an essential skill for developers and IT professionals. Secure Shell (SSH) provides a secure way to access and manage devices remotely, which is critical for IoT applications. With SSH, you can control devices, transfer files, and monitor systems securely from anywhere in the world.
As more devices become connected through the Internet of Things (IoT), the need for secure and efficient management solutions grows. SSH plays a pivotal role in ensuring that these devices remain secure and accessible without compromising on privacy or performance. Whether you're managing a smart home system or an industrial IoT setup, understanding how to use SSH for remote IoT operations is crucial.
This guide will walk you through the process of using SSH for remote IoT management, covering everything from setting up your environment to troubleshooting common issues. By the end of this article, you'll have a solid understanding of how SSH works and how it can be applied effectively in IoT scenarios.
Read also:Tre Johnson The Rising Star In The Music Industry
Table of Contents
- Introduction to SSH
- Why Use SSH for IoT?
- Setting Up SSH
- Connecting to Remote Devices
- Securing Your SSH Connection
- Advanced SSH Features
- Troubleshooting SSH
- Best Practices for SSH in IoT
- Real-World SSH IoT Examples
- Future of SSH in IoT
Introduction to SSH
Secure Shell (SSH) is a cryptographic network protocol used for secure data communication, remote command execution, and other network services between two networked computers. It was designed as a replacement for less secure protocols like Telnet and rsh. SSH ensures that data transmitted between devices is encrypted, making it difficult for attackers to intercept sensitive information.
SSH is widely used in IoT environments because it provides a reliable method for managing devices remotely. Whether you're configuring sensors, updating firmware, or monitoring logs, SSH allows you to perform these tasks securely and efficiently. The protocol supports various authentication methods, including passwords and public key cryptography, giving users flexibility in how they secure their connections.
Why Use SSH for IoT?
IoT devices often operate in unsecured environments, making them vulnerable to attacks. Using SSH for remote IoT management helps mitigate these risks by providing a secure channel for communication. Below are some reasons why SSH is a preferred choice for IoT applications:
- Encryption: SSH encrypts all data transmitted between devices, preventing unauthorized access.
- Authentication: SSH supports strong authentication mechanisms, ensuring that only authorized users can access devices.
- Reliability: SSH connections are stable and can be configured to automatically reconnect if interrupted.
- Scalability: SSH can be used to manage multiple devices simultaneously, making it ideal for large-scale IoT deployments.
Setting Up SSH
Before you can use SSH for remote IoT management, you need to set it up on both the server (IoT device) and the client (your computer). Here's a step-by-step guide to help you get started:
On the IoT Device
1. Install an SSH server on your IoT device. Most Linux-based devices come with OpenSSH pre-installed. If not, you can install it using the following command:
sudo apt-get install openssh-server
Read also:Kraken Vs Wild Unveiling The Epic Battle Of Marine Legends
2. Configure the SSH server by editing the configuration file located at /etc/ssh/sshd_config. Make sure to set the correct port number and disable root login for added security.
On Your Computer
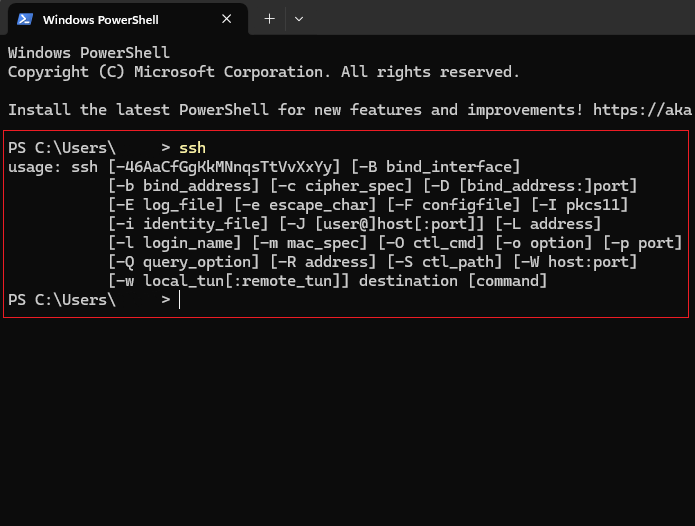
1. Install an SSH client if you're using Windows. On macOS and Linux, SSH clients are usually pre-installed.
2. Test the connection by running the following command:
ssh username@device_ip_address
Connecting to Remote Devices
Once SSH is set up, you can connect to your IoT devices remotely. Here's how:
1. Open your terminal or command prompt.
2. Enter the SSH command followed by the username and IP address of your IoT device:
ssh username@device_ip_address
3. Enter your password when prompted. If you're using SSH keys, the connection will be established automatically without requiring a password.
Securing Your SSH Connection
Security is paramount when dealing with IoT devices. Here are some tips to secure your SSH connections:
- Use Strong Passwords: Ensure that your passwords are complex and unique.
- Enable Two-Factor Authentication: Add an extra layer of security by requiring a second form of verification.
- Disable Root Login: Prevent direct access to the root account to reduce the risk of unauthorized access.
- Limit Access: Restrict SSH access to specific IP addresses or networks.
Advanced SSH Features
SSH offers several advanced features that can enhance your IoT management capabilities. Below are some of the most useful ones:
Port Forwarding
Port forwarding allows you to access services running on your IoT device from your local machine. This is particularly useful when managing services that are not exposed to the public internet.
Tunneling
SSH tunneling creates a secure channel between two devices, allowing you to transmit data securely over unsecured networks. This is especially useful for IoT devices operating in public environments.
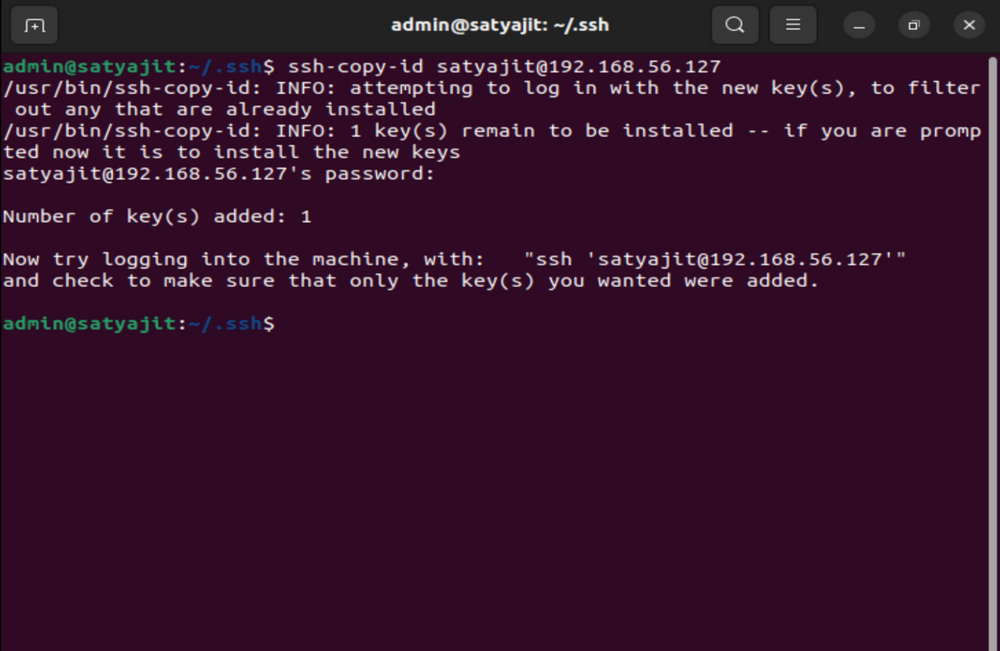
SSH Keys
SSH keys provide a more secure alternative to password-based authentication. They consist of a public key (stored on the server) and a private key (stored on the client). Using SSH keys eliminates the need to enter passwords every time you connect to a device.
Troubleshooting SSH
Even with proper setup, SSH connections can sometimes fail. Here are some common issues and how to resolve them:
- Connection Refused: Ensure that the SSH service is running on the IoT device and that the firewall allows incoming connections on the specified port.
- Authentication Failed: Double-check your username, password, and SSH keys. Make sure they are correctly configured.
- Timeout Errors: Check your network connection and ensure that there are no routing issues between your computer and the IoT device.
Best Practices for SSH in IoT
Adopting best practices can help you make the most out of SSH for IoT management. Here are some recommendations:
- Regularly Update Software: Keep your SSH server and client software up to date to protect against vulnerabilities.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities.
- Use Separate Networks: Isolate IoT devices on a separate network to minimize the risk of attacks spreading to other systems.
Real-World SSH IoT Examples
SSH is used in various real-world IoT applications. For instance, it is commonly used in smart home systems to manage devices like smart thermostats and security cameras. In industrial settings, SSH is employed to monitor and control machinery remotely, ensuring optimal performance and reducing downtime.
Future of SSH in IoT
As IoT continues to evolve, the role of SSH in securing and managing devices will become even more critical. Advances in encryption technologies and authentication methods will further enhance the security of SSH connections. Additionally, the integration of SSH with emerging technologies like blockchain could provide new ways to secure IoT ecosystems.
Conclusion
Using SSH for remote IoT management offers numerous advantages, including enhanced security, reliability, and scalability. By following the steps outlined in this guide, you can effectively set up and utilize SSH to manage your IoT devices. Remember to adhere to best practices and stay informed about the latest developments in SSH and IoT security.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and related technologies. Together, let's build a safer and more connected world!
References: