SSH IoT Device Anywhere AWS Example: The Internet of Things (IoT) continues to revolutionize industries by enabling seamless communication between devices. However, securely accessing IoT devices from anywhere remains a critical challenge for developers and administrators. This article will explore how you can leverage AWS services to establish secure SSH connections to IoT devices, ensuring robust security and reliability.
In today's hyper-connected world, IoT devices are deployed across diverse locations, from remote industrial sites to smart homes. Ensuring secure remote access to these devices is vital for maintenance, monitoring, and troubleshooting. AWS provides an extensive suite of tools and services that facilitate secure SSH connections to IoT devices, empowering administrators to manage their devices efficiently.
This guide will walk you through the entire process, from setting up your AWS environment to establishing secure SSH connections. Whether you're a developer, system administrator, or IT professional, this article will equip you with the knowledge and tools necessary to implement secure remote access for your IoT devices using AWS.
Read also:Unveiling The Remarkable Life And Achievements Of Spencer Jones
Table of Contents
- Introduction to SSH IoT Device Anywhere with AWS
- Why Choose AWS for SSH IoT Device Connections?
- Setting Up Your AWS Environment
- Securing Your SSH Connections
- AWS Tools for IoT Device Management
- A Practical Example of SSH IoT Device Anywhere
- Common Issues and Troubleshooting
- Scalability Considerations
- Cost Management for SSH IoT Deployments
- Conclusion and Next Steps
Introduction to SSH IoT Device Anywhere with AWS
The concept of "SSH IoT Device Anywhere" refers to the ability to securely access IoT devices from any location using SSH (Secure Shell). This functionality is particularly valuable for organizations managing distributed IoT deployments, where devices may be located in remote or hard-to-reach areas.
Understanding SSH in IoT
SSH is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. When applied to IoT, SSH ensures that administrators can access and manage devices without compromising their security. AWS enhances this capability by providing robust infrastructure and services that simplify the process of establishing secure SSH connections.
Key Benefits of Using AWS for SSH IoT Connections
- Security: AWS offers advanced security features, including encryption and identity management, to protect your SSH connections.
- Scalability: The platform supports large-scale deployments, making it ideal for organizations with numerous IoT devices.
- Reliability: AWS ensures high availability and fault tolerance, minimizing downtime and ensuring consistent access to your IoT devices.
Why Choose AWS for SSH IoT Device Connections?
AWS stands out as the preferred platform for managing SSH connections to IoT devices due to its comprehensive suite of services and tools. Below are some reasons why AWS is the go-to choice for developers and administrators:
Advanced Security Features
AWS provides state-of-the-art security measures, including IAM (Identity and Access Management), encryption, and network security groups, to safeguard your IoT devices and SSH connections.
Seamless Integration with IoT Services
AWS IoT Core and other related services integrate effortlessly with SSH, enabling a streamlined approach to device management. This integration simplifies the process of monitoring, updating, and troubleshooting IoT devices.
Setting Up Your AWS Environment
Before establishing SSH connections to your IoT devices, you need to set up your AWS environment properly. This section will guide you through the essential steps:
Read also:Xrp The Revolutionary Digital Asset Redefining Financial Transactions
Creating an AWS Account
Begin by creating an AWS account if you don't already have one. This account will serve as the foundation for all your AWS activities, including managing SSH connections to IoT devices.
Configuring IAM Roles and Policies
Set up IAM roles and policies to define permissions for accessing your IoT devices via SSH. Proper configuration ensures that only authorized users can establish connections, enhancing security.
Securing Your SSH Connections
Security is paramount when managing IoT devices remotely. AWS provides several tools and best practices to secure your SSH connections:
Using SSH Keys for Authentication
Implement SSH key-based authentication to eliminate the need for passwords, reducing the risk of unauthorized access. AWS supports secure key management, making it easier to generate and distribute SSH keys.
Implementing Network Security Groups
Configure network security groups to control inbound and outbound traffic to your IoT devices. This ensures that only trusted sources can initiate SSH connections.
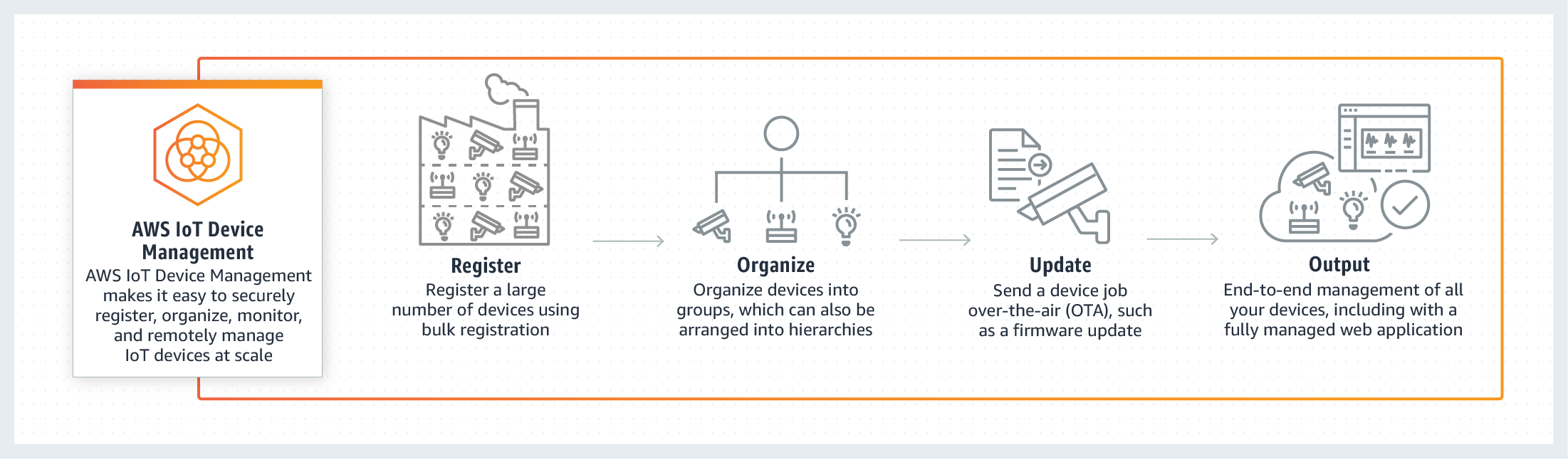
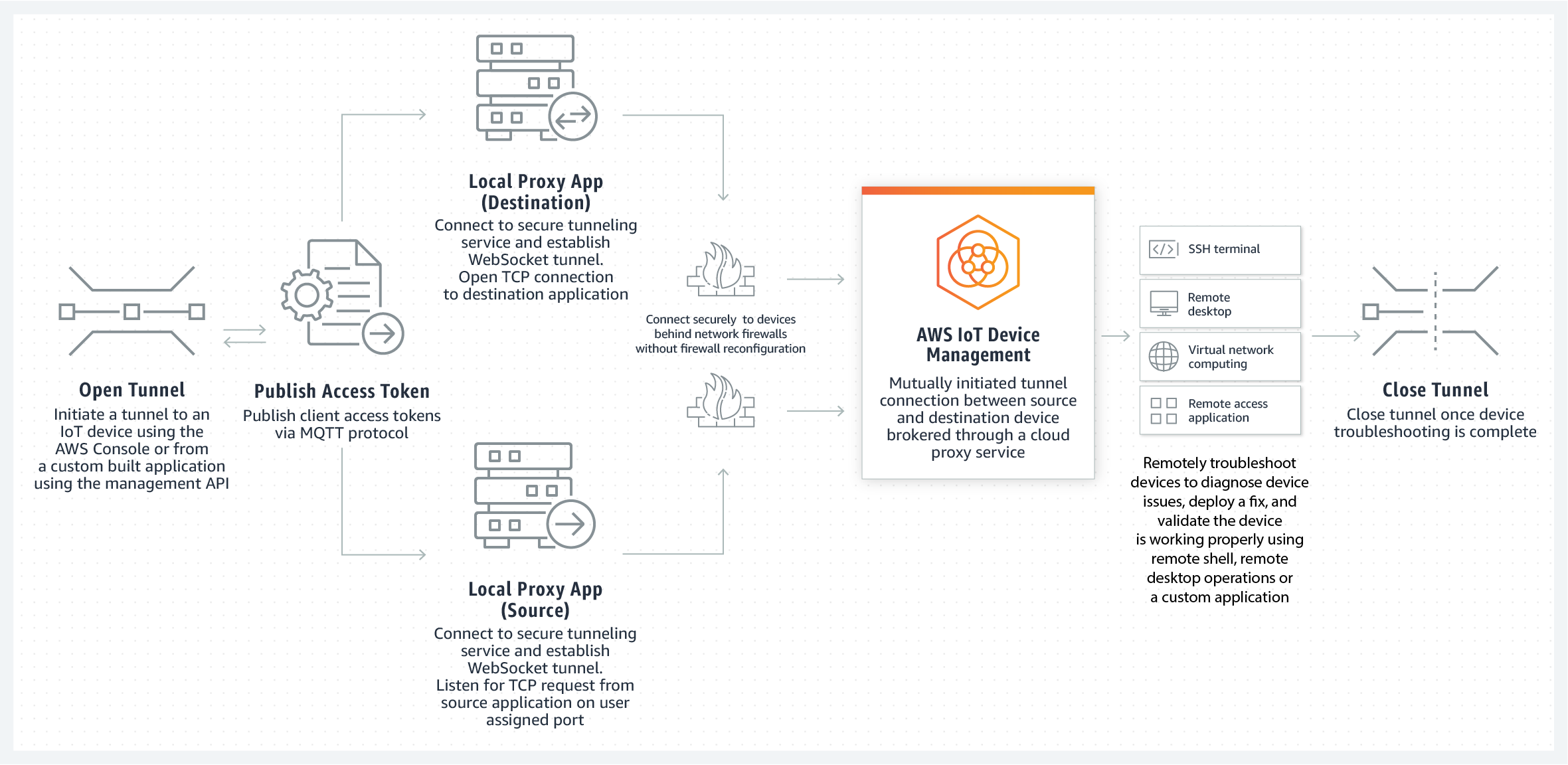
AWS Tools for IoT Device Management
AWS offers a range of tools that facilitate the management of IoT devices and SSH connections:
AWS IoT Core
AWS IoT Core serves as the central hub for managing IoT devices. It enables secure and scalable communication between devices and the AWS cloud, supporting SSH connections and other protocols.
AWS Systems Manager
AWS Systems Manager simplifies the management of IoT devices by providing tools for remote access, monitoring, and troubleshooting. It integrates seamlessly with SSH, enhancing the overall device management experience.
A Practical Example of SSH IoT Device Anywhere
To illustrate how SSH IoT Device Anywhere works with AWS, consider the following example:
Scenario: Managing Remote Industrial Sensors
Imagine a manufacturing facility with numerous IoT sensors deployed across multiple locations. By leveraging AWS services, administrators can securely access these sensors via SSH from anywhere, enabling real-time monitoring and maintenance.
Steps to Implement
- Set up an AWS IoT Core account and register the sensors as devices.
- Configure SSH keys and assign appropriate IAM roles for secure access.
- Use AWS Systems Manager to establish SSH connections and manage the sensors remotely.
Common Issues and Troubleshooting
While AWS provides robust tools for managing SSH connections, challenges may arise. Below are some common issues and their solutions:
Connection Failures
If you encounter connection failures, verify your network security group settings and ensure that the necessary ports are open. Additionally, check your SSH key configuration to confirm proper authentication.
Performance Bottlenecks
For large-scale deployments, performance bottlenecks may occur. Optimize your AWS environment by leveraging load balancing and auto-scaling features to handle increased traffic.
Scalability Considerations
As your IoT deployment grows, scalability becomes a critical factor. AWS offers several options to ensure your SSH IoT setup can accommodate increasing demands:
Auto Scaling
Implement auto-scaling to dynamically adjust resources based on workload. This ensures optimal performance and cost efficiency as your deployment expands.
Multi-Region Deployment
Consider deploying your IoT devices across multiple AWS regions to enhance redundancy and availability. This approach minimizes downtime and ensures consistent access to your devices.
Cost Management for SSH IoT Deployments
Managing costs is essential for sustainable IoT deployments. AWS provides tools to monitor and optimize expenses:
Cost Explorer
Utilize AWS Cost Explorer to analyze your spending patterns and identify areas for cost reduction. This tool offers detailed insights into resource usage and billing.
Reserved Instances
Purchase reserved instances for predictable workloads to reduce costs. This option provides significant savings compared to on-demand pricing.
Conclusion and Next Steps
In conclusion, SSH IoT Device Anywhere with AWS offers a secure and efficient solution for managing IoT devices remotely. By leveraging AWS services, organizations can ensure robust security, scalability, and reliability in their IoT deployments.
We encourage readers to experiment with the techniques and tools discussed in this article. Share your experiences and insights in the comments section, and don't forget to explore other resources on our site for further learning.
References: