In today's interconnected world, securely connect remote IoT VPC has become a critical necessity for businesses of all sizes. The Internet of Things (IoT) has revolutionized the way we interact with devices, but it also introduces significant security challenges. Ensuring a secure connection between remote IoT devices and Virtual Private Cloud (VPC) is paramount to safeguarding sensitive data and maintaining operational efficiency.
As companies increasingly adopt IoT technology, the need for secure communication channels becomes more pronounced. Remote IoT devices often operate in uncontrolled environments, making them vulnerable to cyberattacks. A secure VPC acts as a fortress, protecting your data and ensuring uninterrupted communication between devices.
This comprehensive guide delves into the intricacies of securely connecting remote IoT devices to a VPC. We'll explore best practices, advanced security measures, and practical implementation strategies to help you fortify your network infrastructure. Let's embark on this journey to enhance your IoT security framework.
Read also:Unblocked Games G The Ultimate Guide To Fun And Entertainment
Table of Contents
- Introduction to IoT VPC Security
- Understanding IoT and VPC Basics
- Challenges in Securing IoT VPC
- Best Practices for Securely Connect Remote IoT VPC
- Tools and Technologies for IoT VPC Security
- Importance of Encryption in IoT VPC
- Designing a Secure Network Architecture
- Authentication and Authorization in IoT VPC
- Monitoring and Incident Response
- Future Trends in IoT VPC Security
Introduction to IoT VPC Security
The rapid proliferation of IoT devices has transformed industries, enabling smarter and more efficient operations. However, this growth also brings challenges, particularly in securely connect remote IoT VPC. A Virtual Private Cloud (VPC) serves as a secure and isolated environment within a public cloud, providing a safe space for IoT devices to communicate.
Securing an IoT VPC requires a multi-layered approach that addresses potential vulnerabilities at every level. From device-level security to network encryption, each component plays a crucial role in maintaining the integrity of the system. Understanding the fundamentals of IoT and VPC security is the first step toward building a robust framework.
Understanding IoT and VPC Basics
What is IoT?
The Internet of Things refers to a network of interconnected devices that communicate with each other and with the cloud. These devices collect and exchange data, enabling automation and real-time insights. IoT applications span various sectors, including healthcare, manufacturing, and smart homes.
What is VPC?
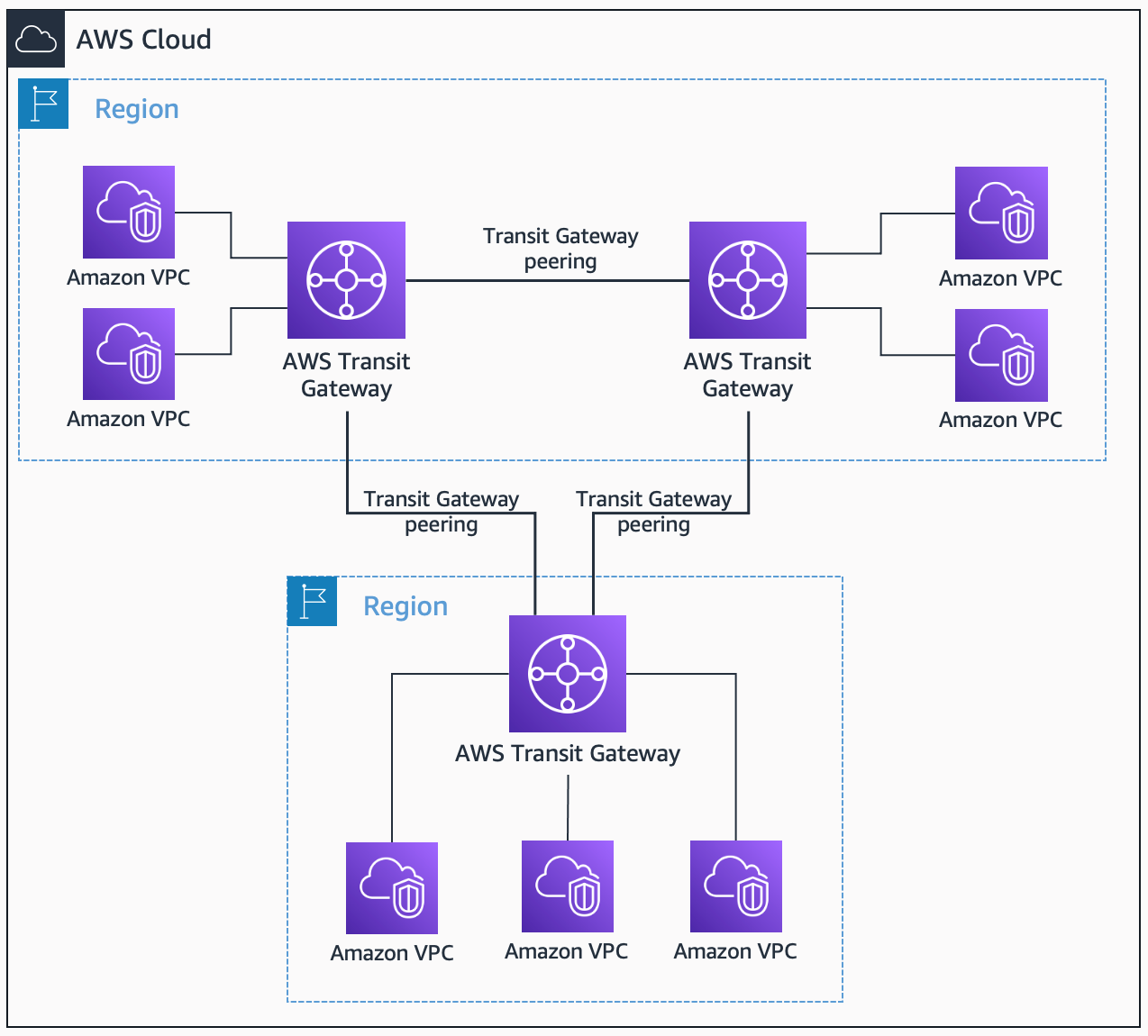
A Virtual Private Cloud is a virtual network dedicated to your AWS environment. It allows you to launch resources in a virtual network that you define, providing complete control over network settings and security. VPCs are essential for securely connect remote IoT VPC, ensuring that only authorized devices can access the network.
Challenges in Securing IoT VPC
Securing an IoT VPC presents several challenges, including device authentication, data encryption, and network segmentation. IoT devices often have limited processing power, making it difficult to implement complex security protocols. Additionally, the distributed nature of IoT devices increases the attack surface, making them more susceptible to cyber threats.
- Limited device resources
- Uncontrolled operating environments
- Rapidly evolving threat landscape
- Complexity of managing large-scale IoT deployments
Best Practices for Securely Connect Remote IoT VPC
To ensure a secure connection between remote IoT devices and a VPC, organizations should adopt the following best practices:
Read also:Meet Melanie Jolys Kids A Closer Look At Her Family Life
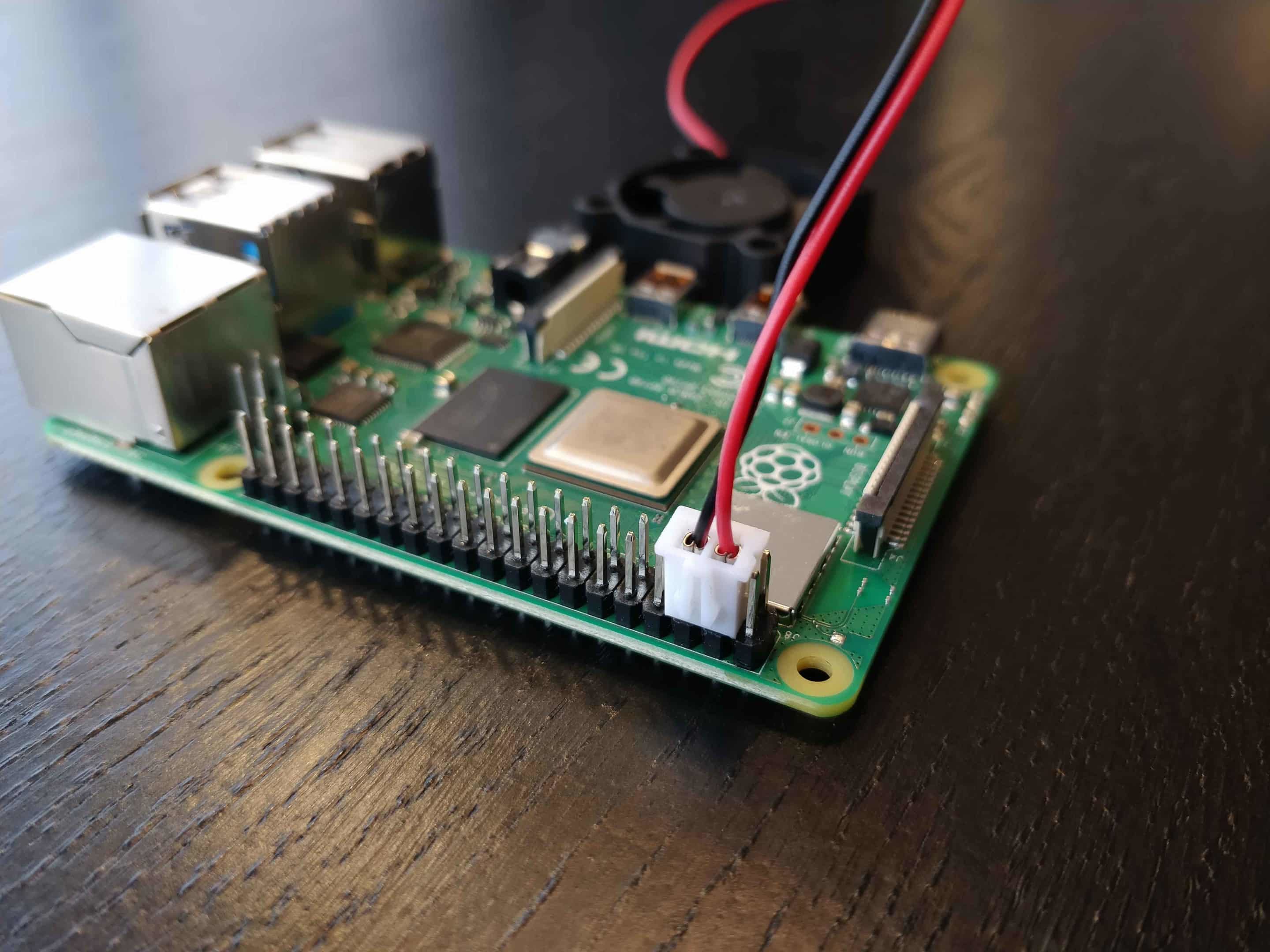
Device Security
Securing IoT devices at the hardware and software levels is crucial. Implementing secure boot processes, firmware updates, and device-level encryption can significantly reduce vulnerabilities.
Network Segmentation
Segmenting the network into smaller, isolated subnets limits the potential impact of a breach. This approach ensures that even if one device is compromised, the rest of the network remains secure.
Regular Audits
Conducting regular security audits helps identify and address potential vulnerabilities before they can be exploited. This proactive approach is essential for maintaining a secure IoT VPC environment.
Tools and Technologies for IoT VPC Security
Several tools and technologies are available to enhance the security of IoT VPC environments. These include:
- Firewalls: Protecting the network perimeter from unauthorized access.
- Intrusion Detection Systems (IDS): Monitoring network traffic for suspicious activity.
- Security Information and Event Management (SIEM): Centralizing security information for better analysis and response.
Importance of Encryption in IoT VPC
Encryption is a cornerstone of securely connect remote IoT VPC. It ensures that data transmitted between devices and the VPC remains confidential and cannot be intercepted by unauthorized parties. Implementing end-to-end encryption, both at rest and in transit, is essential for safeguarding sensitive information.
Designing a Secure Network Architecture
A well-designed network architecture is critical for securely connect remote IoT VPC. This involves:
Network Segmentation
Dividing the network into smaller, isolated segments reduces the attack surface and limits the potential impact of a breach.
Access Control
Implementing strict access control measures ensures that only authorized devices and users can access the network. This can be achieved through multi-factor authentication and role-based access control.
Authentication and Authorization in IoT VPC
Authentication and authorization are key components of securely connect remote IoT VPC. These processes verify the identity of devices and users and determine their level of access to the network. Implementing robust authentication mechanisms, such as OAuth 2.0 and JSON Web Tokens (JWT), is essential for maintaining security.
Monitoring and Incident Response
Continuous monitoring of the IoT VPC environment is crucial for detecting and responding to security incidents. Implementing a comprehensive incident response plan ensures that any breaches are addressed promptly and effectively. This involves:
- Real-time monitoring of network traffic
- Automated alert systems for suspicious activity
- Rapid response teams to address security incidents
Future Trends in IoT VPC Security
The field of IoT VPC security is rapidly evolving, with new technologies and approaches emerging to address emerging threats. Some of the key trends include:
AI and Machine Learning
AI and machine learning are increasingly being used to enhance security by analyzing large datasets and identifying patterns indicative of potential threats. These technologies enable more accurate and proactive threat detection.
Quantum Cryptography
Quantum cryptography promises to revolutionize data encryption by providing unbreakable security. As quantum computing becomes more prevalent, this technology will play a crucial role in securing IoT VPC environments.
Conclusion
Securing an IoT VPC requires a comprehensive approach that addresses potential vulnerabilities at every level. By adopting best practices, leveraging advanced tools and technologies, and staying informed about emerging trends, organizations can effectively protect their IoT networks. We encourage you to implement these strategies and share your experiences in the comments section below. Additionally, feel free to explore our other articles on IoT security and network architecture for further insights.
Remember, the security of your IoT VPC is only as strong as its weakest link. Stay vigilant, and take proactive steps to fortify your network infrastructure.
Sources: