In the era of advanced technology, securely connecting remote IoT devices through AWS VPC using a Raspberry Pi has become a necessity for many businesses and tech enthusiasts. The Internet of Things (IoT) is revolutionizing how we interact with technology, but ensuring secure communication between devices is critical. This guide will provide step-by-step instructions on how to set up a secure connection for remote IoT devices using AWS Virtual Private Cloud (VPC) and a Raspberry Pi, all while offering free resources for download.
This article will explore the importance of secure connections in IoT ecosystems, the role of AWS VPC in enhancing security, and the practical steps to integrate Raspberry Pi into your cloud infrastructure. Whether you're a beginner or an experienced developer, this guide will equip you with the knowledge to protect your IoT devices effectively.
By the end of this article, you'll have a clear understanding of how to establish a secure connection for remote IoT devices, ensuring data privacy and protection. Let's dive into the world of IoT, AWS, and Raspberry Pi to create a robust and secure network.
Read also:Atleacutetico Nacional Vs Tolima A Deep Dive Into The Rivalry And Their Legacy
Understanding IoT and Its Security Challenges
The Internet of Things (IoT) refers to the network of physical objects embedded with sensors, software, and connectivity to exchange data with other devices and systems over the internet. While IoT offers countless benefits, such as increased efficiency and automation, it also introduces significant security challenges. Devices in an IoT network are often vulnerable to cyberattacks, data breaches, and unauthorized access.
Key Security Concerns in IoT
Here are some of the primary security concerns associated with IoT devices:
- Data Privacy: IoT devices collect vast amounts of sensitive data, which can be exploited if not properly secured.
- Device Authentication: Ensuring that only authorized devices can access the network is crucial for maintaining security.
- Firmware Vulnerabilities: Many IoT devices run outdated firmware, making them susceptible to attacks.
- Network Security: Weak network configurations can expose IoT devices to external threats.
What Is AWS VPC and Why Is It Essential?
AWS Virtual Private Cloud (VPC) is a service provided by Amazon Web Services that allows users to create an isolated virtual network in the AWS Cloud. With AWS VPC, you can define your own IP address range, create subnets, configure route tables, and set up security groups to control access to resources. This service is essential for securely connecting remote IoT devices to your network.
Benefits of Using AWS VPC for IoT
- Enhanced Security: AWS VPC provides robust security features, such as security groups and network access control lists (NACLs), to protect your IoT devices.
- Scalability: AWS VPC can easily scale to accommodate a growing number of IoT devices.
- Flexibility: You can customize your VPC to meet the specific needs of your IoT ecosystem.
Introducing Raspberry Pi in IoT Deployments
Raspberry Pi is a low-cost, credit-card-sized computer that can be used for a variety of applications, including IoT deployments. Its versatility, ease of use, and affordability make it an ideal choice for connecting IoT devices to the cloud. By integrating Raspberry Pi with AWS VPC, you can create a secure and efficient IoT network.
Advantages of Using Raspberry Pi for IoT
- Cost-Effective: Raspberry Pi is an affordable solution for IoT projects.
- Open-Source: Raspberry Pi supports a wide range of open-source software, making it easy to develop custom solutions.
- Community Support: The Raspberry Pi community provides extensive resources and support for developers.
Steps to Securely Connect Remote IoT VPC Raspberry Pi AWS
Setting up a secure connection for remote IoT devices using AWS VPC and Raspberry Pi involves several steps. Below is a comprehensive guide to help you through the process.
Step 1: Set Up Your AWS Account
Before you begin, ensure that you have an active AWS account. If you don't have one, sign up for a free tier account to get started. Once your account is ready, follow these steps:
Read also:Dollar Tl Understanding The Dynamics Between The Us Dollar And Turkish Lira
- Create a new VPC in the AWS Management Console.
- Configure subnets, route tables, and security groups for your VPC.
- Launch an EC2 instance within your VPC to serve as a gateway for IoT devices.
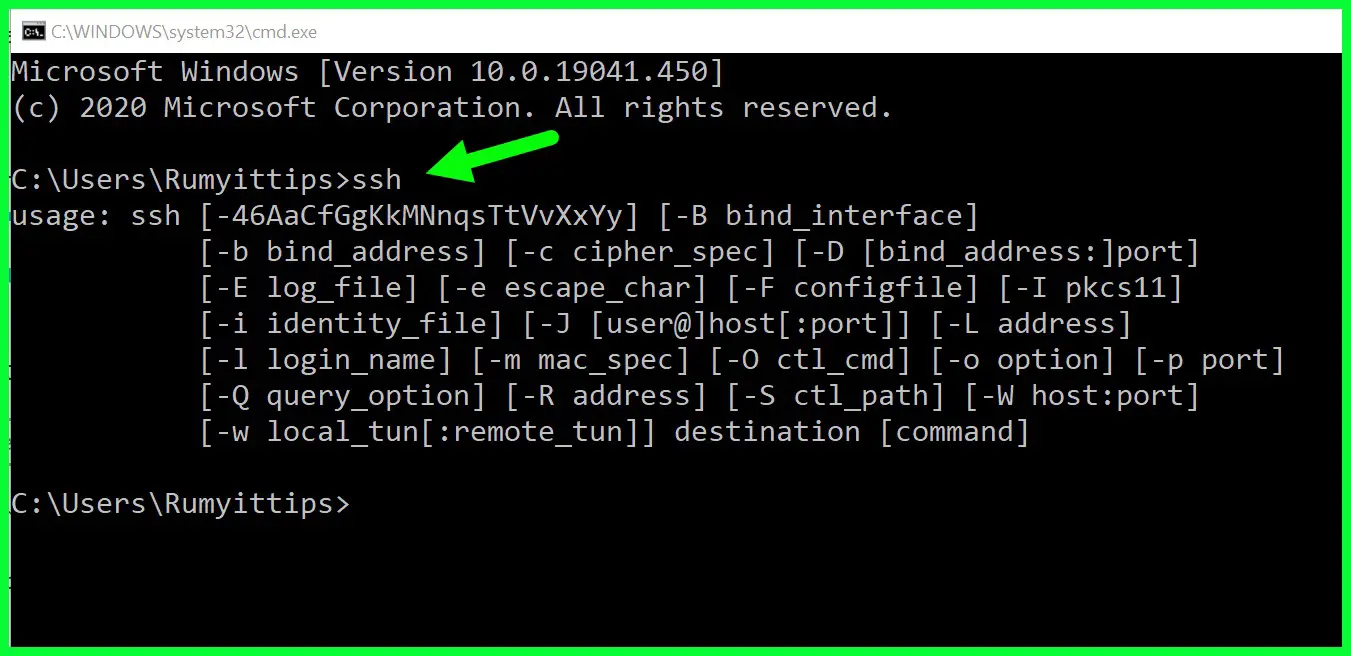
Step 2: Configure Raspberry Pi
Prepare your Raspberry Pi by installing the necessary software and libraries. Here's what you need to do:
- Install Raspbian OS on your Raspberry Pi.
- Update the system and install Python libraries for AWS SDK.
- Configure the Raspberry Pi to communicate with your AWS VPC.
Free Resources for Download
There are several free resources available to help you with your IoT project. Below are some useful downloads:
- AWS Free Tier: Get started with AWS services for free.
- Raspberry Pi Software: Download the latest Raspbian OS and other software for your Raspberry Pi.
- AWS IoT Documentation: Access comprehensive guides and tutorials for AWS IoT.
Best Practices for Securing IoT Devices
Securing IoT devices requires a multi-layered approach. Here are some best practices to consider:
Data Encryption
Encrypt all data transmitted between IoT devices and the cloud to prevent unauthorized access. Use protocols such as TLS/SSL to secure communication channels.
Device Authentication
Implement strong authentication mechanisms, such as X.509 certificates, to verify the identity of IoT devices. This ensures that only authorized devices can access your network.
Regular Updates
Keep your IoT devices and software up to date with the latest security patches and firmware updates. This helps protect against known vulnerabilities.
Case Studies and Real-World Examples
To better understand the practical applications of securely connecting remote IoT devices using AWS VPC and Raspberry Pi, let's look at some real-world examples:
Example 1: Smart Home Automation
A homeowner uses Raspberry Pi to connect various smart home devices, such as lights, thermostats, and security cameras, to AWS VPC. This setup allows the homeowner to remotely monitor and control their devices while ensuring data privacy and security.
Example 2: Industrial IoT
A manufacturing company deploys IoT sensors to monitor equipment performance and predict maintenance needs. By integrating Raspberry Pi with AWS VPC, the company can securely transmit sensor data to the cloud for analysis, improving operational efficiency.
Future Trends in IoT Security
The field of IoT security is rapidly evolving, with new technologies and strategies emerging to address existing challenges. Some future trends to watch include:
- Blockchain Technology: Blockchain can enhance IoT security by providing a decentralized and tamper-proof ledger for data transactions.
- AI-Powered Security: Artificial intelligence can be used to detect and respond to potential threats in real-time, improving overall security.
- Quantum Cryptography: As quantum computing becomes more prevalent, quantum cryptography may offer new ways to secure IoT communications.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using AWS VPC and Raspberry Pi is a powerful solution for protecting your IoT ecosystem. By following the steps outlined in this guide and adopting best practices for IoT security, you can create a robust and secure network for your devices.
We encourage you to take action by downloading the free resources mentioned in this article and experimenting with your own IoT projects. Share your experiences and insights in the comments section below, and don't forget to explore other articles on our site for more information on IoT, AWS, and Raspberry Pi.
Table of Contents
- Understanding IoT and Its Security Challenges
- What Is AWS VPC and Why Is It Essential?
- Introducing Raspberry Pi in IoT Deployments
- Steps to Securely Connect Remote IoT VPC Raspberry Pi AWS
- Free Resources for Download
- Best Practices for Securing IoT Devices
- Case Studies and Real-World Examples
- Future Trends in IoT Security
- Conclusion and Call to Action
- Table of Contents