In today's interconnected world, the Internet of Things (IoT) has revolutionized how we interact with technology. However, securely connecting remote IoT devices, especially within a Virtual Private Cloud (VPC) environment, is crucial for safeguarding sensitive data. This article dives deep into the best practices to securely connect remote IoT VPC Raspberry Pi while ensuring secure downloads.
The rapid proliferation of IoT devices has brought convenience, but it also poses significant security challenges. From smart homes to industrial automation, IoT devices are vulnerable to cyber threats unless properly secured. One effective solution is using a Virtual Private Cloud (VPC) to isolate and protect IoT devices, especially when using a Raspberry Pi as a central hub.
This article will explore the intricacies of securely connecting remote IoT devices in a VPC environment, focusing on Raspberry Pi configurations and secure download practices. By the end, you'll have a comprehensive understanding of how to safeguard your IoT ecosystem.
Read also:Copa Catalunya Exploring The Thrilling Regional Football Tournament
Table of Contents
- Introduction to IoT Security
- Understanding Virtual Private Cloud (VPC)
- Setting Up Raspberry Pi for IoT
- Steps to Securely Connect Remote IoT Devices
- Ensuring Secure Downloads in IoT Networks
- Best Practices for IoT Security
- Troubleshooting Common IoT Security Issues
- Data Protection and Privacy in IoT
- Future Trends in IoT Security
- Conclusion
Introduction to IoT Security
Why IoT Security Matters
The Internet of Things (IoT) has transformed industries by enabling seamless communication between devices. However, this interconnectedness comes with inherent risks. Cybercriminals can exploit vulnerabilities in IoT devices to gain unauthorized access, compromise data, or disrupt operations. Securely connect remote IoT VPC Raspberry Pi is one of the most effective strategies to mitigate these risks.
IoT security is not just about protecting individual devices; it's about safeguarding entire networks. A breach in one device can compromise the entire system, leading to significant financial and reputational damage. Therefore, implementing robust security measures is paramount.
Key Challenges in IoT Security
- Limited processing power and memory in IoT devices
- Fragmented security standards across manufacturers
- Difficulty in updating firmware and software on remote devices
Addressing these challenges requires a multi-layered approach, combining hardware, software, and network security solutions.
Understanding Virtual Private Cloud (VPC)
A Virtual Private Cloud (VPC) is a dedicated network environment within a public cloud that provides isolation and security for IoT devices. By securely connect remote IoT VPC Raspberry Pi, you can create a private network that limits access to authorized users and devices only.
Benefits of Using VPC for IoT
- Enhanced security through network isolation
- Flexible scalability to accommodate growing IoT ecosystems
- Granular control over access permissions and traffic routing
VPCs are particularly useful for IoT deployments where sensitive data is transmitted between devices. They provide a secure environment for data processing and storage, reducing the risk of unauthorized access.
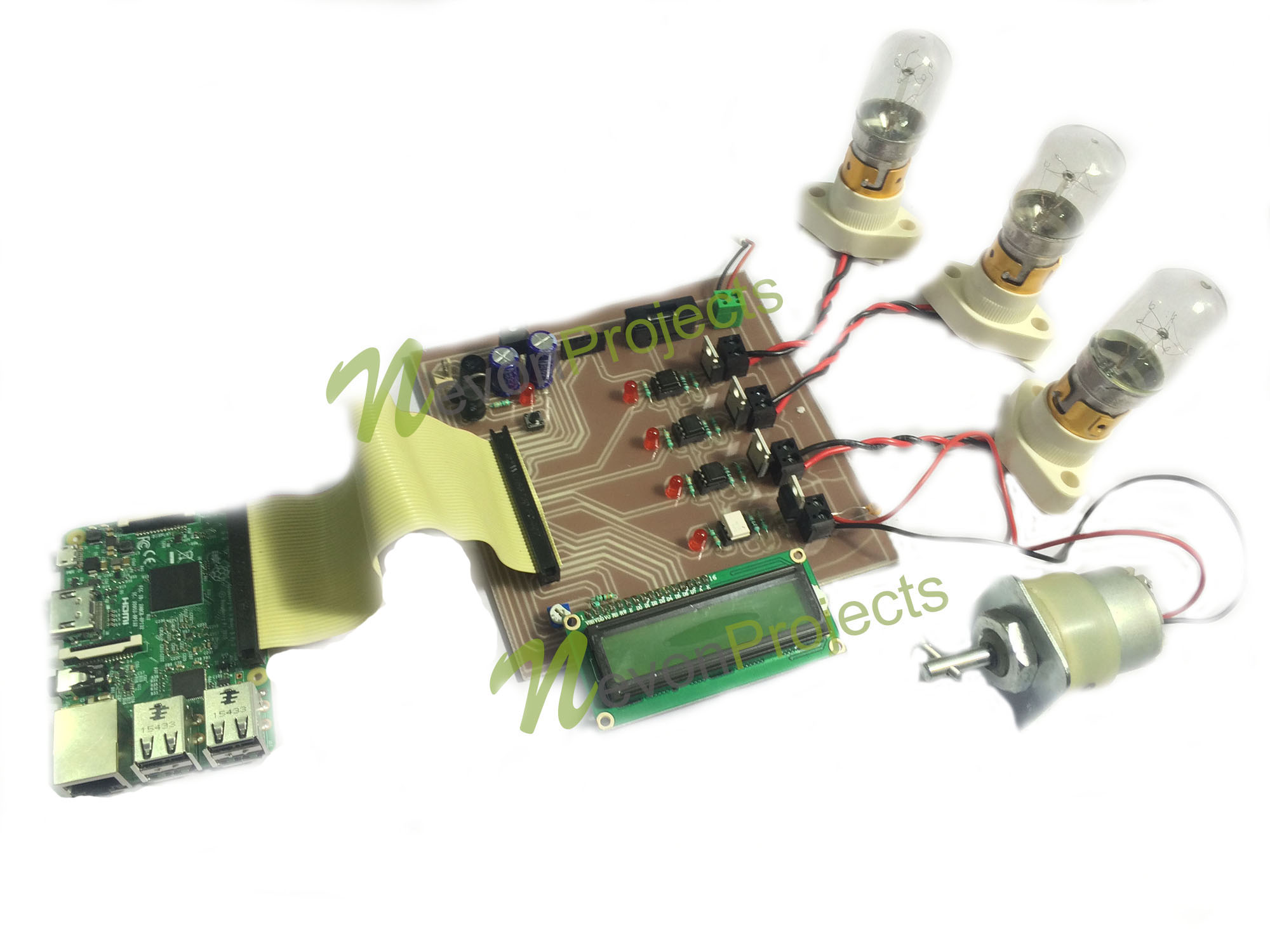
Setting Up Raspberry Pi for IoT
The Raspberry Pi is a versatile single-board computer that serves as an excellent platform for IoT projects. To securely connect remote IoT VPC Raspberry Pi, you need to configure it properly to ensure maximum security.
Read also:Chicago Tornado Watch A Comprehensive Guide To Staying Safe And Informed
Step-by-Step Guide to Raspberry Pi Configuration
- Install a secure operating system like Raspbian with built-in security features
- Enable SSH for remote access and configure firewall rules to restrict unauthorized connections
- Set up a static IP address to ensure consistent network communication
Additionally, consider using encryption protocols like SSL/TLS to protect data transmitted between the Raspberry Pi and other IoT devices.
Steps to Securely Connect Remote IoT Devices
Network Segmentation
Network segmentation involves dividing a network into smaller subnetworks to limit the spread of potential security breaches. When securely connect remote IoT VPC Raspberry Pi, network segmentation ensures that a breach in one device does not compromise the entire network.
Authentication and Authorization
- Implement strong authentication mechanisms such as multi-factor authentication (MFA)
- Use role-based access control (RBAC) to define user permissions and restrict access to sensitive areas
Authentication and authorization are critical components of IoT security, ensuring that only authorized users and devices can access the network.
Ensuring Secure Downloads in IoT Networks
Secure downloads are essential for maintaining the integrity of IoT devices and networks. When securely connect remote IoT VPC Raspberry Pi, ensure that all software updates and firmware downloads are authenticated and encrypted.
Best Practices for Secure Downloads
- Use trusted repositories for software and firmware updates
- Verify the authenticity of downloaded files using digital signatures
- Implement automatic updates to ensure devices are always running the latest secure versions
By following these best practices, you can minimize the risk of downloading malicious software or firmware that could compromise your IoT ecosystem.
Best Practices for IoT Security
Regular Security Audits
Conducting regular security audits is essential for identifying and addressing vulnerabilities in your IoT network. When securely connect remote IoT VPC Raspberry Pi, schedule periodic audits to ensure compliance with security standards.
Incident Response Planning
- Develop a comprehensive incident response plan to address security breaches
- Train personnel to recognize and respond to potential threats
Having a well-defined incident response plan can significantly reduce the impact of security incidents and ensure a swift recovery.
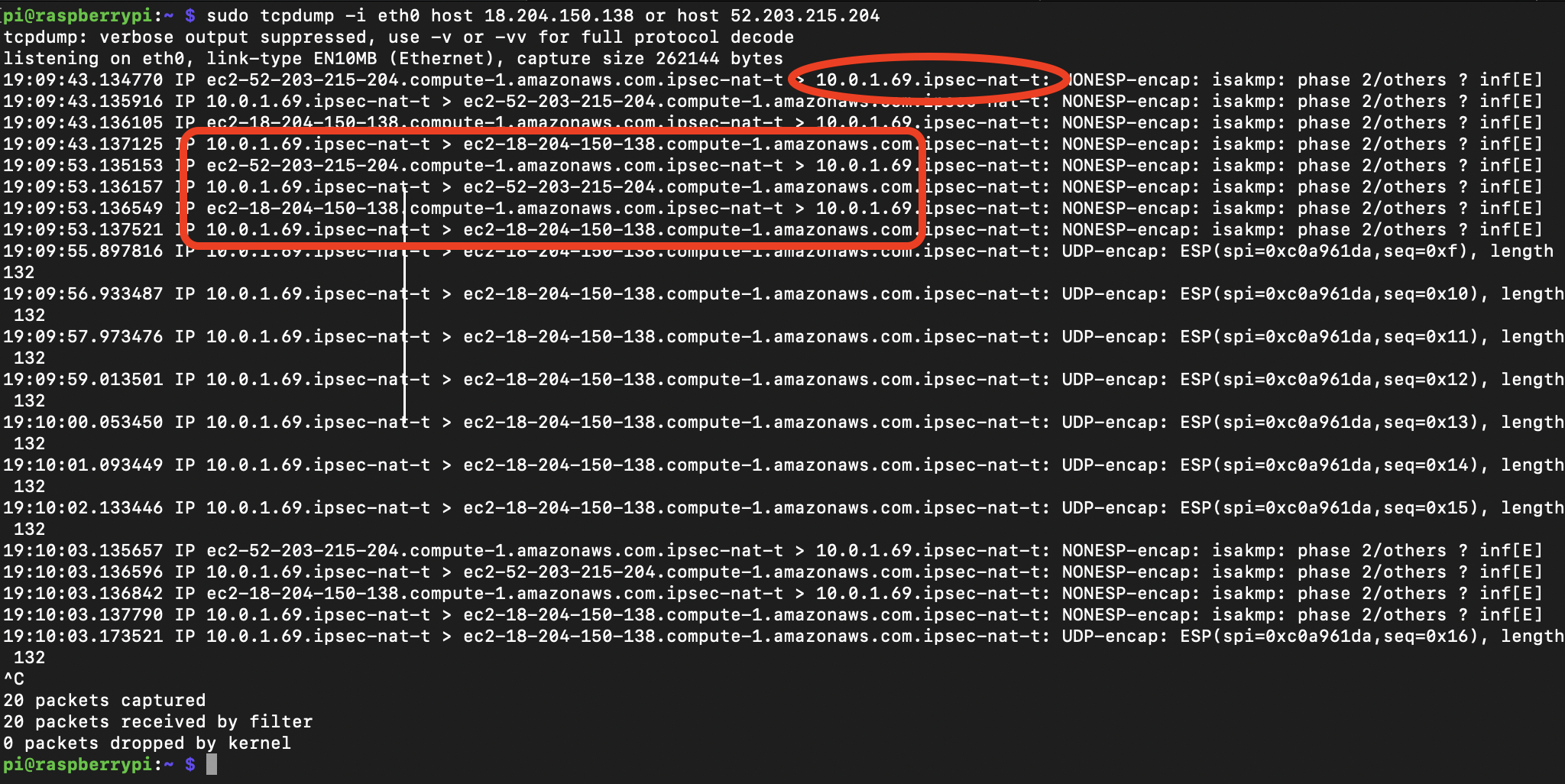
Troubleshooting Common IoT Security Issues
Despite best efforts, security issues can still arise in IoT networks. When securely connect remote IoT VPC Raspberry Pi, be prepared to troubleshoot common problems such as unauthorized access, network outages, and device malfunctions.
Common Troubleshooting Steps
- Check firewall rules and access permissions
- Inspect device logs for signs of suspicious activity
- Update firmware and software to the latest versions
Addressing these issues promptly can prevent minor problems from escalating into major security breaches.
Data Protection and Privacy in IoT
Data protection and privacy are critical considerations in IoT deployments. When securely connect remote IoT VPC Raspberry Pi, implement robust data protection measures to safeguard sensitive information.
Data Encryption
- Encrypt data both in transit and at rest to prevent unauthorized access
- Use strong encryption algorithms such as AES-256
Data encryption is a fundamental aspect of IoT security, ensuring that even if data is intercepted, it remains unreadable to unauthorized parties.
Future Trends in IoT Security
The future of IoT security lies in emerging technologies such as artificial intelligence (AI), blockchain, and quantum cryptography. These technologies offer innovative solutions for securely connect remote IoT VPC Raspberry Pi and enhancing overall network security.
AI-Driven Security
AI can analyze vast amounts of data to detect anomalies and predict potential security threats. By integrating AI into IoT security systems, you can achieve proactive threat detection and response.
Blockchain for Data Integrity
Blockchain technology provides a decentralized and tamper-proof ledger for recording transactions. It can be used to ensure the integrity of data exchanged between IoT devices.
Conclusion
Securing IoT networks is a complex but essential task in today's digital age. By following the best practices outlined in this article, you can securely connect remote IoT VPC Raspberry Pi and protect your IoT ecosystem from potential threats. Remember to conduct regular security audits, implement data encryption, and stay updated with the latest trends in IoT security.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site for more insights into IoT security and related topics. Together, let's build a safer and more secure digital future.