In today's interconnected world, mastering SSH (Secure Shell) for remote IoT operations on a Mac is more critical than ever. Whether you're a hobbyist or a professional, understanding how to use SSH remote IoT on Mac for free can significantly enhance your ability to manage devices remotely. This guide aims to simplify the process while providing actionable insights for beginners and advanced users alike.
SSH is a powerful tool that allows secure communication between devices over a network. By learning how to use SSH remote IoT on Mac, you gain the ability to control and manage IoT devices from anywhere in the world, ensuring efficiency and convenience in your workflow.
Throughout this article, we'll explore step-by-step instructions, troubleshooting tips, and best practices to help you master SSH remote IoT on Mac for free. Let's dive in and unlock the full potential of secure remote access.
Read also:Bruce Willis The Iconic Action Hero Who Shaped Modern Cinema
Table of Contents
- Introduction to SSH
- Why Use SSH for Remote IoT
- Prerequisites for Using SSH on Mac
- Step-by-Step Guide to Use SSH Remote IoT on Mac
- Best Practices for SSH Remote IoT
- Troubleshooting Common Issues
- Security Tips for SSH Connections
- Alternative Tools for Remote IoT Management
- Frequently Asked Questions
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a network protocol that provides encrypted communication between devices. It is widely used for remote login and other secure network services over an unsecured network. By leveraging SSH, you can securely access and manage IoT devices from your Mac without worrying about data interception or unauthorized access.
SSH is particularly useful for IoT applications because it ensures secure data transmission, even when devices are located in different geographic locations. Whether you're managing a smart home system, industrial sensors, or cloud-based applications, SSH provides the reliability and security you need.
One of the key advantages of SSH is its ability to operate on virtually any platform, including macOS, Linux, and Windows. This cross-platform compatibility makes it an essential tool for anyone working in the IoT space.
Why Use SSH for Remote IoT
Using SSH for remote IoT management offers several benefits, including:
- Security: SSH encrypts all data transmitted between devices, protecting sensitive information from cyber threats.
- Reliability: SSH ensures stable connections, even in challenging network conditions.
- Flexibility: SSH supports a wide range of commands and applications, making it suitable for various IoT use cases.
- Cost-Effectiveness: SSH is free to use and does not require additional licensing fees, making it an ideal choice for budget-conscious users.
By mastering SSH remote IoT on Mac, you can streamline your workflow and enhance the security of your IoT ecosystem.
Prerequisites for Using SSH on Mac
Before diving into the process, ensure that you have the following prerequisites in place:
Read also:Tyus Jones The Rising Star In Professional Basketball
- A Mac computer with macOS installed.
- An IoT device with SSH server functionality enabled.
- A stable internet connection for remote access.
- Basic knowledge of terminal commands and networking concepts.
Having these prerequisites in place will ensure a smooth setup and operation process.
Step-by-Step Guide to Use SSH Remote IoT on Mac
Step 1: Enable SSH on Your Mac
To begin, you need to enable SSH on your Mac. Follow these steps:
- Open System Preferences on your Mac.
- Click on Sharing.
- In the left-hand menu, check the box for Remote Login.
- Confirm that SSH is enabled by checking the message displayed below the checkbox.
Once SSH is enabled, your Mac is ready to act as a client for remote IoT connections.
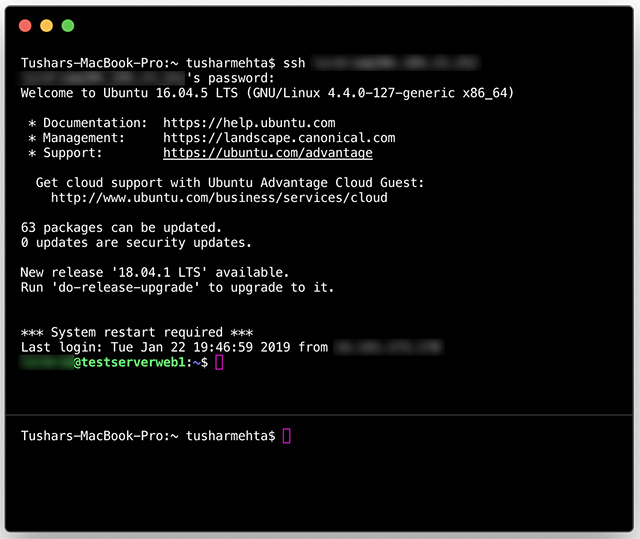
Step 2: Connect to a Remote IoT Device
Connecting to a remote IoT device involves the following steps:
- Open the Terminal application on your Mac.
- Type the following command:
ssh username@IP_address, replacingusernamewith the login name for the remote device andIP_addresswith the device's IP address. - Press Enter and provide the password when prompted.
- Once connected, you can execute commands on the remote device as if you were physically present.
For example, if your IoT device's IP address is 192.168.1.100 and the username is "admin," the command would look like this: ssh admin@192.168.1.100.
Step 3: Secure Your SSH Connection
Securing your SSH connection is crucial to protect against unauthorized access. Consider implementing the following measures:
- Use Strong Passwords: Ensure that your login credentials are complex and not easily guessable.
- Enable Key-Based Authentication: Replace password-based authentication with SSH keys for added security.
- Update Software Regularly: Keep your Mac and IoT devices up to date with the latest security patches.
- Limit Access: Restrict SSH access to specific IP addresses or networks to minimize exposure.
By following these best practices, you can significantly enhance the security of your SSH connections.
Best Practices for SSH Remote IoT
Here are some additional best practices to consider when using SSH for remote IoT management:
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities.
- Disable Root Login: Prevent direct login as the root user to reduce the risk of unauthorized access.
- Use Non-Standard Ports: Change the default SSH port (22) to a custom port to deter automated attacks.
- Implement Firewalls: Use firewalls to control incoming and outgoing traffic to your SSH server.
Adhering to these practices will help you maintain a secure and efficient SSH remote IoT setup.
Troubleshooting Common Issues
Even with proper setup, issues may arise when using SSH remote IoT on Mac. Here are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is running on the remote device and that the IP address is correct.
- Authentication Failed: Double-check your login credentials and ensure that key-based authentication is properly configured.
- Timeout Errors: Verify that your network connection is stable and that no firewalls are blocking the SSH port.
If problems persist, consult the official documentation for your IoT device or seek assistance from community forums.
Security Tips for SSH Connections
Security should always be a top priority when using SSH for remote IoT management. Here are some tips to enhance your security:
- Use Two-Factor Authentication: Add an extra layer of security by enabling two-factor authentication for SSH connections.
- Restrict User Permissions: Assign appropriate permissions to users to prevent unauthorized access to sensitive data.
- Regularly Audit Connections: Periodically review active SSH sessions to identify and terminate suspicious connections.
By implementing these security measures, you can protect your IoT devices and maintain the integrity of your network.
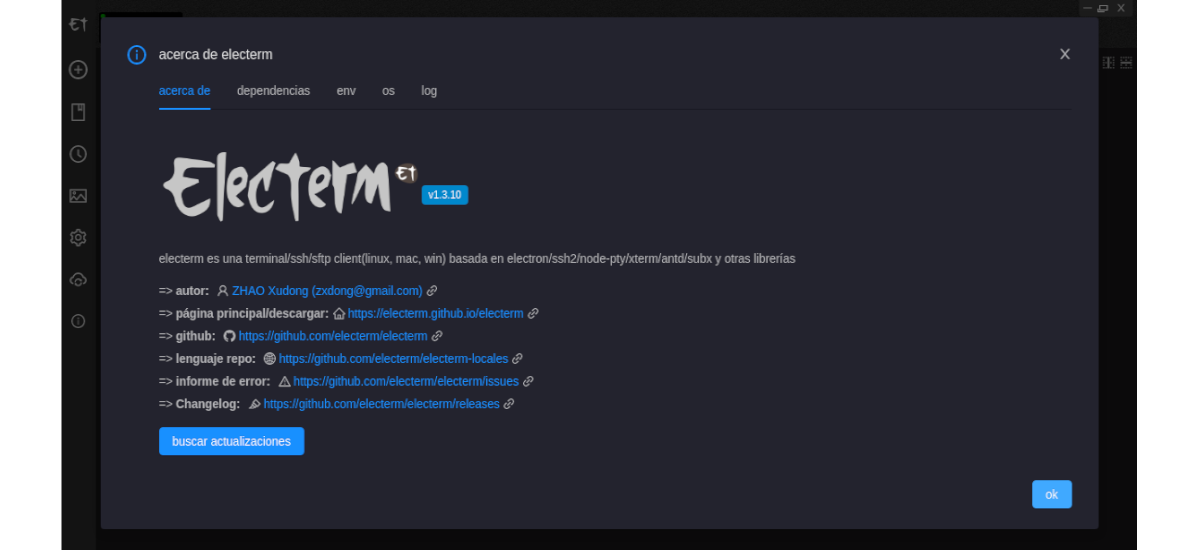
Alternative Tools for Remote IoT Management
While SSH is a powerful tool, there are alternative solutions for remote IoT management, including:
- SecureCRT: A commercial SSH client with advanced features for managing remote devices.
- PuTTY: A free and open-source SSH client widely used in the Windows environment.
- Mosh (Mobile Shell):** A modern alternative to SSH that supports intermittent connectivity.
Consider exploring these tools to find the best fit for your specific needs and preferences.
Frequently Asked Questions
1. Can I Use SSH on a Mac for Free?
Yes, SSH is a built-in feature of macOS, meaning you can use it for free without any additional costs.
2. Is SSH Secure for IoT Devices?
SSH is highly secure for IoT devices when properly configured. It encrypts all data transmissions and supports advanced security features like key-based authentication.
3. Can I Automate SSH Connections?
Yes, you can automate SSH connections using scripts and tools like Ansible or Fabric. This is particularly useful for managing multiple IoT devices simultaneously.
Conclusion
Learning how to use SSH remote IoT on Mac for free opens up a world of possibilities for managing and controlling IoT devices from anywhere in the world. By following the steps outlined in this guide, you can set up a secure and reliable SSH connection while adhering to best practices and security recommendations.
We encourage you to experiment with SSH and explore its capabilities further. If you found this article helpful, please share it with others who might benefit from it. Additionally, feel free to leave a comment below with any questions or feedback you may have.
Stay connected and continue exploring the exciting world of IoT and remote management!