In today's digital era, finding the best SSH RemoteIoT solutions has become crucial for businesses and individuals looking to enhance their remote connectivity and security. With the increasing reliance on IoT devices and remote operations, understanding and implementing the right tools can significantly improve productivity while safeguarding sensitive data. In this article, we will explore the top SSH RemoteIoT solutions, their features, and how they can benefit your operations.
Remote connectivity has transformed how we interact with devices and systems, enabling seamless communication between devices regardless of geographical location. Secure Shell (SSH) plays a pivotal role in ensuring secure access to remote servers and IoT devices, making it a critical component of modern network infrastructure.
Whether you're a developer, IT professional, or a business owner, having access to reliable SSH RemoteIoT solutions can enhance your ability to manage and control connected devices. This article will provide a comprehensive overview of the best SSH RemoteIoT options available, helping you make informed decisions for your specific needs.
Read also:Alec Baldwin Wife A Comprehensive Look Into Her Life Career And Marriage
Table of Contents
- Introduction to SSH RemoteIoT
- Why Choose SSH for RemoteIoT?
- Top SSH RemoteIoT Solutions
- Benefits of SSH RemoteIoT
- Security Features of SSH RemoteIoT
- How to Implement SSH RemoteIoT
- Common Challenges and Solutions
- Comparison of SSH RemoteIoT Solutions
- Future Trends in SSH RemoteIoT
- Conclusion and Next Steps
Introduction to SSH RemoteIoT
SSH RemoteIoT refers to the integration of Secure Shell (SSH) protocols with Internet of Things (IoT) devices to enable secure remote access and management. This technology allows users to control and interact with IoT devices from remote locations without compromising security or performance. As the number of IoT devices continues to grow, the demand for secure and reliable remote access solutions has become more pronounced.
The best SSH RemoteIoT solutions combine robust encryption, authentication mechanisms, and user-friendly interfaces to ensure seamless connectivity. These solutions are designed to cater to a wide range of industries, including healthcare, manufacturing, and smart home automation, making them versatile and adaptable to various use cases.
Understanding SSH Protocol
Secure Shell (SSH) is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It provides a secure channel for data transfer, command execution, and file management, making it an ideal choice for remote IoT applications. SSH employs strong encryption algorithms and authentication methods to protect against unauthorized access and data breaches.
Why Choose SSH for RemoteIoT?
There are several reasons why SSH is the preferred choice for remote IoT applications. Firstly, its robust security features ensure that data transmitted between devices remains confidential and tamper-proof. Secondly, SSH supports various authentication methods, including password-based and public-key authentication, providing flexibility in user access management.
Additionally, SSH is widely supported across different platforms and operating systems, making it easy to integrate with existing IoT infrastructure. Its open-source nature also allows developers to customize and extend its functionality to meet specific requirements.
Key Features of SSH for RemoteIoT
- End-to-end encryption for secure communication
- Support for multiple authentication methods
- Platform independence and compatibility
- Customizable and extensible architecture
Top SSH RemoteIoT Solutions
Several SSH RemoteIoT solutions are available in the market, each offering unique features and capabilities. Below are some of the best SSH RemoteIoT solutions that you can consider for your remote connectivity needs:
Read also:Why Liberty University Stands Out A Comprehensive Guide For Future Students
1. OpenSSH
OpenSSH is one of the most popular and widely used SSH implementations, known for its reliability and security. It provides a comprehensive suite of tools for secure remote access and file transfer, making it an excellent choice for IoT applications. OpenSSH is open-source and supports a wide range of platforms, including Linux, macOS, and Windows.
2. Bitvise SSH Client
Bitvise SSH Client is a powerful and user-friendly SSH solution that offers advanced features such as port forwarding, tunneling, and SFTP support. It is particularly well-suited for enterprise environments where secure remote access is critical. Bitvise provides both free and paid versions, catering to different user needs.
3. PuTTY
PuTTY is a lightweight and portable SSH client that is widely used for remote access to IoT devices. It supports multiple protocols, including SSH, Telnet, and Rlogin, making it versatile and adaptable to various use cases. PuTTY is free and open-source, making it accessible to users of all levels.
Benefits of SSH RemoteIoT
Implementing SSH RemoteIoT solutions offers numerous benefits, including enhanced security, improved productivity, and cost savings. By leveraging SSH, organizations can ensure that their IoT devices are securely managed and monitored, reducing the risk of cyberattacks and data breaches.
Additionally, SSH RemoteIoT solutions enable users to perform remote troubleshooting and maintenance, minimizing downtime and improving operational efficiency. The ability to access and control IoT devices from anywhere in the world also provides flexibility and convenience, making it easier for businesses to scale their operations.
Key Benefits
- Enhanced security and data protection
- Improved productivity and operational efficiency
- Reduced downtime and maintenance costs
- Flexibility and scalability for global operations
Security Features of SSH RemoteIoT
Security is a critical aspect of SSH RemoteIoT solutions, and several features contribute to their robust protection. These include strong encryption algorithms, secure authentication mechanisms, and access control policies. SSH employs encryption protocols such as AES and RSA to secure data transmission, ensuring that sensitive information remains confidential.
Authentication methods like public-key cryptography and two-factor authentication further enhance security by verifying the identity of users before granting access. Additionally, SSH RemoteIoT solutions often include logging and auditing capabilities, allowing administrators to monitor and track access attempts for better security management.
Encryption Standards
SSH RemoteIoT solutions utilize industry-standard encryption protocols to protect data in transit. These include:
- AES (Advanced Encryption Standard)
- DES (Data Encryption Standard)
- Blowfish
- RSA (Rivest-Shamir-Adleman)
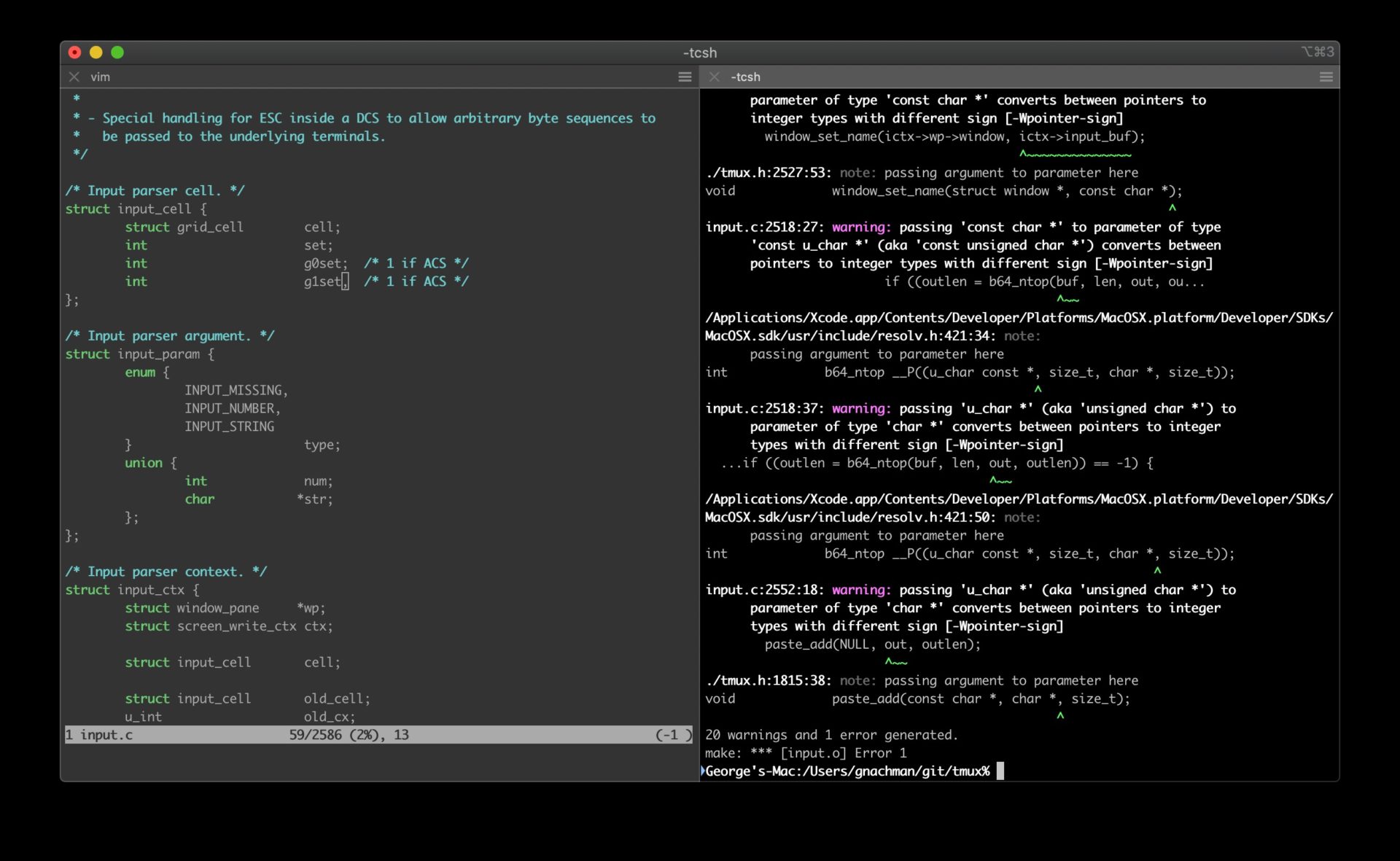
How to Implement SSH RemoteIoT
Implementing SSH RemoteIoT solutions involves several steps, starting with selecting the right tools and configuring them to meet your specific requirements. Below is a step-by-step guide to help you set up SSH RemoteIoT:
Step 1: Choose the Right SSH Client
Select an SSH client that supports your platform and offers the features you need. Popular options include OpenSSH, Bitvise SSH Client, and PuTTY.
Step 2: Configure SSH Server
Set up an SSH server on your IoT devices to enable remote access. This involves installing the necessary software and configuring security settings such as port numbers, authentication methods, and access controls.
Step 3: Test and Optimize
Once the SSH server is configured, test the connection to ensure it works as expected. Optimize settings for performance and security, and regularly update software to address vulnerabilities.
Common Challenges and Solutions
While SSH RemoteIoT solutions offer numerous benefits, they also come with challenges that need to be addressed. Some common challenges include:
Challenge 1: Security Vulnerabilities
SSH servers can be vulnerable to brute-force attacks and other security threats if not properly configured. To mitigate these risks, implement strong password policies, enable two-factor authentication, and regularly update software to patch vulnerabilities.
Challenge 2: Performance Issues
Remote IoT connections can suffer from latency and bandwidth limitations, affecting performance. To address this, optimize SSH settings for speed and efficiency, and use compression techniques to reduce data transfer overhead.
Comparison of SSH RemoteIoT Solutions
When choosing an SSH RemoteIoT solution, it's important to compare different options based on their features, pricing, and compatibility. Below is a comparison of some popular SSH RemoteIoT solutions:
| Solution | Features | Pricing | Compatibility |
|---|---|---|---|
| OpenSSH | Free, open-source, versatile | Free | Linux, macOS, Windows |
| Bitvise SSH Client | Advanced features, enterprise-ready | Free and paid versions | Windows |
| PuTTY | Lightweight, portable, multi-protocol | Free | Windows, Linux |
Future Trends in SSH RemoteIoT
The future of SSH RemoteIoT looks promising, with advancements in technology driving innovation and improvement. Some emerging trends include:
Trend 1: Quantum-Resistant Encryption
As quantum computing becomes more prevalent, there is a growing need for encryption methods that can withstand quantum attacks. SSH RemoteIoT solutions are likely to adopt quantum-resistant algorithms to ensure long-term security.
Trend 2: AI-Driven Security
Artificial intelligence and machine learning are being integrated into SSH RemoteIoT solutions to enhance security by detecting and responding to threats in real-time. These technologies can analyze patterns and anomalies to identify potential security breaches before they occur.
Conclusion and Next Steps
SSH RemoteIoT solutions offer a secure and efficient way to manage and interact with IoT devices remotely. By understanding the features and benefits of these solutions, you can make informed decisions to enhance your remote connectivity and security. As technology continues to evolve, staying updated with the latest trends and advancements will be crucial for maintaining a competitive edge.
We encourage you to explore the best SSH RemoteIoT solutions available and implement them in your operations. Don't forget to share your thoughts and experiences in the comments section below, and consider subscribing to our newsletter for more insightful content. Together, let's build a secure and connected future!