Setting up SSH remote access on your Raspberry Pi is a game-changer for IoT enthusiasts and developers. Whether you're managing a home automation system or deploying a remote sensor network, SSH provides secure and reliable access to your device from anywhere in the world.
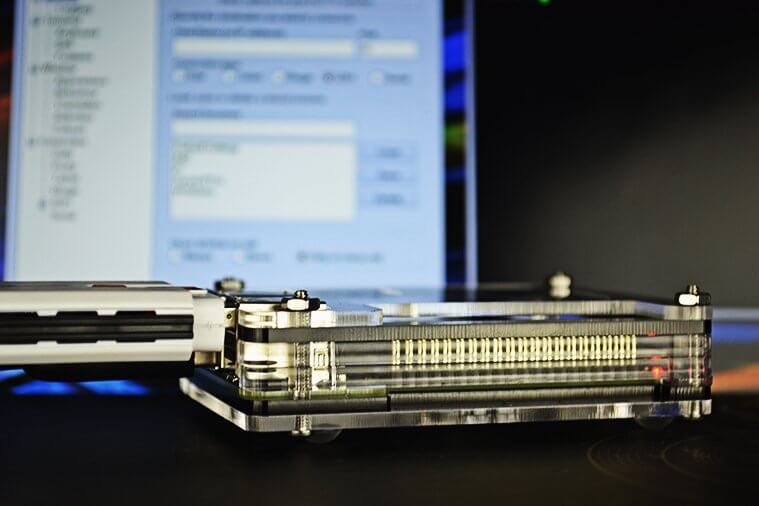
In today's connected world, the Internet of Things (IoT) has revolutionized how we interact with technology. At the heart of many IoT projects lies the versatile Raspberry Pi, a compact and affordable single-board computer. One of the most powerful tools for managing your Raspberry Pi remotely is Secure Shell (SSH).
This comprehensive guide will walk you through everything you need to know about setting up SSH for remote access on your Raspberry Pi, including tips for securing your connection, troubleshooting common issues, and optimizing performance for IoT applications.
Read also:Social Security Identity Verification A Comprehensive Guide To Protecting Your Identity
Table of Contents:
- Introduction to SSH and Raspberry Pi
- Understanding SSH in IoT Context
- Setting Up SSH on Raspberry Pi
- Securing Your SSH Connection
- Troubleshooting SSH Issues
- Optimizing SSH for IoT
- Alternatives to SSH for Raspberry Pi
- Real-World IoT Applications
- The Future of SSH in IoT
- Conclusion and Next Steps
Introduction to SSH and Raspberry Pi
Secure Shell (SSH) is a network protocol that allows you to securely connect to and manage remote devices, such as your Raspberry Pi. For IoT enthusiasts, this means you can control your Raspberry Pi-based projects without being physically present.
SSH provides encryption for data transfer, ensuring that your commands and sensitive information remain private. This is especially important when managing IoT devices in public or unsecured networks. By setting up SSH on your Raspberry Pi, you gain the flexibility to monitor and manage your projects from anywhere with an internet connection.
Whether you're configuring sensors, updating software, or troubleshooting issues, SSH simplifies the process and enhances productivity. In this guide, we'll explore how to set up SSH on your Raspberry Pi, secure your connection, and optimize it for IoT applications.
Understanding SSH in IoT Context
What Makes SSH Ideal for IoT?
SSH is widely regarded as one of the most reliable protocols for remote access due to its robust security features. In the context of IoT, where devices are often deployed in remote or inaccessible locations, SSH offers several advantages:
- Encrypted communication to protect sensitive data.
- Platform independence, allowing you to connect from virtually any device.
- Scripting capabilities for automating tasks and monitoring devices.
For Raspberry Pi users, SSH eliminates the need for a monitor, keyboard, or mouse, making it an essential tool for headless operation.
Read also:Cruz Azul Vs Leon The Rivalry That Defines Mexican Football
Setting Up SSH on Raspberry Pi
Step-by-Step Guide
Setting up SSH on your Raspberry Pi is straightforward and can be done in a few simple steps:
- Enable SSH on your Raspberry Pi using the Raspberry Pi Configuration tool or by editing the
/boot/config.txtfile. - Connect your Raspberry Pi to the same network as your computer.
- Find the IP address of your Raspberry Pi using the
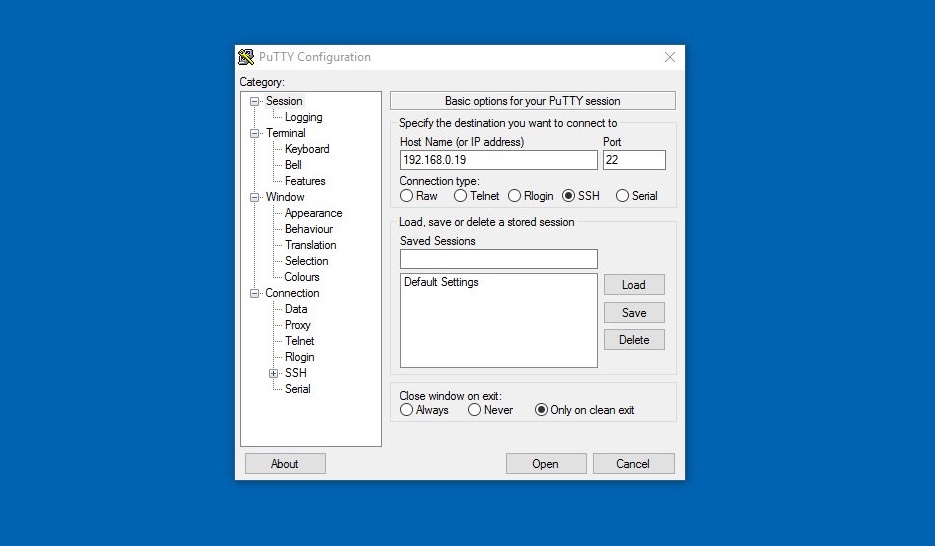
ifconfigorip addrcommand. - Use an SSH client, such as PuTTY (Windows) or Terminal (Mac/Linux), to connect to your Raspberry Pi using its IP address.
Once connected, you can execute commands, transfer files, and manage your Raspberry Pi remotely.
Securing Your SSH Connection
Best Practices for SSH Security
While SSH is inherently secure, additional measures can further protect your Raspberry Pi from unauthorized access:
- Change the default SSH port (22) to a non-standard port.
- Use strong, unique passwords or public key authentication for SSH login.
- Disable root login to prevent brute-force attacks.
- Implement firewall rules to restrict access to your SSH server.
By following these best practices, you can ensure that your Raspberry Pi remains secure even when accessed remotely.
Troubleshooting SSH Issues
Common Problems and Solutions
Despite its reliability, SSH connections can sometimes fail due to various reasons. Here are some common issues and their solutions:
- Connection Refused: Ensure that SSH is enabled and the Raspberry Pi is connected to the correct network.
- Authentication Failed: Double-check your username, password, and public key configuration.
- Timeout Errors: Verify that your firewall settings allow SSH traffic on the specified port.
For persistent issues, consult the Raspberry Pi documentation or community forums for additional support.
Optimizing SSH for IoT
Tips for Efficient SSH Usage
To get the most out of SSH for your IoT projects, consider the following optimization tips:
- Use compression to reduce bandwidth usage during file transfers.
- Enable keepalive packets to maintain a stable connection.
- Automate routine tasks with shell scripts to minimize manual intervention.
These optimizations not only improve performance but also enhance the reliability of your SSH-based IoT systems.
Alternatives to SSH for Raspberry Pi
Exploring Other Remote Access Options
While SSH is the most popular choice for remote access, there are alternative methods worth considering:
- VNC (Virtual Network Computing): Provides a graphical interface for remote management.
- Web-Based Interfaces: Ideal for web applications running on your Raspberry Pi.
- Third-Party Services: Solutions like ngrok or remot3.it offer cloud-based access without port forwarding.
Each option has its own advantages and limitations, so choose the one that best fits your specific needs.
Real-World IoT Applications
How SSH Powers IoT Projects
SSH plays a crucial role in many IoT applications, including:
- Home automation systems, where SSH enables remote control of smart devices.
- Environmental monitoring, where SSH facilitates data retrieval from remote sensors.
- Industrial automation, where SSH supports secure communication between machines.
By leveraging SSH, developers can build robust and scalable IoT solutions that meet the demands of modern applications.
The Future of SSH in IoT
Emerging Trends and Technologies
As IoT continues to evolve, SSH will remain a vital tool for remote access and management. Future developments may include:
- Enhanced encryption algorithms for improved security.
- Integration with AI-powered systems for automated decision-making.
- Support for emerging protocols and standards in IoT communication.
Staying informed about these advancements will help you make the most of SSH in your IoT projects.
Conclusion and Next Steps
In conclusion, SSH is an indispensable tool for anyone working with Raspberry Pi in IoT projects. By setting up SSH correctly, securing your connection, and optimizing performance, you can unlock the full potential of your IoT systems. Remember to explore alternative methods and stay updated on the latest trends in IoT technology.
We invite you to share your experiences with SSH and Raspberry Pi in the comments below. Feel free to ask questions or suggest topics for future articles. Don't forget to subscribe to our newsletter for the latest updates and tutorials on IoT and related technologies. Together, let's build a smarter, more connected world!
References:
- Raspberry Pi Documentation: https://www.raspberrypi.org/documentation/
- SSH Official Website: https://www.ssh.com/
- IoT Journal: https://www.iotjournal.com/