In today's interconnected world, securely connecting remote IoT devices to a Virtual Private Cloud (VPC) through a Raspberry Pi has become an essential skill for developers and IT professionals. As the Internet of Things (IoT) continues to grow, ensuring secure communication between devices and networks is paramount. This article will guide you through the process of setting up a secure connection for your IoT devices using a Raspberry Pi as a gateway to your VPC.
Whether you're managing smart home devices, industrial sensors, or any other IoT infrastructure, the ability to establish a secure connection is crucial. Without proper security measures, sensitive data could be exposed to unauthorized access, leading to potential breaches and vulnerabilities. This guide aims to provide you with step-by-step instructions and expert advice to help you achieve a secure IoT VPC connection using Raspberry Pi.
By the end of this article, you'll have a solid understanding of the best practices, tools, and configurations needed to secure your IoT ecosystem. We'll cover everything from network architecture to encryption protocols, ensuring that your remote IoT devices remain protected while communicating with your cloud resources.
Read also:Grizzlies Vs Trail Blazers A Deep Dive Into The Thrilling Nba Rivalry
Table of Contents
- Introduction to Secure IoT VPC Connections
- Overview of Raspberry Pi as an IoT Gateway
- Setting Up a Virtual Private Cloud (VPC)
- Securing the Connection Between IoT Devices and VPC
- Importance of Encryption in IoT Communication
- Network Security Best Practices
- Configuring Firewalls for Enhanced Security
- Monitoring and Managing IoT Devices
- Troubleshooting Common Issues
- Conclusion and Next Steps
Introduction to Secure IoT VPC Connections
Understanding IoT and Its Challenges
IoT devices are transforming industries by enabling real-time data collection and automation. However, the rapid expansion of IoT ecosystems has introduced significant security challenges. One of the primary concerns is securing the communication between remote IoT devices and centralized cloud services. A Virtual Private Cloud (VPC) provides a secure and isolated environment for hosting these services, but connecting IoT devices to it requires careful planning and implementation.
Why Use Raspberry Pi?
Raspberry Pi serves as an excellent platform for IoT gateways due to its affordability, flexibility, and ease of use. By leveraging Raspberry Pi, you can create a robust and secure bridge between your IoT devices and VPC. Its compatibility with various operating systems and programming languages makes it an ideal choice for developers working on IoT projects.
Key Benefits of Secure IoT VPC Connections
Securing your IoT devices with a VPC offers several advantages, including:
- Enhanced data protection
- Reduced risk of unauthorized access
- Improved network performance
- Centralized management of devices
Overview of Raspberry Pi as an IoT Gateway
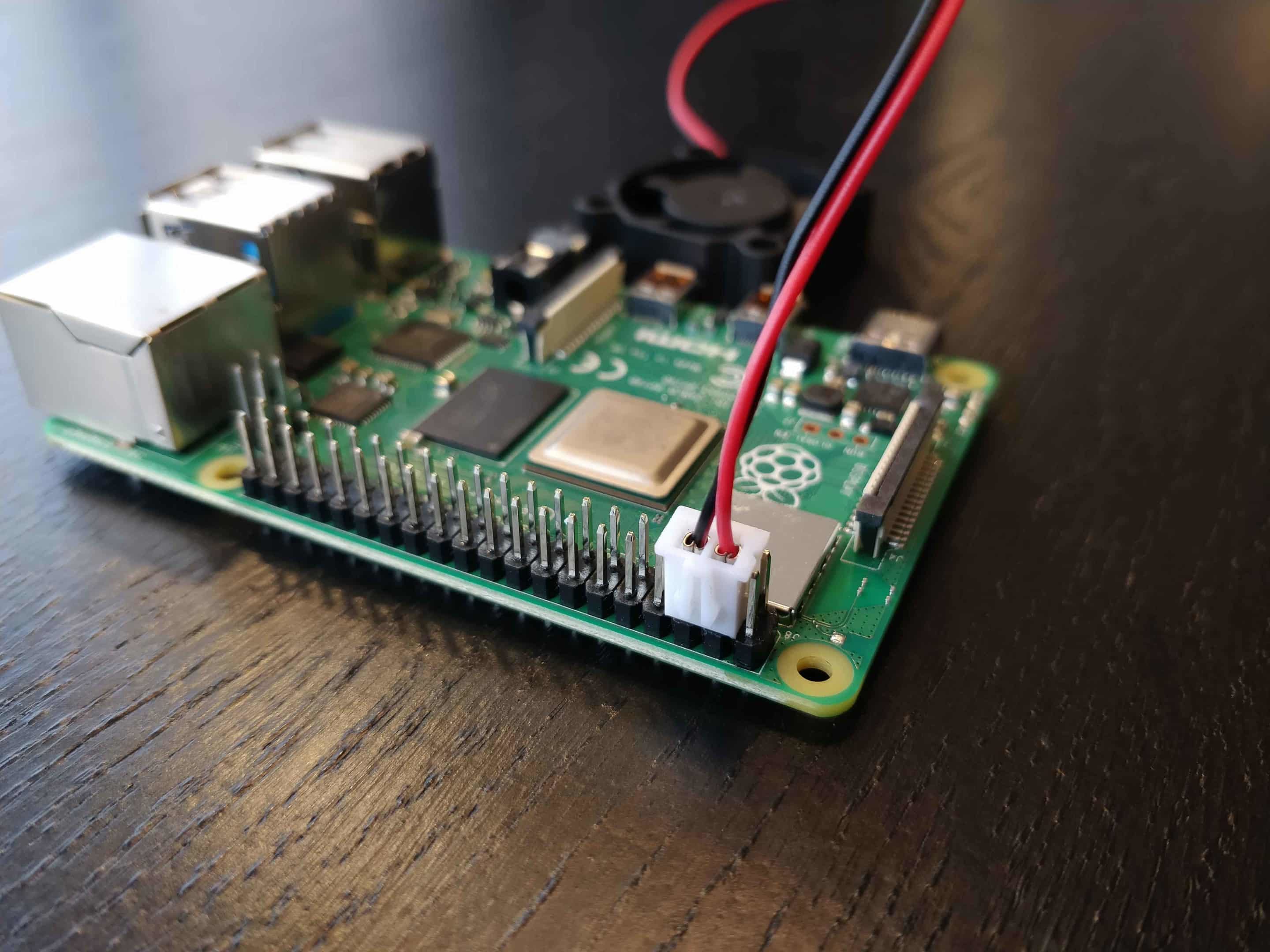
Raspberry Pi is a versatile single-board computer that has gained immense popularity in the IoT community. Its low power consumption, compact size, and extensive community support make it an ideal choice for IoT gateway applications. When used as a gateway, Raspberry Pi acts as an intermediary between IoT devices and cloud services, ensuring secure and reliable communication.
Hardware Specifications
Before proceeding, ensure your Raspberry Pi meets the following specifications:
- Model: Raspberry Pi 4 or higher
- RAM: 4GB or more
- Storage: MicroSD card with at least 16GB capacity
- Network: Ethernet or Wi-Fi capability
Software Setup
Install a lightweight Linux distribution such as Raspbian or Ubuntu Server on your Raspberry Pi. These operating systems provide the necessary tools and libraries for setting up secure IoT connections. Additionally, consider using containerization platforms like Docker to isolate services and enhance security.
Read also:Michael Porter Jr Rising Star In The Nba With Incredible Potential
Setting Up a Virtual Private Cloud (VPC)
A VPC is a virtual network dedicated to your cloud resources, providing a secure and isolated environment for hosting your IoT applications. Setting up a VPC involves several steps, including defining subnets, configuring security groups, and establishing network access rules.
Steps to Create a VPC
- Log in to your cloud provider's management console (e.g., AWS, Azure, or Google Cloud).
- Create a new VPC and specify its IP address range.
- Define subnets for different regions or zones within your VPC.
- Set up security groups to control inbound and outbound traffic.
- Configure routing tables to ensure proper communication between subnets.
Securing the Connection Between IoT Devices and VPC
Establishing a secure connection between IoT devices and VPC requires implementing robust authentication and encryption mechanisms. This section outlines the key steps to achieve a secure connection.
Authentication Methods
Choose an appropriate authentication method for your IoT devices, such as:
- Username and password
- API keys
- Certificates
Encryption Protocols
Use industry-standard encryption protocols to protect data in transit, such as:
- Transport Layer Security (TLS)
- Secure Sockets Layer (SSL)
- Internet Protocol Security (IPsec)
Importance of Encryption in IoT Communication
Encryption plays a critical role in securing IoT communication by ensuring data confidentiality and integrity. Without encryption, sensitive information transmitted between IoT devices and VPC could be intercepted and misused by malicious actors.
Benefits of Encryption
- Protects data from unauthorized access
- Ensures data integrity during transmission
- Builds trust with end-users
Network Security Best Practices
Implementing network security best practices is essential for safeguarding your IoT ecosystem. This includes regular updates, access controls, and monitoring.
Regular Updates
Keep your Raspberry Pi and IoT devices up to date with the latest firmware and software patches to address known vulnerabilities.
Access Controls
Limit access to your VPC and IoT devices by implementing role-based access control (RBAC) and multi-factor authentication (MFA).
Configuring Firewalls for Enhanced Security
Firewalls act as a barrier between your IoT devices and external networks, filtering traffic based on predefined rules. Configuring firewalls correctly is crucial for maintaining a secure IoT environment.
Firewall Rules
Set up firewall rules to allow only necessary traffic to pass through, such as:
- Restricting incoming connections to specific IP addresses
- Blocking unauthorized outbound traffic
- Enabling logging for monitoring purposes
Monitoring and Managing IoT Devices
Monitoring your IoT devices is essential for detecting and responding to security incidents promptly. Use monitoring tools to track device performance, network activity, and security events.
Monitoring Tools
Consider using the following tools for monitoring your IoT devices:
- Prometheus
- Grafana
- Splunk
Troubleshooting Common Issues
Despite taking precautions, issues may arise when setting up a secure IoT VPC connection. This section provides guidance on troubleshooting common problems.
Connection Issues
If you encounter connection issues, check the following:
- Network configuration
- Firewall settings
- Certificate validity
Conclusion and Next Steps
Securing the connection between remote IoT devices and a VPC using Raspberry Pi is a critical step in protecting your IoT ecosystem. By following the best practices outlined in this article, you can ensure that your devices remain safe from potential threats while maintaining optimal performance.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site to deepen your understanding of IoT security and related topics. Together, we can build a safer and more connected world.