In today's rapidly evolving technological landscape, managing SSH keys for remote IoT devices has become a critical component of cybersecurity. Organizations are increasingly relying on secure communication channels to protect their networks and sensitive data. Best RemoteIoT SSH key management practices ensure that devices remain secure while maintaining efficiency and scalability.
SSH (Secure Shell) keys are an essential tool for securely accessing remote devices without the need for passwords. However, managing these keys across multiple IoT devices can be challenging. This guide explores the best practices, tools, and strategies to effectively manage SSH keys for remote IoT devices, ensuring maximum security and operational efficiency.
Whether you're a network administrator, cybersecurity professional, or IT enthusiast, this article will provide you with actionable insights into the world of SSH key management. From understanding the basics to implementing advanced strategies, you'll discover everything you need to secure your IoT infrastructure.
Read also:Cia Unveiling The Role History And Impact Of The Central Intelligence Agency
Table of Contents
- Introduction to RemoteIoT SSH Key Management
- Importance of SSH Key Management
- Basics of SSH Keys
- Challenges in RemoteIoT SSH Key Management
- Best Practices for SSH Key Management
- Tools for Managing SSH Keys
- Security Considerations for RemoteIoT SSH Keys
- Scaling SSH Key Management for IoT Devices
- Automation in SSH Key Management
- Conclusion and Next Steps
Introduction to RemoteIoT SSH Key Management
RemoteIoT SSH key management refers to the process of securely creating, distributing, and managing SSH keys for IoT devices that operate remotely. As IoT adoption continues to grow, the number of connected devices increases exponentially, leading to a surge in security challenges. Organizations must implement robust SSH key management practices to protect their networks from unauthorized access and cyber threats.
SSH keys serve as a digital credential that allows secure communication between devices without the need for passwords. Proper management of these keys ensures that only authorized users and devices can access the network. Neglecting SSH key management can lead to vulnerabilities, making it easier for attackers to exploit weak or outdated keys.
Importance of SSH Key Management
SSH key management plays a vital role in maintaining the security and integrity of remote IoT networks. Without proper management, organizations risk exposing sensitive data and critical infrastructure to potential threats. Below are some reasons why SSH key management is crucial:
- Enhanced Security: SSH keys provide a more secure alternative to passwords, reducing the risk of brute-force attacks.
- Improved Efficiency: Automated key management eliminates the need for manual intervention, saving time and resources.
- Compliance: Many industries have strict regulations regarding data protection and network security, making SSH key management a compliance requirement.
- Scalability: As the number of IoT devices grows, effective SSH key management ensures that networks can scale without compromising security.
Basics of SSH Keys
What Are SSH Keys?
SSH keys are cryptographic keys used for authenticating secure connections between devices. They consist of two parts: a private key, which is kept secret and stored on the client side, and a public key, which is shared with the server. When a client attempts to connect to a server, the server verifies the client's identity by checking the public key against the private key.
How Do SSH Keys Work?
The process of using SSH keys involves the following steps:
- Key Generation: A pair of SSH keys (public and private) is generated using an SSH client.
- Key Distribution: The public key is copied to the server, allowing the server to recognize the client.
- Authentication: When the client attempts to connect, the server verifies the client's identity by comparing the public key with the private key.
Challenges in RemoteIoT SSH Key Management
Managing SSH keys for remote IoT devices comes with its own set of challenges. Below are some common obstacles organizations face:
Read also:Pistons Vs Heat The Ultimate Showdown In Nba History
- Key Rotation: Regularly updating SSH keys to ensure they remain secure can be time-consuming and complex.
- Key Inventory: Keeping track of all active SSH keys across multiple devices and servers can be challenging.
- Access Control: Ensuring that only authorized users and devices have access to SSH keys is critical for maintaining security.
- Scalability: As the number of IoT devices increases, managing SSH keys becomes more difficult, requiring scalable solutions.
Best Practices for SSH Key Management
1. Regular Key Rotation
Rotating SSH keys on a regular basis helps mitigate the risk of unauthorized access. Organizations should establish a key rotation schedule and automate the process where possible.
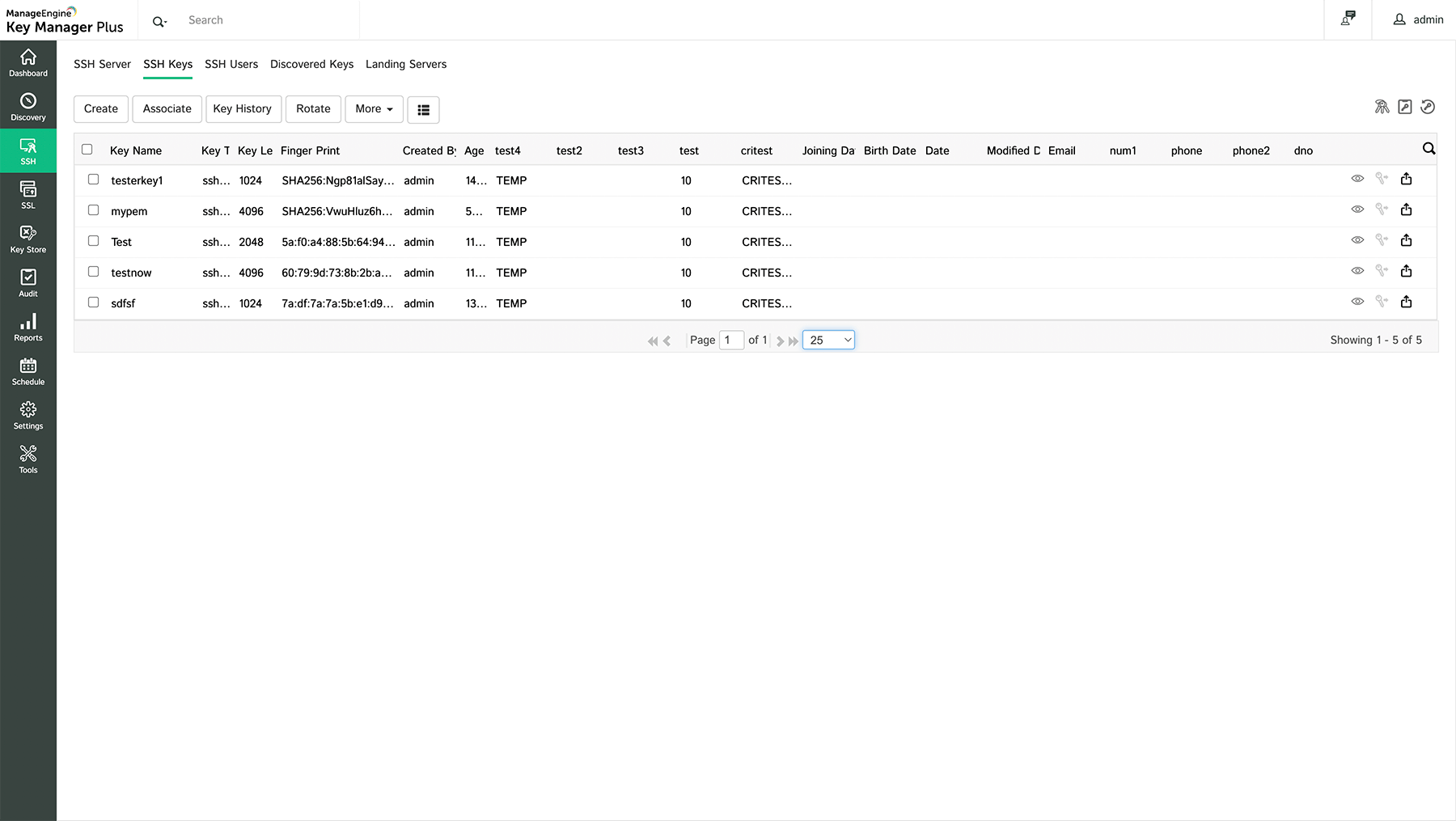
2. Centralized Key Management
Implementing a centralized SSH key management system allows organizations to monitor and control all SSH keys from a single location. This improves visibility and simplifies key management.
3. Access Control Policies
Enforcing strict access control policies ensures that only authorized users and devices can access SSH keys. Role-based access control (RBAC) is a popular method for managing permissions effectively.
Tools for Managing SSH Keys
Several tools are available to help organizations manage SSH keys efficiently. Below are some popular options:
- OpenSSH: A widely used open-source SSH implementation that includes tools for generating and managing SSH keys.
- HashiCorp Vault: A secure solution for storing and managing secrets, including SSH keys, with support for key rotation and access control.
- CyberArk: A comprehensive privileged access management solution that includes SSH key management capabilities.
Security Considerations for RemoteIoT SSH Keys
When managing SSH keys for remote IoT devices, organizations must consider several security factors:
- Key Storage: SSH keys should be stored securely, preferably in a hardware security module (HSM) or encrypted storage.
- Key Expiration: Setting an expiration date for SSH keys ensures that outdated keys are automatically removed from the system.
- Monitoring and Auditing: Regularly monitoring SSH key usage and auditing access logs helps identify potential security breaches.
Scaling SSH Key Management for IoT Devices
As the number of IoT devices grows, organizations must adopt scalable SSH key management solutions. Cloud-based platforms and automation tools can help streamline the process, ensuring that networks remain secure and efficient. Additionally, leveraging machine learning and artificial intelligence can enhance key management capabilities, providing real-time insights and predictive analytics.
Automation in SSH Key Management
Automation plays a crucial role in simplifying SSH key management for remote IoT devices. By automating tasks such as key generation, distribution, and rotation, organizations can reduce manual effort and minimize the risk of human error. Popular automation tools include Ansible, Puppet, and Chef, which offer robust SSH key management capabilities.
Conclusion and Next Steps
In conclusion, best remoteIoT SSH key management practices are essential for maintaining the security and efficiency of remote IoT networks. By implementing the strategies and tools discussed in this article, organizations can effectively manage SSH keys, ensuring that their networks remain protected against potential threats.
We encourage readers to take the following steps:
- Review your current SSH key management practices and identify areas for improvement.
- Explore the tools and solutions mentioned in this article to find the best fit for your organization.
- Stay informed about the latest trends and advancements in SSH key management to remain ahead of emerging threats.
Feel free to leave a comment or share this article with others who may benefit from the insights provided. For more information on cybersecurity and IoT, explore our other articles and resources.