Are you looking for a way to remotely access your Raspberry Pi IoT device using SSH with a free setup? In today's digital age, remote access to devices has become an essential skill for tech enthusiasts, hobbyists, and professionals alike. Whether you're managing home automation systems or building complex IoT solutions, understanding how to use SSH (Secure Shell) is crucial. This guide will walk you through the process step by step, ensuring you can download and set up SSH for your Raspberry Pi IoT device without any hassle.
SSH remote IoT device Raspberry Pi free download options are widely available, and setting up this system is easier than you might think. By the end of this article, you'll have the knowledge and tools to remotely control your Raspberry Pi from anywhere in the world. This guide is perfect for beginners who want to dive into the world of IoT and remote device management.
Whether you're a student, hobbyist, or professional, mastering SSH for your Raspberry Pi will open doors to countless possibilities. Let's explore how you can achieve this seamlessly and securely.
Read also:Kim Tae Ri A Rising Star In The World Of Cinema
Table of Contents
- Introduction to SSH and Raspberry Pi
- Setting Up SSH on Raspberry Pi
- Understanding Remote Access with SSH
- Tools and Software for SSH Raspberry Pi
- Step-by-Step Guide for SSH Setup
- Ensuring Security in SSH Connections
- Common Issues and Troubleshooting
- Alternative Tools for Remote IoT Device Management
- Applications of SSH in IoT Projects
- Conclusion and Next Steps
Introduction to SSH and Raspberry Pi
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used to securely access remote devices over an unsecured network. It provides a secure channel for communication between two devices, ensuring data integrity and confidentiality. SSH is widely used in server management, IoT projects, and remote device control.
Why Use Raspberry Pi for IoT Projects?
Raspberry Pi is a versatile and affordable single-board computer that has become a favorite among hobbyists and professionals. Its small size, low power consumption, and extensive community support make it ideal for IoT projects. By combining Raspberry Pi with SSH, you can remotely manage and monitor your IoT devices with ease.
According to a survey by Raspberry Pi Foundation, over 40 million Raspberry Pi units have been sold globally, highlighting its popularity and reliability in various applications.
Setting Up SSH on Raspberry Pi
Prerequisites for SSH Setup
Before you begin, ensure you have the following:
- A Raspberry Pi device (any model with SSH support)
- A microSD card with Raspberry Pi OS installed
- An active internet connection
- An SSH client (such as PuTTY for Windows or Terminal for macOS/Linux)
Once you have these prerequisites, you're ready to proceed with the setup process.
Enabling SSH on Raspberry Pi
Enabling SSH on Raspberry Pi is straightforward. Follow these steps:
Read also:Chicago Tornado Watch A Comprehensive Guide To Staying Safe And Informed
- Insert the microSD card into your computer.
- Open the boot partition and create a blank file named "ssh" (without any extension).
- Insert the microSD card into your Raspberry Pi and power it on.
- SSH will automatically be enabled during the boot process.
For advanced users, you can also enable SSH through the Raspberry Pi Configuration tool or by editing the configuration files directly.
Understanding Remote Access with SSH
How Does SSH Work?
SSH establishes a secure connection between your local machine and the remote Raspberry Pi device. It uses encryption algorithms to protect data during transmission, making it ideal for sensitive applications. The protocol supports authentication methods such as passwords and public key cryptography, ensuring secure access.
Benefits of Using SSH for Remote IoT Device Management
Here are some advantages of using SSH for your IoT projects:
- Security: SSH encrypts all data transmitted between devices, preventing unauthorized access.
- Reliability: SSH connections are stable and can handle intermittent network issues.
- Flexibility: You can perform various tasks remotely, such as file transfers, command execution, and system monitoring.
Tools and Software for SSH Raspberry Pi
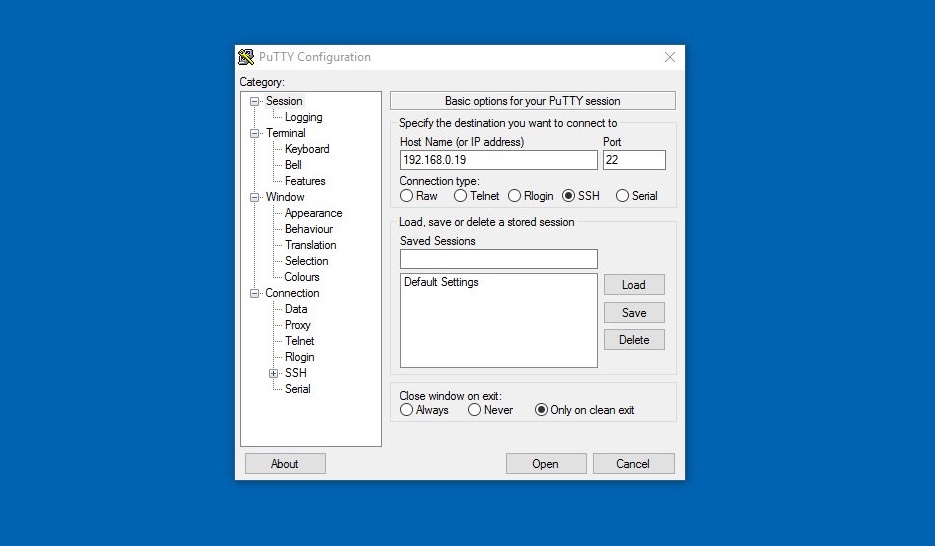
Popular SSH Clients
There are several SSH clients available for different operating systems. Some popular options include:
- PuTTY (Windows)
- Terminal (macOS/Linux)
- MobaXterm (Windows)
- Termius (Cross-platform)
Each of these tools offers unique features, so choose one that best suits your needs.
Additional Tools for IoT Projects
For IoT projects, you may also need tools such as:
- MQTT brokers for message passing
- Node-RED for visual programming
- Python libraries for sensor integration
These tools can enhance the functionality of your Raspberry Pi IoT setup.
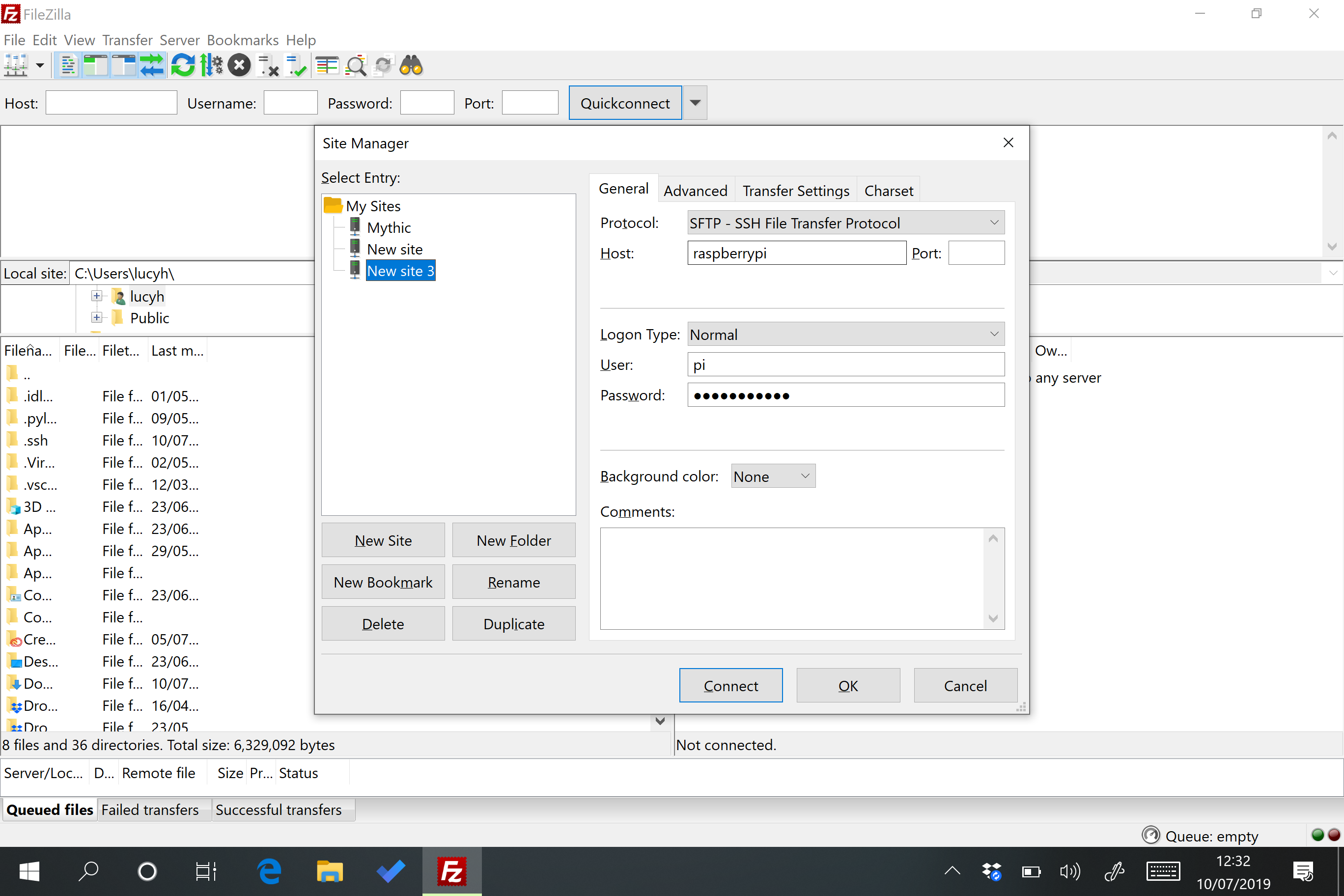
Step-by-Step Guide for SSH Setup
Connecting to Your Raspberry Pi via SSH
Follow these steps to connect to your Raspberry Pi using SSH:
- Find the IP address of your Raspberry Pi by running the command
ifconfigor checking your router's DHCP client list. - Open your SSH client and enter the IP address of your Raspberry Pi as the hostname.
- Enter your Raspberry Pi username (default is "pi") and password (default is "raspberry").
- You should now have a terminal session with your Raspberry Pi.
Configuring SSH Keys for Passwordless Login
To enhance security and convenience, you can set up SSH keys for passwordless login:
- Generate an SSH key pair on your local machine using the command
ssh-keygen. - Copy the public key to your Raspberry Pi using the command
ssh-copy-id. - Test the connection by logging in without entering a password.
Ensuring Security in SSH Connections
Best Practices for SSH Security
While SSH is secure by default, there are additional steps you can take to enhance its security:
- Change the default SSH port to a non-standard port.
- Disable password authentication and use SSH keys instead.
- Limit access to specific IP addresses using firewall rules.
- Regularly update your Raspberry Pi OS and SSH software.
SSH Security Risks
Despite its robust security features, SSH is not immune to attacks. Some common risks include:
- Brute-force attacks
- Man-in-the-middle attacks
- Unpatched vulnerabilities in SSH software
By following best practices, you can mitigate these risks and ensure the security of your SSH connections.
Common Issues and Troubleshooting
Unable to Connect via SSH
If you're unable to connect to your Raspberry Pi via SSH, consider the following solutions:
- Verify that SSH is enabled on your Raspberry Pi.
- Check the IP address and ensure it's correct.
- Ensure that your firewall rules allow SSH traffic.
Password Authentication Failed
If you encounter a "password authentication failed" error, double-check the following:
- Your username and password are correct.
- Password authentication is enabled in the SSH configuration file.
- Your Raspberry Pi OS is up to date.
Alternative Tools for Remote IoT Device Management
Other Remote Access Solutions
While SSH is a popular choice for remote access, there are other tools you can consider:
- VNC (Virtual Network Computing) for graphical access
- TeamViewer for cross-platform remote control
- Web-based interfaces for IoT devices
Each of these tools has its own advantages and limitations, so choose one that aligns with your project requirements.
Applications of SSH in IoT Projects
Real-World Use Cases
SSH can be used in various IoT projects, including:
- Home automation systems
- Environmental monitoring solutions
- Smart agriculture applications
- Industrial automation systems
By leveraging SSH, you can remotely manage and monitor these systems, ensuring they operate efficiently and securely.
Future Trends in IoT and SSH
As IoT continues to evolve, the role of SSH in remote device management will become even more critical. Emerging technologies such as 5G and edge computing will further enhance the capabilities of SSH in IoT applications.
Conclusion and Next Steps
In conclusion, setting up SSH for your Raspberry Pi IoT device is a powerful way to manage and monitor your projects remotely. By following the steps outlined in this guide, you can ensure a secure and reliable connection. Remember to adhere to best practices for SSH security and regularly update your systems to protect against potential threats.
We encourage you to take the next step by experimenting with SSH in your own IoT projects. Don't forget to share your experiences and insights in the comments below. For more informative articles and tutorials, explore our website and stay updated with the latest trends in technology.