Accessing IoT devices remotely has become an essential skill for modern technology enthusiasts, especially when leveraging SSH, web-based tools, and Ubuntu. In today's interconnected world, the ability to manage and monitor devices from anywhere is not just convenient but also crucial for efficiency and security. This article will provide a comprehensive guide on how to remotely access IoT devices using SSH, web interfaces, and downloading Ubuntu for seamless integration.
As the Internet of Things (IoT) continues to grow, the demand for remote management solutions increases. Whether you're a developer, IT professional, or hobbyist, understanding how to securely connect to IoT devices remotely can significantly enhance your capabilities. This guide will walk you through the necessary steps, tools, and best practices to ensure your remote access is both effective and secure.
By the end of this article, you'll have a clear understanding of the tools and techniques required to remotely access IoT devices, including setting up SSH connections, utilizing web-based interfaces, and downloading the appropriate version of Ubuntu. Let's dive in!
Read also:Michael Porter Jr Rising Star In The Nba With Incredible Potential
Table of Contents
- Introduction to IoT Remote Access
- What is SSH and Why Use It?
- Setting Up SSH on IoT Devices
- Accessing IoT Devices via Web Interface
- Downloading Ubuntu for IoT Devices
- Ensuring Security in Remote Access
- Recommended Tools for IoT Remote Access
- Common Issues and Troubleshooting
- Use Cases for Remote IoT Access
- Conclusion and Next Steps
Introduction to IoT Remote Access
The Internet of Things (IoT) has revolutionized how we interact with technology, enabling devices to communicate and share data seamlessly. However, managing these devices remotely is a challenge that requires a robust solution. Remote access to IoT devices allows users to monitor, configure, and troubleshoot devices from anywhere in the world.
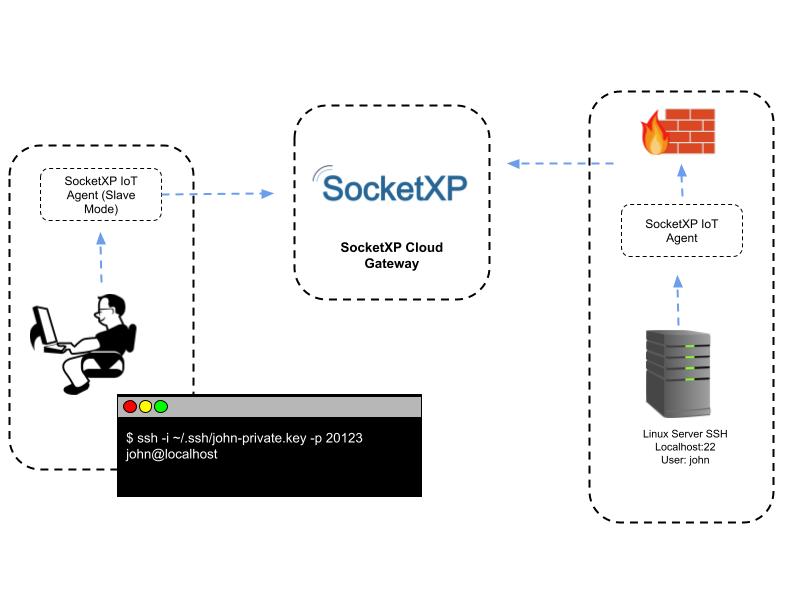
One of the most reliable methods for remote access is Secure Shell (SSH), which provides a secure channel for communication between devices. Additionally, web-based interfaces offer an alternative for users who prefer a more user-friendly approach. Downloading and installing Ubuntu on IoT devices can further enhance their capabilities, providing a powerful operating system tailored for remote management.
This section will explore the importance of remote access in IoT, the benefits it offers, and why SSH and web-based solutions are preferred by professionals.
What is SSH and Why Use It?
Understanding SSH Protocol
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over unsecured networks. It encrypts all data transmitted between devices, ensuring privacy and integrity. SSH is widely used for remote command-line login and execution, file transfers, and tunneling.
Key features of SSH include:
- Strong encryption for secure communication
- Authentication mechanisms to verify user identity
- Support for various cryptographic algorithms
Advantages of Using SSH for IoT
When it comes to remote access for IoT devices, SSH offers several advantages:
Read also:Lia Thomas A Comprehensive Look At Her Journey And Achievements
- Highly secure and resistant to eavesdropping
- Supports automation and scripting for efficient management
- Compatible with a wide range of devices and operating systems
SSH is particularly useful for IoT devices that require frequent updates, monitoring, and troubleshooting. Its robust security features make it an ideal choice for protecting sensitive data and ensuring device integrity.
Setting Up SSH on IoT Devices
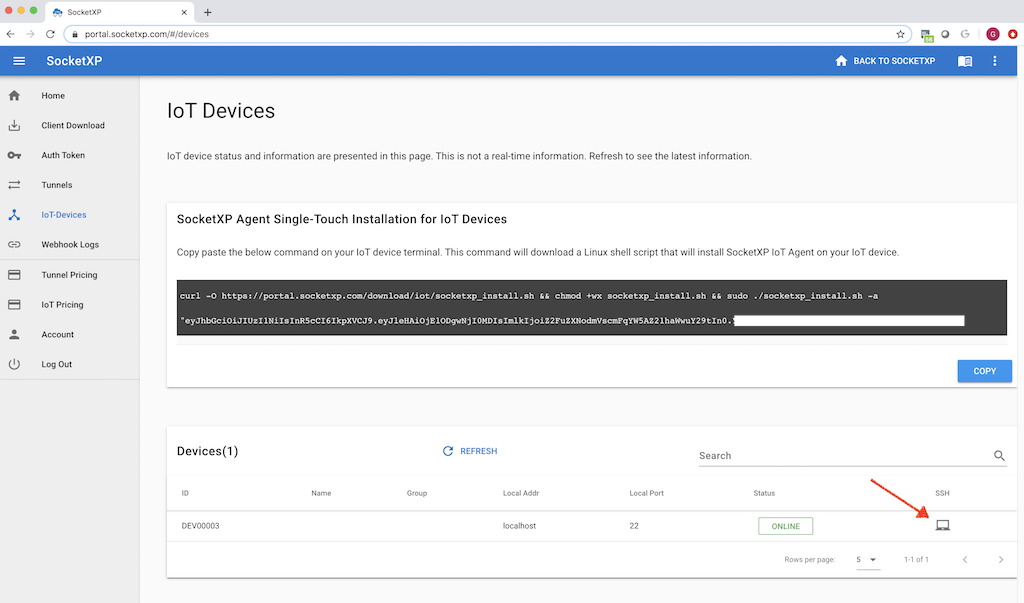
Configuring SSH on IoT devices is a straightforward process that involves enabling the SSH service, generating keys, and securing the connection. Here's a step-by-step guide:
Enabling SSH on IoT Devices
Most modern IoT devices come with SSH pre-installed, but it may need to be enabled manually. Follow these steps:
- Access the device's settings menu
- Locate the SSH service and enable it
- Restart the device to apply changes
Generating SSH Keys
SSH keys provide a secure method of authentication without the need for passwords. To generate SSH keys:
- Open a terminal on your computer
- Run the command:
ssh-keygen - Follow the prompts to create a public and private key pair
Securing SSH Connections
Once SSH is set up, it's crucial to secure the connection to prevent unauthorized access. Best practices include:
- Disabling password authentication
- Using strong, unique SSH keys
- Limiting access to specific IP addresses
Accessing IoT Devices via Web Interface
Web-Based Remote Access Solutions
In addition to SSH, web-based interfaces offer an alternative method for remote access. These solutions typically involve a web server running on the IoT device, allowing users to interact with it through a browser. Popular options include:
- Node-RED
- Home Assistant
- OpenHAB
Setting Up a Web Interface
Setting up a web interface on an IoT device involves installing a web server and configuring it to expose the necessary services. Here's how:
- Install a lightweight web server like NGINX or Apache
- Configure the server to serve the desired interface
- Set up authentication and encryption for secure access
Web-based access is particularly useful for users who prefer a graphical interface over command-line tools. It also allows for easier integration with other web-based services and applications.
Downloading Ubuntu for IoT Devices
Why Choose Ubuntu for IoT?
Ubuntu is a popular choice for IoT devices due to its stability, security, and extensive community support. It offers a range of features tailored for IoT applications, including:
- Lightweight and efficient performance
- Support for a wide range of hardware architectures
- Regular updates and security patches
Downloading and Installing Ubuntu
Downloading Ubuntu for IoT devices is simple. Follow these steps:
- Visit the official Ubuntu website
- Select the appropriate version for your device
- Download the image file and write it to an SD card or USB drive
- Install Ubuntu on your IoT device following the installation guide
Once installed, Ubuntu provides a powerful platform for developing and managing IoT applications, making it an excellent choice for remote access solutions.
Ensuring Security in Remote Access
Best Practices for Secure Remote Access
Security is paramount when remotely accessing IoT devices. Implementing best practices can significantly reduce the risk of unauthorized access. Key recommendations include:
- Using strong, unique passwords and SSH keys
- Enabling two-factor authentication
- Regularly updating software and firmware
Monitoring and Logging
Monitoring and logging are essential for detecting and responding to security incidents. Implementing tools like fail2ban and logwatch can help:
- Block repeated login attempts
- Alert administrators of suspicious activity
- Provide detailed logs for analysis
By following these security measures, you can ensure your IoT devices remain protected while maintaining remote access capabilities.
Recommended Tools for IoT Remote Access
SSH Clients
Several SSH clients are available for different operating systems. Popular options include:
- Putty (Windows)
- Terminal (macOS/Linux)
- MobaXterm (Cross-platform)
Web-Based Tools
For web-based remote access, consider the following tools:
- Node-RED for visual programming
- Home Assistant for home automation
- OpenHAB for open-source home automation
These tools provide a user-friendly interface for managing IoT devices remotely, making them ideal for both beginners and professionals.
Common Issues and Troubleshooting
Despite careful setup, issues may arise when remotely accessing IoT devices. Here are some common problems and solutions:
Connection Issues
If you're unable to connect to your device:
- Check the network configuration
- Verify the IP address and port number
- Ensure the SSH service is running
Security Alerts
If you receive security alerts:
- Review logs for suspicious activity
- Update security settings and software
- Implement additional security measures
By addressing these issues promptly, you can maintain a stable and secure remote access environment.
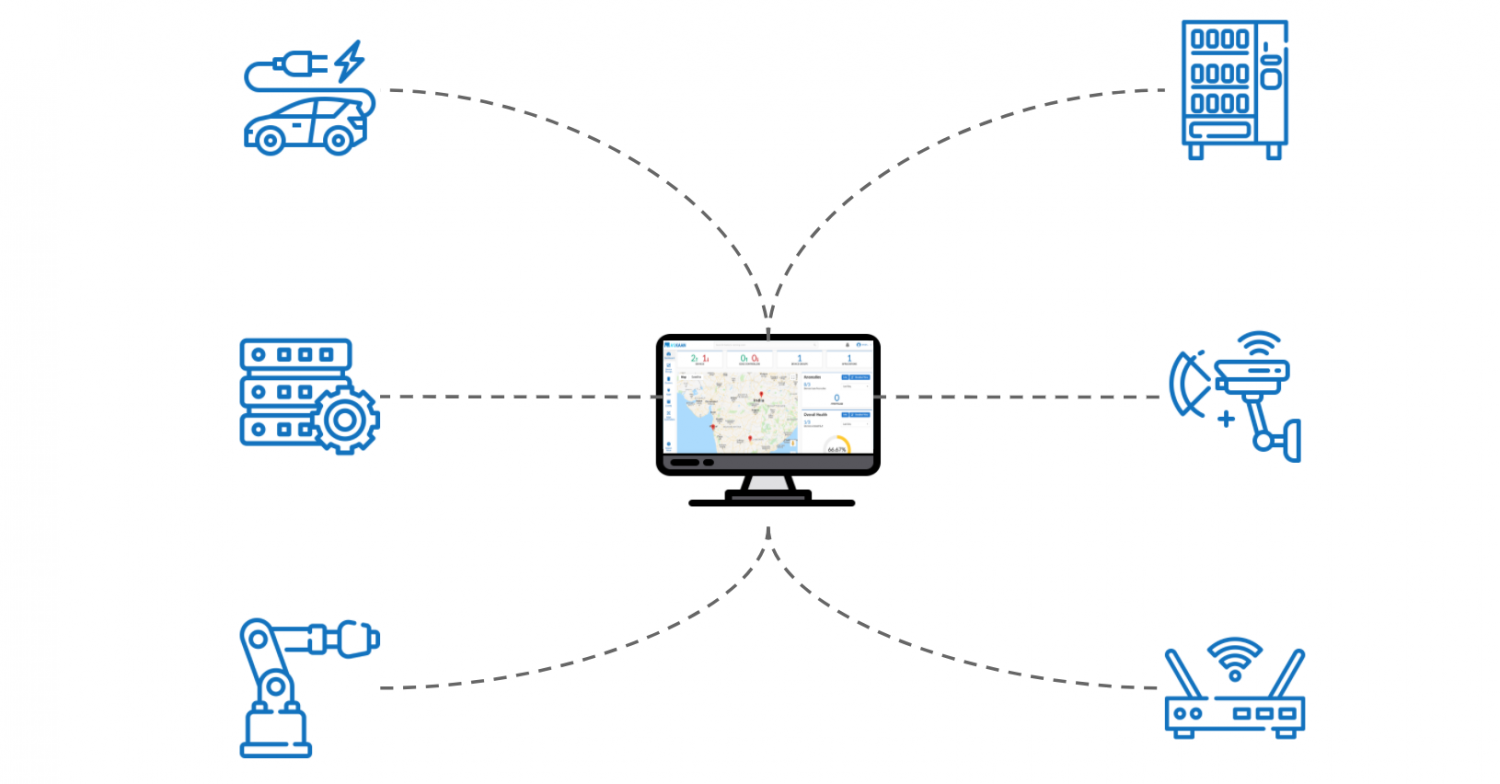
Use Cases for Remote IoT Access
Industrial Applications
Remote access is critical in industrial settings, allowing engineers to monitor and control equipment from a central location. Use cases include:
- Remote monitoring of machinery
- Automated data collection and analysis
- Remote troubleshooting and maintenance
Smart Home Solutions
In smart homes, remote access enables users to control devices like lights, thermostats, and security systems from anywhere. Benefits include:
- Increased convenience and comfort
- Improved energy efficiency
- Enhanced security
These use cases demonstrate the versatility and value of remote access in various industries and applications.
Conclusion and Next Steps
Remotely accessing IoT devices via SSH, web interfaces, and Ubuntu is a powerful solution for managing and monitoring devices from anywhere. By following the steps outlined in this guide, you can set up a secure and efficient remote access system tailored to your needs.
To further enhance your skills, consider exploring advanced topics such as automation, scripting, and integrating additional tools and services. We encourage you to share your thoughts and experiences in the comments below, and don't forget to check out our other articles for more insights into IoT and remote access technologies.
Thank you for reading, and happy hacking!