IoT remote access with SSH on AWS is a powerful solution for securely managing devices over the internet. As the Internet of Things (IoT) continues to expand, the need for robust and secure remote access methods becomes increasingly critical. With AWS offering scalable and secure infrastructure, combining SSH with IoT devices ensures seamless connectivity and management.
From smart homes to industrial automation, IoT devices are transforming how we interact with technology. However, ensuring secure access to these devices remotely is a challenge that must be addressed. This article explores how SSH on AWS can provide a secure and efficient solution for IoT remote access.
Whether you're a developer, system administrator, or IT professional, understanding the nuances of IoT remote access with SSH on AWS can enhance your ability to manage and secure IoT devices effectively. Let's dive deeper into the specifics of this integration and its practical applications.
Read also:Michael Porter Jr Rising Star In The Nba With Incredible Potential
Table of Contents
- Introduction to IoT Remote Access
- Benefits of Using SSH on AWS for IoT
- AWS Architecture for IoT SSH Access
- Setup Process for IoT Remote Access
- Security Measures for IoT Devices
- Example Implementation of IoT SSH on AWS
- Troubleshooting Common Issues
- Best Practices for IoT Remote Access
- Future Trends in IoT Remote Access
- Conclusion
Introduction to IoT Remote Access
IoT remote access refers to the ability to control and manage IoT devices from a remote location. This capability is essential for monitoring, troubleshooting, and maintaining devices without physical presence. The integration of SSH on AWS enhances this process by providing a secure communication channel.
SSH, or Secure Shell, is a cryptographic protocol that facilitates secure communication over unsecured networks. By leveraging AWS services, such as EC2 instances and IAM roles, IoT devices can be accessed remotely with enhanced security features.
Understanding the fundamentals of IoT remote access is crucial for implementing effective solutions. This section explores the basic concepts and importance of secure remote access in the IoT ecosystem.
Benefits of Using SSH on AWS for IoT
Utilizing SSH on AWS for IoT remote access offers numerous advantages. Firstly, AWS provides a scalable infrastructure that can handle the demands of IoT networks, ensuring reliable connectivity even during peak usage. Secondly, AWS's security features, such as encrypted data transfer and identity management, enhance the protection of IoT devices.
Additionally, AWS integrates seamlessly with other cloud services, enabling automation and streamlined management of IoT devices. The ability to scale resources dynamically ensures that IoT deployments can grow without compromising performance or security.
Scalability and Flexibility
One of the key benefits of using AWS for IoT remote access is its scalability. As IoT networks expand, AWS can accommodate increased traffic and device counts without significant manual intervention. This flexibility allows organizations to adapt to changing demands efficiently.
Read also:Lean Cuisine Recall Understanding The Impact And What You Need To Know
Enhanced Security Features
AWS offers advanced security features, such as IAM roles, VPCs, and encryption, which protect IoT devices from unauthorized access. These features ensure that data transmitted between devices and the cloud remains secure and confidential.
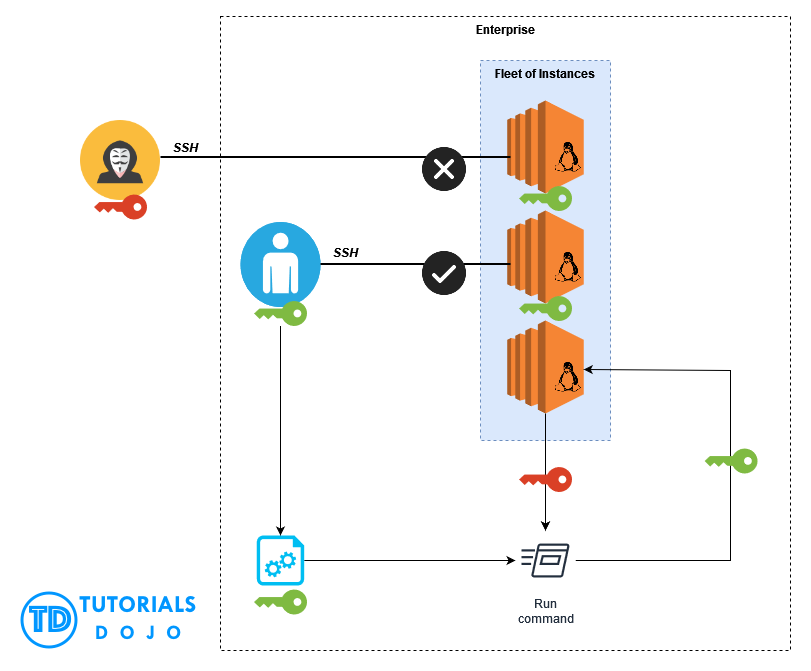
AWS Architecture for IoT SSH Access
The architecture for IoT remote access using SSH on AWS involves several key components. These include EC2 instances, IAM roles, security groups, and VPCs. Each component plays a critical role in ensuring secure and efficient communication between IoT devices and the cloud.
EC2 instances serve as the primary platform for hosting SSH servers, while IAM roles manage access permissions. Security groups act as virtual firewalls, controlling inbound and outbound traffic, and VPCs provide an isolated network environment for enhanced security.
Key Components
- EC2 Instances: Host SSH servers for remote access.
- IAM Roles: Manage user permissions and access control.
- Security Groups: Control network traffic to and from instances.
- VPCs: Create a secure and isolated network environment.
Setup Process for IoT Remote Access
Setting up IoT remote access with SSH on AWS involves several steps. These include creating an EC2 instance, configuring security groups, setting up IAM roles, and establishing SSH connections. Each step is crucial for ensuring a secure and functional setup.
Begin by launching an EC2 instance and selecting an appropriate Amazon Machine Image (AMI). Configure the security group to allow SSH traffic on port 22. Next, create IAM roles to manage access permissions and ensure only authorized users can access the devices.
Step-by-Step Guide
- Create an EC2 instance with the desired AMI.
- Configure the security group to allow SSH traffic.
- Set up IAM roles for access management.
- Establish SSH connections to the IoT devices.
Security Measures for IoT Devices
Securing IoT devices is paramount when implementing remote access solutions. SSH on AWS provides several security measures to protect devices from unauthorized access and potential threats. These include key-based authentication, encrypted communication, and network isolation.
Key-based authentication eliminates the need for passwords, reducing the risk of brute-force attacks. Encrypted communication ensures that data transmitted between devices and the cloud remains secure. Network isolation through VPCs further enhances security by creating a dedicated network environment for IoT devices.
Best Security Practices
- Use key-based authentication instead of passwords.
- Enable encryption for all data transmissions.
- Regularly update security settings and configurations.
Example Implementation of IoT SSH on AWS
A practical example of IoT remote access with SSH on AWS involves setting up a smart home system. In this scenario, multiple IoT devices, such as smart thermostats and security cameras, are connected to an EC2 instance via SSH. The EC2 instance acts as a central hub for managing and monitoring the devices.
The implementation process includes configuring the EC2 instance, setting up security groups, and establishing SSH connections. Once the setup is complete, users can remotely access and control the devices through a secure SSH connection.
Implementation Steps
- Configure the EC2 instance as a central hub.
- Set up security groups to allow SSH traffic.
- Establish SSH connections to the IoT devices.
- Monitor and manage devices remotely through the SSH connection.
Troubleshooting Common Issues
While implementing IoT remote access with SSH on AWS, users may encounter various issues. Common problems include connection failures, authentication errors, and network configuration issues. Understanding how to troubleshoot these problems is essential for maintaining a functional setup.
Connection failures can often be resolved by checking the security group settings and ensuring that SSH traffic is allowed. Authentication errors may require verifying key-based authentication settings and ensuring that the correct keys are being used. Network configuration issues can be addressed by reviewing VPC settings and ensuring proper subnet configurations.
Troubleshooting Tips
- Verify security group settings for SSH traffic.
- Check key-based authentication settings.
- Review VPC and subnet configurations.
Best Practices for IoT Remote Access
Adopting best practices for IoT remote access ensures a secure and efficient setup. These practices include regular security audits, monitoring network activity, and keeping software and firmware up to date. By following these guidelines, organizations can minimize risks and maximize the benefits of IoT remote access.
Regular security audits help identify potential vulnerabilities and address them proactively. Monitoring network activity allows for early detection of suspicious behavior, while keeping software and firmware updated ensures compatibility and security.
Key Best Practices
- Conduct regular security audits.
- Monitor network activity for suspicious behavior.
- Keep software and firmware updated.
Future Trends in IoT Remote Access
The future of IoT remote access with SSH on AWS looks promising, with advancements in technology and increasing demand for secure connectivity. Emerging trends include the integration of AI and machine learning for enhanced security, the adoption of edge computing for improved performance, and the development of new protocols for secure communication.
As IoT networks continue to grow, the need for scalable and secure solutions becomes increasingly important. AWS is at the forefront of this evolution, providing cutting-edge technologies and services to support IoT deployments.
Conclusion
In conclusion, IoT remote access with SSH on AWS offers a secure and efficient solution for managing IoT devices. By leveraging AWS's scalable infrastructure and advanced security features, organizations can ensure reliable and secure connectivity for their IoT networks. This article has explored the benefits, setup process, security measures, and future trends of IoT remote access with SSH on AWS.
We encourage readers to implement the best practices discussed and explore the possibilities of IoT remote access with SSH on AWS. Your feedback and questions are valuable, so please leave a comment or share this article with others who may benefit from it. For more insights and updates, explore our other articles on IoT and cloud computing topics.