In today's interconnected world, Secure Shell (SSH) plays a crucial role in securing communications within IoT networks on Windows systems. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices has become more important than ever. SSH provides a robust framework for encrypted data transfer, protecting sensitive information from unauthorized access and cyber threats.
With the rapid growth of IoT devices, securing network communications is no longer an option—it's a necessity. SSH in IoT networks on Windows offers a secure method to manage devices remotely, ensuring data integrity and confidentiality. By leveraging SSH, organizations can safeguard their networks against potential vulnerabilities and breaches.
This article delves into the intricacies of Secure Shell (SSH) in IoT networks for Windows, exploring its functionality, benefits, challenges, and best practices. Whether you're a developer, system administrator, or cybersecurity professional, understanding SSH is essential for maintaining secure IoT ecosystems.
Read also:Avalanche Vs Maple Leafs A Comprehensive Analysis Of The Ultimate Rivalry
Table of Contents
- Introduction to Secure Shell (SSH)
- Understanding SSH in IoT Networks
- Implementing SSH on Windows
- Benefits of Using SSH in IoT Networks
- Security Features of SSH
- Challenges in Implementing SSH for IoT
- Best Practices for SSH in IoT Networks
- Configuring SSH in IoT Networks
- Real-World Use Cases of SSH in IoT
- Future Trends of SSH in IoT Networks
Introduction to Secure Shell (SSH)
Secure Shell (SSH) is a cryptographic network protocol designed to provide secure communication over an unsecured network. Originally developed in 1995 by Tatu Ylönen, SSH has become a cornerstone of modern networking, enabling secure remote access to devices and systems. It is widely used in various industries, including IT, telecommunications, and finance, to protect sensitive data and ensure secure communication.
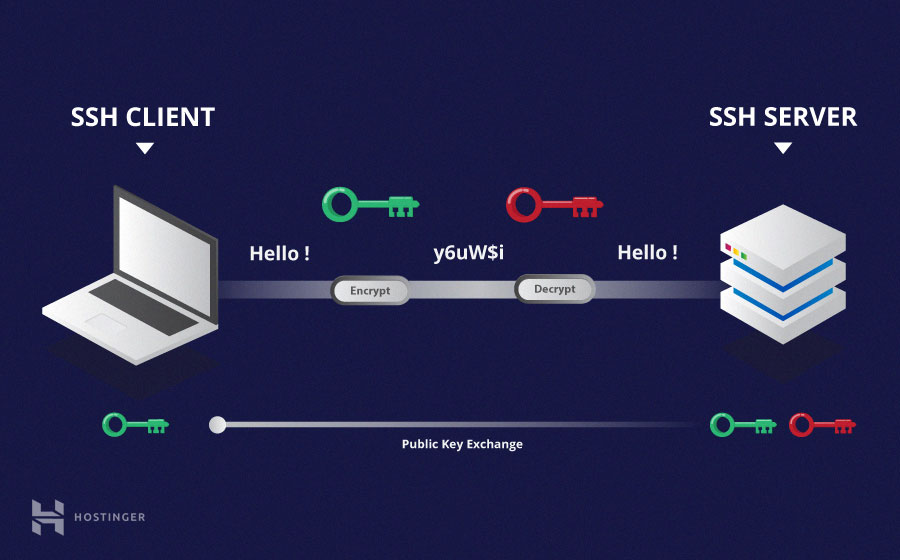
SSH operates on a client-server model, where a client initiates a connection to a server using encrypted protocols. This ensures that data transmitted between the client and server remains confidential and tamper-proof. In the context of IoT networks, SSH plays a vital role in securing communications between devices, especially when managing and monitoring them remotely.
How SSH Works
SSH establishes a secure channel by using a combination of symmetric and asymmetric encryption methods. The process involves:
- Authentication: Verifying the identity of the client and server using public key cryptography.
- Encryption: Encrypting data exchanged between the client and server to prevent unauthorized access.
- Integrity: Ensuring data integrity through cryptographic hashing.
Understanding SSH in IoT Networks
In the realm of IoT, SSH serves as a critical tool for securing communications between devices. With millions of IoT devices connected to the internet, ensuring secure communication is paramount. SSH provides a reliable method for managing and monitoring IoT devices remotely, reducing the risk of unauthorized access and data breaches.
IoT networks often consist of devices with limited computational resources, making it challenging to implement complex security protocols. SSH addresses this issue by offering a lightweight yet robust solution for securing communications. By leveraging SSH, organizations can maintain control over their IoT ecosystems while ensuring data privacy and security.
Key Features of SSH in IoT
- Remote Access: Enables secure remote management of IoT devices.
- Data Encryption: Protects sensitive information transmitted between devices.
- Authentication: Ensures only authorized users and devices can access the network.
Implementing SSH on Windows
Windows provides built-in support for SSH, making it easier for users to implement secure communication protocols in IoT networks. Starting with Windows 10, Microsoft introduced OpenSSH as a native feature, allowing users to enable SSH client and server functionalities directly from the settings menu.
Read also:Keith Urban The Country Music Icon Redefining The Genre
To enable SSH on Windows, users can follow these steps:
- Open the Windows Features dialog box.
- Check the boxes for "OpenSSH Client" and "OpenSSH Server."
- Restart the system to apply the changes.
Once enabled, users can use SSH to securely connect to IoT devices and manage them remotely.
Configuring SSH on Windows
Configuring SSH on Windows involves setting up the SSH server and client. This includes:
- Setting up the SSH Server: Configuring the server to accept incoming connections securely.
- Managing SSH Keys: Generating and managing public and private keys for authentication.
- Securing the SSH Connection: Implementing best practices to enhance security.
Benefits of Using SSH in IoT Networks
Using SSH in IoT networks offers numerous advantages, including:
- Enhanced Security: SSH provides strong encryption and authentication mechanisms, protecting data from unauthorized access.
- Remote Management: Enables administrators to manage IoT devices remotely, improving efficiency and reducing costs.
- Scalability: SSH can be easily scaled to accommodate growing IoT networks, ensuring consistent security across all devices.
By leveraging SSH, organizations can create a secure and reliable IoT ecosystem, safeguarding their networks against potential threats.
Why SSH is Essential for IoT Networks
In IoT networks, SSH serves as a fundamental tool for ensuring secure communication. Its ability to encrypt data and authenticate users makes it an indispensable asset for protecting sensitive information. Additionally, SSH's compatibility with various operating systems, including Windows, makes it a versatile solution for IoT environments.
Security Features of SSH
SSH incorporates several security features that make it a reliable choice for securing IoT networks. These include:
- Encryption: SSH uses advanced encryption algorithms to protect data during transmission.
- Authentication: Public key authentication ensures only authorized users can access the network.
- Integrity Checks: Cryptographic hashing ensures data integrity and detects any unauthorized modifications.
These features collectively enhance the security of IoT networks, making them more resilient to cyber threats.
Advanced Security Protocols in SSH
SSH employs advanced security protocols, such as:
- Transport Layer Security (TLS): Ensures secure communication between devices.
- Public Key Infrastructure (PKI): Facilitates secure authentication and encryption.
- Secure File Transfer Protocol (SFTP): Enables secure file transfers within the network.
Challenges in Implementing SSH for IoT
While SSH offers numerous benefits, implementing it in IoT networks presents certain challenges. These include:
- Resource Constraints: Many IoT devices have limited computational resources, making it difficult to implement complex security protocols.
- Key Management: Managing public and private keys across a large number of devices can be cumbersome.
- Network Complexity: IoT networks often consist of diverse devices and systems, complicating the implementation of unified security solutions.
Addressing these challenges requires a comprehensive approach that balances security with usability and scalability.
Overcoming SSH Implementation Challenges
To overcome the challenges of implementing SSH in IoT networks, organizations can adopt the following strategies:
- Optimizing Resource Usage: Utilizing lightweight encryption algorithms and protocols.
- Automating Key Management: Implementing automated systems for generating and managing SSH keys.
- Standardizing Security Protocols: Establishing uniform security standards across all devices and systems.
Best Practices for SSH in IoT Networks
Implementing SSH in IoT networks requires adherence to best practices to ensure maximum security and efficiency. These include:
- Regular Updates: Keeping SSH software and firmware up to date to address potential vulnerabilities.
- Strong Authentication: Using strong passwords and public key authentication to enhance security.
- Monitoring and Logging: Implementing robust monitoring and logging systems to detect and respond to security incidents.
By following these best practices, organizations can create a secure and resilient IoT ecosystem.
Advanced Best Practices for SSH
For organizations seeking to enhance their SSH implementation, the following advanced best practices can be considered:
- Network Segmentation: Isolating IoT devices from other network segments to minimize risks.
- Access Control: Implementing granular access controls to restrict unauthorized access.
- Regular Audits: Conducting regular security audits to identify and address potential vulnerabilities.
Configuring SSH in IoT Networks
Configuring SSH in IoT networks involves several steps, including:
- Setting Up the SSH Server: Configuring the server to accept incoming connections securely.
- Generating SSH Keys: Creating public and private keys for authentication.
- Securing the SSH Connection: Implementing encryption and authentication protocols to enhance security.
Proper configuration is essential for ensuring the effectiveness of SSH in securing IoT networks.
Advanced Configuration Techniques
Advanced configuration techniques for SSH in IoT networks include:
- Customizing SSH Settings: Tailoring SSH settings to meet specific security requirements.
- Implementing Failover Mechanisms: Ensuring continuity of operations in case of failures.
- Using SSH Tunnels: Creating secure tunnels for data transmission between devices.
Real-World Use Cases of SSH in IoT
SSH has been successfully implemented in various real-world IoT applications, including:
- Smart Home Systems: Securing communications between smart home devices and control systems.
- Industrial IoT (IIoT): Protecting critical infrastructure and industrial control systems.
- Healthcare IoT: Ensuring secure communication between medical devices and patient monitoring systems.
These use cases demonstrate the versatility and effectiveness of SSH in securing IoT networks.
Case Studies of SSH in IoT
Several case studies highlight the successful implementation of SSH in IoT networks. For example:
- Case Study 1: A manufacturing company used SSH to secure communications between industrial robots and control systems.
- Case Study 2: A healthcare provider implemented SSH to protect sensitive patient data transmitted between medical devices.
Future Trends of SSH in IoT Networks
As IoT continues to evolve, the role of SSH in securing networks is expected to grow. Future trends in SSH for IoT networks include:
- Quantum-Resistant Encryption: Developing encryption methods resistant to quantum computing attacks.
- AI-Driven Security: Leveraging artificial intelligence to enhance SSH security and detection capabilities.
- Blockchain Integration: Exploring the integration of blockchain technology to enhance SSH security.
These trends underscore the ongoing importance of SSH in securing IoT networks and protecting sensitive data.
Conclusion
In conclusion, Secure Shell (SSH) plays a vital role in securing IoT networks on Windows systems. By providing robust encryption, authentication, and data integrity features, SSH ensures secure communication between devices, protecting them from unauthorized access and cyber threats. Implementing SSH in IoT networks requires adherence to best practices and a comprehensive approach to address potential challenges.
We encourage readers to explore the capabilities of SSH in their IoT environments and implement it to enhance security. Feel free to leave a comment, share this article, or explore other related content on our site to