In today's interconnected world, SSH remote IoT device access via Android APK has become an essential tool for developers, engineers, and tech enthusiasts alike. With the rapid growth of the Internet of Things (IoT), managing and interacting with remote devices has never been more critical. This article will guide you through everything you need to know about SSH remote IoT device access on Android, ensuring you can securely connect and manage your devices from anywhere.
SSH (Secure Shell) is a cryptographic network protocol designed to provide secure communication over an unsecured network. It has become the go-to method for remote device access due to its robust security features and versatility. As more IoT devices are integrated into our daily lives, understanding how to leverage SSH on Android is crucial for maintaining control and ensuring data security.
Whether you're a seasoned professional or just starting your journey in IoT development, this comprehensive guide will equip you with the knowledge and tools necessary to master SSH remote IoT device access on Android. Let's dive in!
Read also:Marty Stuart The Legendary Country Music Icon
Table of Contents
- Introduction to SSH Remote IoT Device Access
- Why Use SSH for IoT Device Access
- Understanding SSH Remote Access via Android APK
- Installing SSH APK on Android
- Connecting to IoT Devices
- Security Considerations for SSH Remote Access
- Troubleshooting Common Issues
- Advanced SSH Features
- Alternatives to SSH for Remote IoT Access
- The Future of SSH Remote IoT Access
Introduction to SSH Remote IoT Device Access
What is SSH?
SSH, or Secure Shell, is a network protocol that provides secure communication between two computers over an unsecured network. Developed in the early 1990s, SSH has become the standard for remote access due to its encryption capabilities and authentication mechanisms. In the context of IoT, SSH allows users to securely connect to and manage remote devices from anywhere in the world.
Why IoT Devices Need Secure Access
With the proliferation of IoT devices, ensuring secure access has become paramount. These devices often handle sensitive data, making them attractive targets for cybercriminals. SSH offers a reliable solution by encrypting all data transmitted between the user and the device, protecting against unauthorized access and data breaches.
Android's Role in IoT Management
Android devices have emerged as powerful tools for managing IoT networks. With the right APK, users can leverage their smartphones or tablets to access and control remote IoT devices, providing unparalleled convenience and flexibility.
Why Use SSH for IoT Device Access
Security Benefits
SSH offers several security advantages over other remote access protocols. Its encryption algorithms ensure that all data transmitted between the user and the IoT device remains confidential. Additionally, SSH supports various authentication methods, including password-based and public-key authentication, allowing users to choose the level of security that best suits their needs.
Reliability and Versatility
SSH is renowned for its reliability and versatility. It can be used to execute commands, transfer files, and even tunnel other protocols, making it an indispensable tool for IoT device management. Whether you're troubleshooting a device or configuring its settings, SSH provides a stable and efficient connection.
Read also:Unblocked Games G The Ultimate Guide To Fun And Entertainment
Compatibility
One of SSH's greatest strengths is its compatibility with a wide range of devices and operating systems. This makes it an ideal choice for managing diverse IoT networks, where devices may run on different platforms and architectures.
Understanding SSH Remote Access via Android APK
What is an APK?
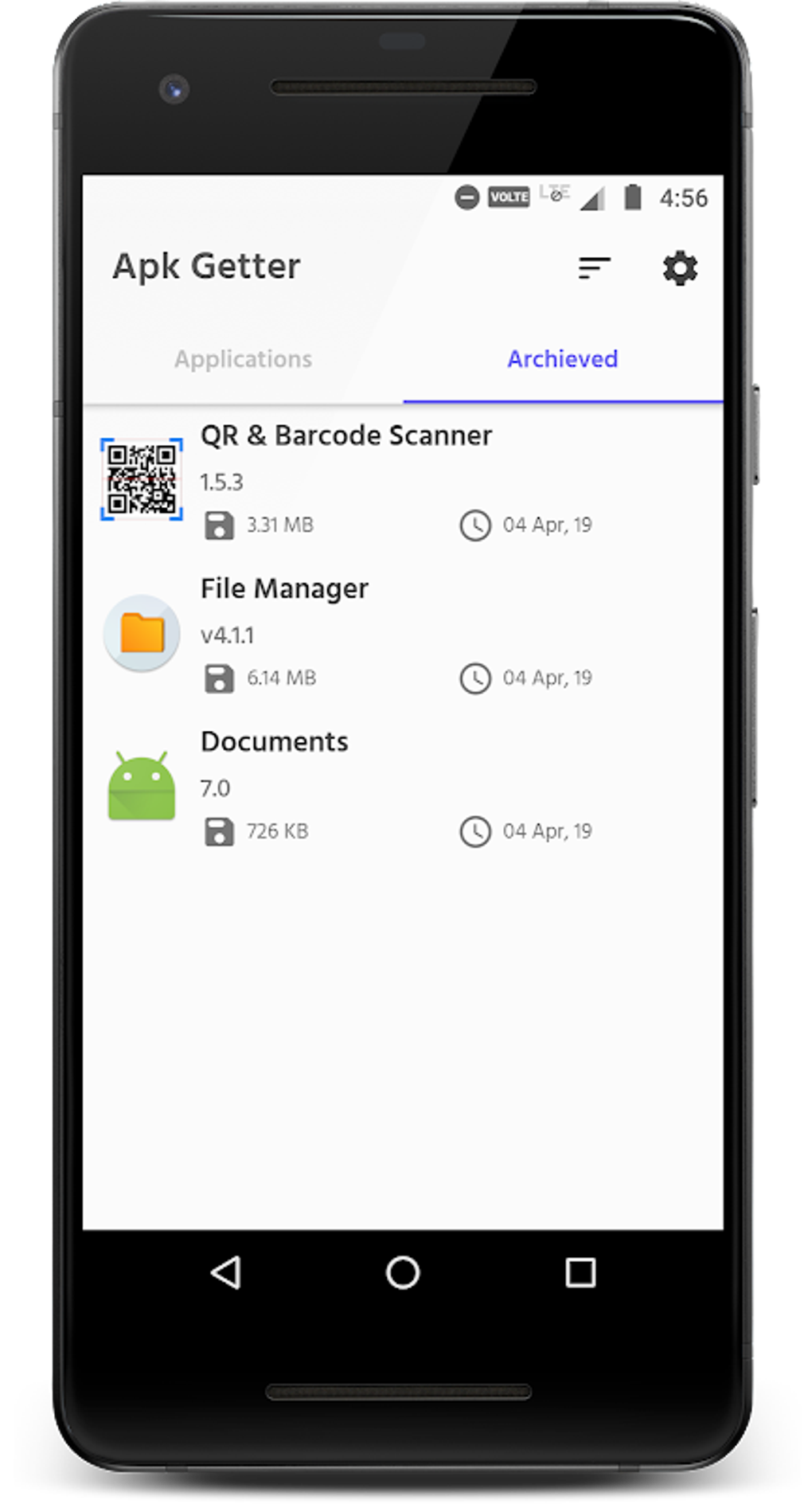
An APK, or Android Package, is the file format used to distribute and install applications on Android devices. Many SSH clients are available as APKs, allowing users to easily download and install them on their smartphones or tablets.
Popular SSH APKs
- Termius
- ConnectBot
- ServerAuditor
- SSH Client
These applications provide a user-friendly interface for managing SSH connections and interacting with remote IoT devices.
Features of SSH APKs
Modern SSH APKs come equipped with a variety of features to enhance the user experience. These include session management, key pair generation, and support for multiple protocols. Some even offer advanced features like port forwarding and file transfer capabilities.
Installing SSH APK on Android
Downloading an SSH APK
To get started, you'll need to download an SSH APK from a trusted source. Popular options include the Google Play Store and the official websites of the respective applications. Always ensure that you're downloading from a reputable source to avoid security risks.
Installing the APK
Once downloaded, installing the APK is straightforward. Simply open the file and follow the on-screen instructions. Most SSH clients will require certain permissions to function properly, so be sure to grant them when prompted.
Configuring the Application
After installation, you'll need to configure the application to connect to your IoT devices. This typically involves setting up SSH keys, specifying the server address, and configuring any additional settings required by your network.
Connecting to IoT Devices
Establishing a Connection
Connecting to an IoT device via SSH is a straightforward process. Begin by entering the device's IP address or hostname in the application's connection settings. Next, specify the port number (usually 22 for SSH) and select the appropriate authentication method.
Authentication Methods
- Password-based authentication
- Public-key authentication
- Two-factor authentication
Each method has its own advantages and disadvantages, so choose the one that best fits your security requirements.
Troubleshooting Connection Issues
If you encounter issues while connecting, check the following:
- Ensure the device's SSH service is running
- Verify the IP address and port number
- Check firewall settings
These steps should help resolve most common connection problems.
Security Considerations for SSH Remote Access
Best Practices for Secure SSH Connections
To ensure the security of your SSH connections, follow these best practices:
- Use strong, unique passwords
- Enable public-key authentication
- Disable password-based authentication
- Regularly update SSH software
These measures will help protect your IoT devices from unauthorized access.
Securing Your Android Device
In addition to securing your SSH connections, it's essential to safeguard your Android device. This includes using a screen lock, enabling encryption, and keeping the operating system and applications up to date.
Monitoring and Logging
Implementing monitoring and logging solutions can help detect and respond to potential security threats. These tools provide valuable insights into connection attempts and can alert you to suspicious activity.
Troubleshooting Common Issues
Connection Refused Errors
A "connection refused" error typically indicates that the SSH service on the IoT device is not running or that the port is blocked by a firewall. Check the device's SSH configuration and ensure that the necessary ports are open.
Authentication Failures
If you're experiencing authentication failures, verify that your credentials are correct and that the authentication method is properly configured. Additionally, check the device's SSH logs for more detailed information.
Performance Issues
Slow or unstable connections can be caused by network congestion or insufficient bandwidth. Consider optimizing your network settings or using a faster connection to improve performance.
Advanced SSH Features
Port Forwarding
SSH's port forwarding feature allows you to securely access services running on a remote IoT device. This can be particularly useful for managing databases, web servers, and other applications.
File Transfer
Many SSH clients support file transfer protocols like SFTP and SCP, enabling you to easily transfer files between your Android device and IoT devices.
Automation and Scripting
SSH can be used in conjunction with automation tools and scripting languages to streamline IoT device management tasks. This can significantly reduce the time and effort required to maintain your network.
Alternatives to SSH for Remote IoT Access
Web-Based Interfaces
Some IoT devices offer web-based interfaces for remote access. While convenient, these solutions often lack the security features provided by SSH.
VPN Connections
Virtual Private Networks (VPNs) can be used to create secure tunnels for accessing IoT devices. However, they may require additional setup and maintenance compared to SSH.
Custom Solutions
For specialized applications, custom remote access solutions may be developed. These can offer tailored functionality but may require significant development resources.
The Future of SSH Remote IoT Access
Emerging Technologies
As technology continues to evolve, new advancements in encryption, authentication, and network protocols will enhance the capabilities of SSH for IoT device access. These developments promise to make remote management even more secure and efficient.
Increased Adoption
With the growing importance of IoT in various industries, the adoption of SSH for remote device access is expected to increase. This will drive further innovation and improvement in SSH clients and related technologies.
Challenges and Opportunities
While the future of SSH remote IoT access is promising, challenges such as increasing cyber threats and the need for greater scalability must be addressed. By embracing emerging technologies and best practices, the potential for SSH in IoT management is virtually limitless.
Conclusion
In conclusion, mastering SSH remote IoT device access on Android with APK is a valuable skill for anyone involved in IoT development and management. By understanding the principles and practices outlined in this article, you can securely and efficiently manage your IoT devices from anywhere in the world.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT and related technologies. Together, let's build a safer and more connected future!
Data Sources:
- OpenSSH Documentation
- Google Developers
- IoT Journal
- SecurityWeek