Remote IoT SSH on AWS has become a critical aspect of modern technology, enabling secure communication between devices and cloud infrastructure. As the Internet of Things (IoT) continues to expand, integrating secure shell (SSH) protocols with Amazon Web Services (AWS) ensures seamless connectivity and robust security. This article will explore how to leverage AWS for remote IoT SSH operations, covering everything from setup to optimization.
As businesses increasingly adopt IoT technologies, the need for secure and reliable remote access grows exponentially. By integrating SSH protocols with AWS, companies can enhance their IoT network's security while maintaining efficient communication. This guide will provide an in-depth understanding of how to implement remote IoT SSH using AWS, empowering you to build scalable and secure IoT ecosystems.
Whether you're a developer, IT professional, or business owner, mastering remote IoT SSH on AWS is essential for staying ahead in today's competitive landscape. This article will walk you through the entire process, ensuring you have all the tools and knowledge necessary to implement this powerful technology effectively.
Read also:Lia Thomas A Comprehensive Look At Her Journey And Achievements
Table of Contents
- Introduction to IoT SSH
- Understanding AWS for Remote IoT SSH
- Setting Up Remote IoT SSH on AWS
- Securing IoT Devices with SSH
- Optimizing SSH Performance on AWS
- Troubleshooting Common Issues
- Best Practices for Remote IoT SSH
- Real-World Applications
- Future Trends in Remote IoT SSH
- Conclusion and Next Steps
Introduction to IoT SSH
The Internet of Things (IoT) revolution has transformed the way devices interact with each other and with cloud-based systems. SSH (Secure Shell) plays a pivotal role in ensuring secure communication between IoT devices and remote servers. By leveraging SSH, IoT devices can establish encrypted connections, safeguarding sensitive data from unauthorized access.
Why SSH is Essential for IoT
SSH provides a secure channel for remote access and data transfer, making it indispensable for IoT applications. Key benefits include:
- End-to-end encryption for secure data transmission
- Authentication mechanisms to prevent unauthorized access
- Support for command-line interfaces for efficient device management
Understanding AWS for Remote IoT SSH
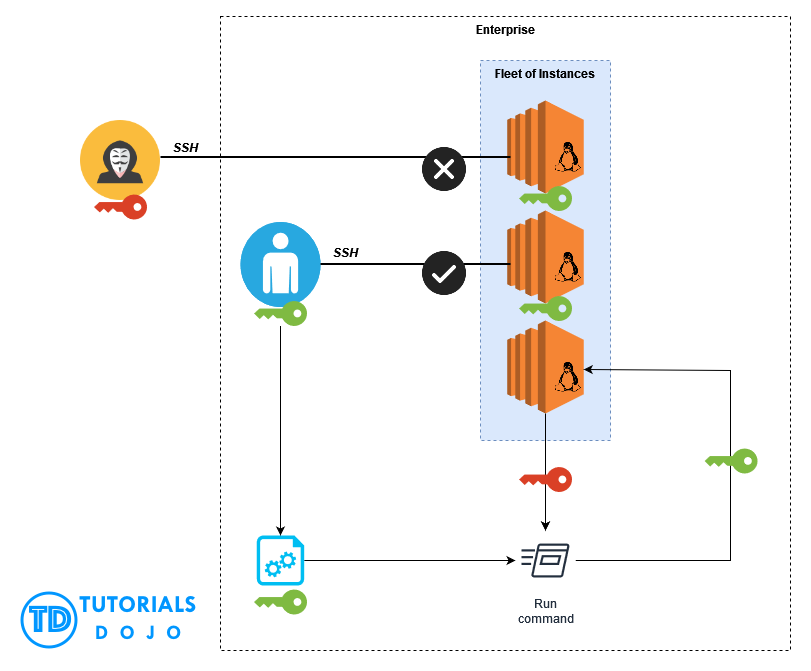
Amazon Web Services (AWS) offers a robust platform for deploying and managing IoT applications. With its scalable infrastructure and advanced security features, AWS is an ideal choice for implementing remote IoT SSH solutions. The platform provides a range of services, including AWS IoT Core, AWS Lambda, and Amazon EC2, which can be seamlessly integrated to create secure and efficient IoT ecosystems.
Key AWS Services for IoT SSH
Several AWS services are particularly relevant for remote IoT SSH:
- AWS IoT Core: Facilitates device connectivity and communication
- Amazon EC2: Provides virtual servers for hosting SSH-enabled IoT applications
- AWS Lambda: Enables serverless computing for automating IoT workflows
Setting Up Remote IoT SSH on AWS
Setting up remote IoT SSH on AWS involves several key steps. From configuring AWS services to establishing SSH connections, this section will guide you through the entire process.
Step 1: Creating an AWS Account
Begin by signing up for an AWS account if you haven't already. AWS offers a free tier for new users, allowing you to experiment with various services without incurring costs.
Read also:76ers Vs Thunder A Deep Dive Into The Rivalry Stats And Game Analysis
Step 2: Configuring AWS IoT Core
Set up AWS IoT Core to manage your IoT devices. This includes registering devices, configuring security policies, and establishing communication protocols.
Step 3: Launching an EC2 Instance
Create an Amazon EC2 instance to host your SSH-enabled IoT application. Choose an appropriate instance type based on your workload requirements and configure security groups to allow SSH access.
Securing IoT Devices with SSH
Security is paramount when implementing remote IoT SSH solutions. By following best practices, you can ensure your IoT devices are protected from potential threats.
Best Practices for SSH Security
- Use strong, unique passwords or SSH keys for authentication
- Disable password authentication in favor of public key authentication
- Restrict SSH access to specific IP addresses using security groups
Optimizing SSH Performance on AWS
Optimizing SSH performance is crucial for maintaining efficient IoT operations. By fine-tuning your AWS configuration and leveraging advanced features, you can enhance the speed and reliability of your SSH connections.
Tips for Improving SSH Performance
- Use compression to reduce data transfer times
- Enable keepalive settings to maintain persistent connections
- Optimize network configurations to minimize latency
Troubleshooting Common Issues
Despite careful planning, issues may arise when implementing remote IoT SSH on AWS. This section will address common challenges and provide solutions to help you overcome them.
Common SSH Issues and Solutions
- Connection timeouts: Check firewall settings and ensure proper port configurations
- Authentication failures: Verify SSH keys and ensure correct permissions
- Performance bottlenecks: Analyze network traffic and optimize resource allocation
Best Practices for Remote IoT SSH
Adopting best practices is essential for successful implementation of remote IoT SSH on AWS. From security to scalability, this section will outline key strategies to ensure your solution is effective and sustainable.
Strategies for Success
- Regularly update SSH software to patch vulnerabilities
- Monitor system logs for suspicious activities
- Plan for scalability to accommodate future growth
Real-World Applications
Remote IoT SSH on AWS has numerous practical applications across various industries. From smart homes to industrial automation, this technology is transforming the way businesses operate.
Industry Use Cases
- Smart agriculture: Monitor and control irrigation systems remotely
- Healthcare: Enable secure access to medical devices for remote diagnostics
- Manufacturing: Automate production processes and perform predictive maintenance
Future Trends in Remote IoT SSH
As technology continues to evolve, new trends are emerging in the field of remote IoT SSH. From advancements in quantum encryption to the integration of artificial intelligence, the future holds exciting possibilities for IoT security and connectivity.
Emerging Technologies
- Quantum encryption for unbreakable security
- AI-driven threat detection and response
- 5G networks for ultra-fast and reliable connectivity
Conclusion and Next Steps
Remote IoT SSH on AWS represents a powerful solution for secure and efficient IoT operations. By following the guidelines outlined in this article, you can successfully implement this technology and unlock its full potential. Remember to prioritize security, scalability, and performance to ensure your IoT ecosystem remains robust and reliable.
We encourage you to take the next step by experimenting with AWS services and exploring additional resources. Don't forget to share your thoughts and experiences in the comments section below. For more in-depth insights, consider reading our related articles on IoT and cloud computing.