In today's interconnected world, learning how to connect SSH IoT devices over the internet using AWS on Windows has become essential for developers, engineers, and tech enthusiasts. With the rapid growth of IoT technology, managing and securing remote devices has never been more critical. This guide will walk you through the process step-by-step, ensuring you understand the best practices and tools to achieve seamless connectivity.
As the Internet of Things (IoT) continues to expand, connecting devices securely over the internet has become a top priority. Whether you're setting up a smart home system, managing industrial sensors, or deploying IoT applications, mastering SSH connections on AWS through Windows is a valuable skill. This article will provide you with practical insights into the tools, configurations, and security measures required to make it happen.
This guide is tailored for readers who want to dive deep into the technical aspects of IoT connectivity. By the end of this article, you'll have a clear understanding of how to connect SSH IoT devices over the internet using AWS on Windows. Let's get started!
Read also:Will Wade The Rising Star In Basketball Coaching
Table of Contents
1. Introduction to SSH IoT Device Connectivity
2. Understanding the Basics of SSH and IoT
3. Prerequisites for Connecting SSH IoT Devices
4. Setting Up AWS for IoT SSH Connections
5. Configuring Windows for SSH IoT Connectivity
6. Securing Your SSH IoT Connections
Read also:India Vs Maldives A Comprehensive Analysis Of Their Relations And Key Comparisons
7. Common Issues and Troubleshooting Tips
8. Advanced Configurations for Enhanced Connectivity
9. Best Practices for Managing IoT Devices Over SSH
Introduction to SSH IoT Device Connectivity
Connecting SSH IoT devices over the internet using AWS on Windows is a powerful way to manage remote systems securely. Secure Shell (SSH) provides an encrypted channel for communication, ensuring that your data remains protected during transmission. This section will introduce you to the concept of SSH and its importance in IoT applications.
With AWS offering robust cloud infrastructure, developers can leverage its services to create scalable and secure IoT solutions. By integrating Windows into the mix, you gain access to a familiar environment for managing your SSH connections. This combination enables you to streamline your workflow and improve efficiency in IoT management.
Understanding the Basics of SSH and IoT
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote system administration and file transfer. When connecting SSH IoT devices, you can ensure that commands and data are transmitted securely, reducing the risk of unauthorized access.
The Role of IoT in Modern Technology
IoT refers to the network of physical devices embedded with sensors, software, and connectivity features, enabling them to exchange data. IoT devices are prevalent in various industries, including healthcare, manufacturing, and smart homes. Connecting these devices over the internet using SSH ensures that they remain accessible and manageable from anywhere in the world.
Prerequisites for Connecting SSH IoT Devices
Before diving into the process, ensure you have the following prerequisites in place:
- AWS account with necessary permissions
- A Windows machine with SSH client installed
- An IoT device with SSH capabilities
- Basic knowledge of networking and cloud computing
Having these prerequisites will make the setup process smoother and more efficient.
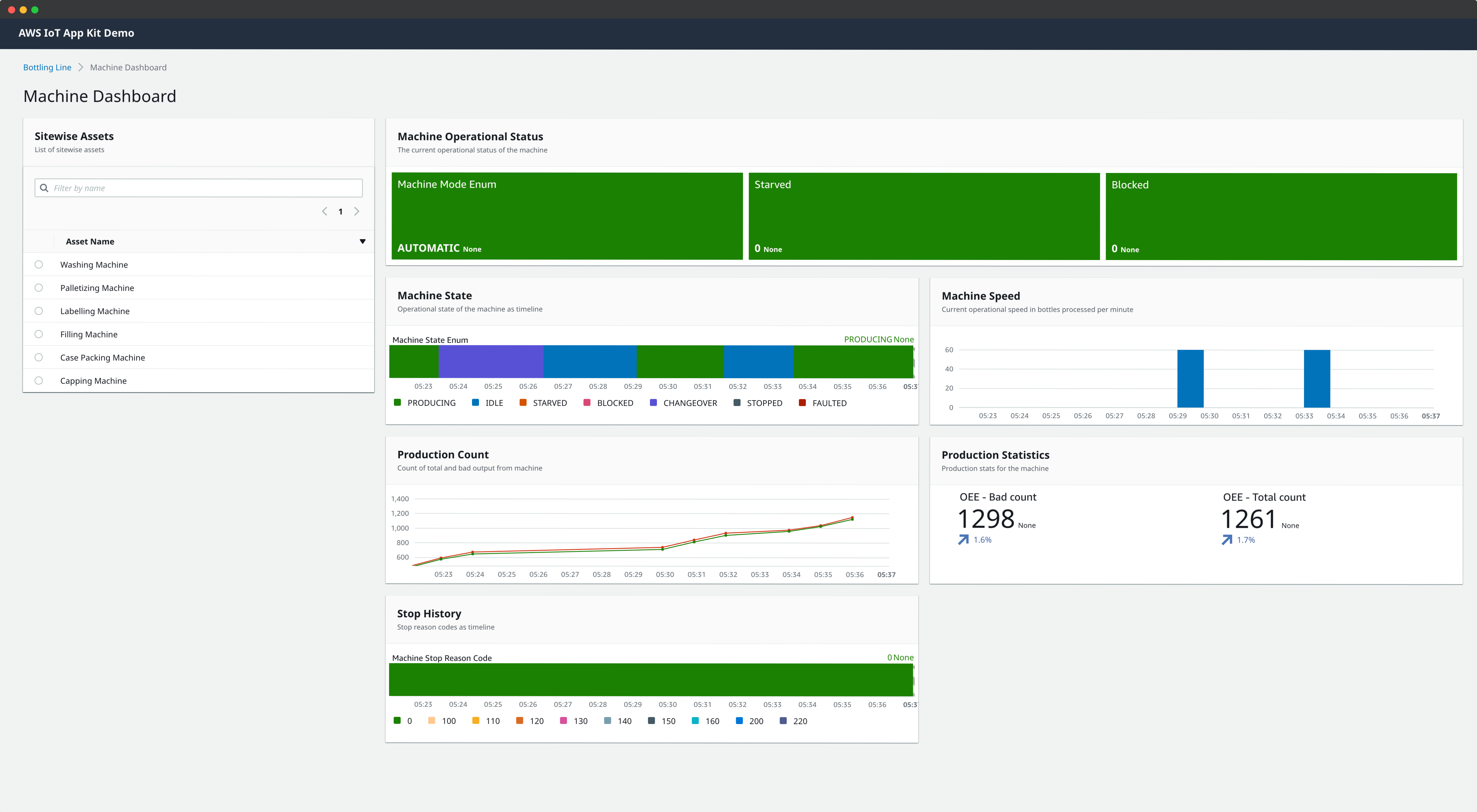
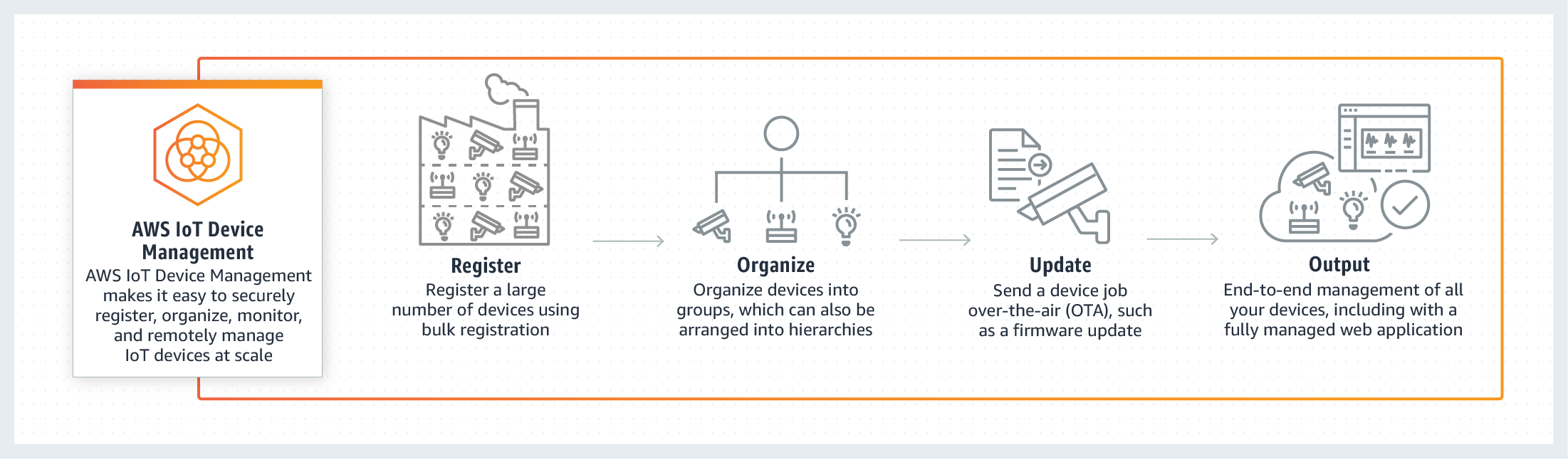
Setting Up AWS for IoT SSH Connections
Creating an AWS IoT Core Account
To begin, create an AWS IoT Core account. This service allows you to securely interact with IoT devices over the internet. Follow the official AWS documentation to set up your account and configure the necessary permissions.
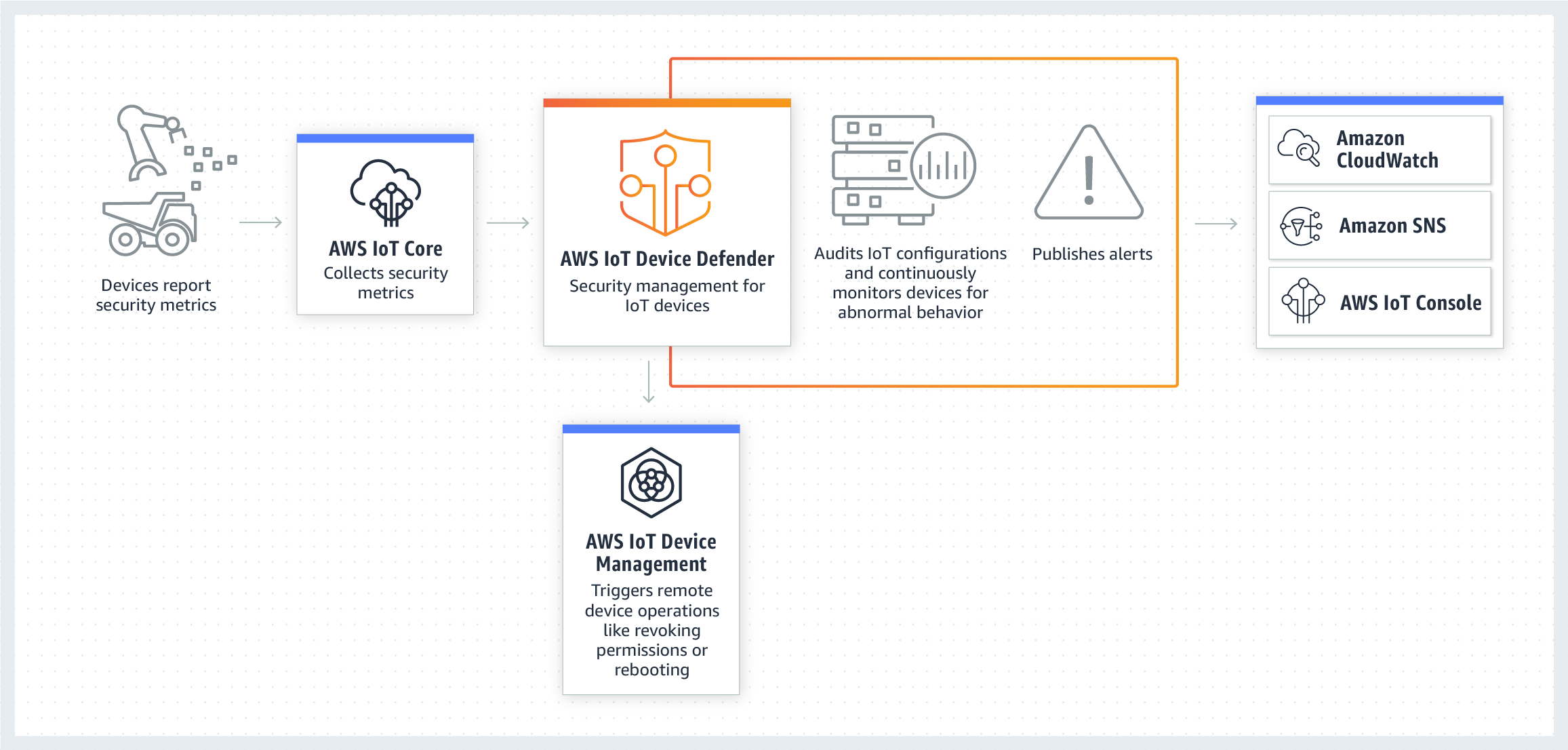
Configuring Security Policies
Security is paramount when managing IoT devices over the internet. Use AWS Identity and Access Management (IAM) to define policies that restrict access to your IoT devices. Ensure that only authorized users can establish SSH connections to your devices.
Configuring Windows for SSH IoT Connectivity
On your Windows machine, install an SSH client such as PuTTY or OpenSSH. These tools enable you to establish secure connections to your IoT devices. Configure the client to use the appropriate port and authentication method, such as public key authentication, to enhance security.
Securing Your SSH IoT Connections
Securing your SSH connections is crucial to protect your IoT devices from unauthorized access. Implement the following best practices:
- Use strong, unique passwords or public key authentication
- Disable root login to prevent direct access to critical systems
- Set up a firewall to restrict incoming connections
- Regularly update your devices and software to patch vulnerabilities
By following these steps, you can significantly reduce the risk of security breaches.
Common Issues and Troubleshooting Tips
Connection Timeouts
If you encounter connection timeouts, verify that your network settings are correct and that there are no firewalls blocking the SSH port. Additionally, ensure that your IoT device is online and reachable.
Authentication Failures
Authentication failures often occur due to incorrect credentials or misconfigured keys. Double-check your authentication settings and regenerate keys if necessary.
Advanced Configurations for Enhanced Connectivity
For advanced users, consider implementing additional features such as:
- SSH tunneling for secure data transfer
- Automated scripts for routine maintenance tasks
- Monitoring tools to track device performance and security
These configurations can enhance the functionality and reliability of your IoT setup.
Best Practices for Managing IoT Devices Over SSH
Adopting best practices ensures that your IoT devices remain secure and efficient. Some key practices include:
- Regularly reviewing access logs for suspicious activity
- Implementing multi-factor authentication for added security
- Documenting your setup and configurations for future reference
By following these guidelines, you can maintain a robust and secure IoT environment.
Conclusion and Next Steps
In conclusion, learning how to connect SSH IoT devices over the internet using AWS on Windows is a valuable skill in today's tech-driven world. By understanding the basics of SSH, configuring your AWS account, and securing your connections, you can effectively manage remote IoT devices. This guide has provided you with the tools and knowledge to achieve seamless connectivity.
We encourage you to take the next step by experimenting with the configurations discussed here. Share your experiences in the comments below and explore other articles on our site to deepen your understanding of IoT and cloud technologies. Together, let's build a more connected and secure future!
References: