RemoteIoT SSH AWS Example is a powerful solution that enables secure communication between IoT devices and AWS cloud services. As the Internet of Things (IoT) continues to grow, the need for secure and efficient data transfer becomes increasingly important. This article will delve into the intricacies of using SSH to connect IoT devices with AWS, offering a detailed guide for developers and IT professionals.
In today's digital age, IoT devices are becoming an integral part of our daily lives. From smart homes to industrial automation, IoT has revolutionized the way we interact with technology. However, ensuring secure communication between these devices and cloud platforms like AWS remains a critical challenge. This is where RemoteIoT SSH AWS Example comes into play, providing a robust framework for secure data exchange.
Whether you're a beginner or an experienced developer, this guide will walk you through the essential steps to implement SSH-based connections for IoT devices on AWS. By the end of this article, you'll have a solid understanding of the tools, techniques, and best practices needed to deploy and manage IoT devices securely.
Read also:Cia Unveiling The Role History And Impact Of The Central Intelligence Agency
Table of Contents
- Introduction to RemoteIoT SSH AWS
- Why Use SSH for RemoteIoT?
- Setting Up AWS Environment
- Connecting IoT Devices via SSH
- Securing Your Connection
- Example Use Cases
- Troubleshooting Common Issues
- Optimizing Performance
- Best Practices for RemoteIoT SSH AWS
- Conclusion and Next Steps
Introduction to RemoteIoT SSH AWS
RemoteIoT SSH AWS Example represents a cutting-edge approach to integrating IoT devices with Amazon Web Services (AWS). SSH, or Secure Shell, is a cryptographic protocol designed to secure network communications. By leveraging SSH, developers can establish encrypted connections between IoT devices and AWS resources, ensuring data integrity and confidentiality.
This section will provide an overview of the RemoteIoT SSH AWS framework, highlighting its key features and benefits. Additionally, we'll explore how this solution addresses common challenges faced in IoT deployments, such as security vulnerabilities and connectivity issues.
Why Use SSH for RemoteIoT?
SSH offers several advantages when it comes to securing IoT device communications. Below are some of the primary reasons why SSH is a preferred choice for RemoteIoT SSH AWS Example:
- Encryption: SSH encrypts all data transmitted between devices, preventing unauthorized access.
- Authentication: SSH supports strong authentication mechanisms, ensuring only authorized devices can connect.
- Reliability: SSH connections are reliable and can be configured to handle intermittent network conditions.
- Flexibility: SSH can be used with various operating systems and hardware platforms, making it versatile for IoT deployments.
Setting Up AWS Environment
Before deploying RemoteIoT SSH AWS Example, it's essential to configure your AWS environment properly. This involves creating and configuring AWS resources to support secure IoT device connections.
Creating an EC2 Instance
An Amazon EC2 instance serves as the server endpoint for your IoT devices. Follow these steps to create an EC2 instance:
- Log in to the AWS Management Console.
- Navigate to the EC2 dashboard and click "Launch Instance."
- Select an Amazon Machine Image (AMI) compatible with your IoT devices.
- Choose an instance type based on your performance requirements.
- Configure instance details, such as network settings and storage.
- Set up a key pair for SSH access.
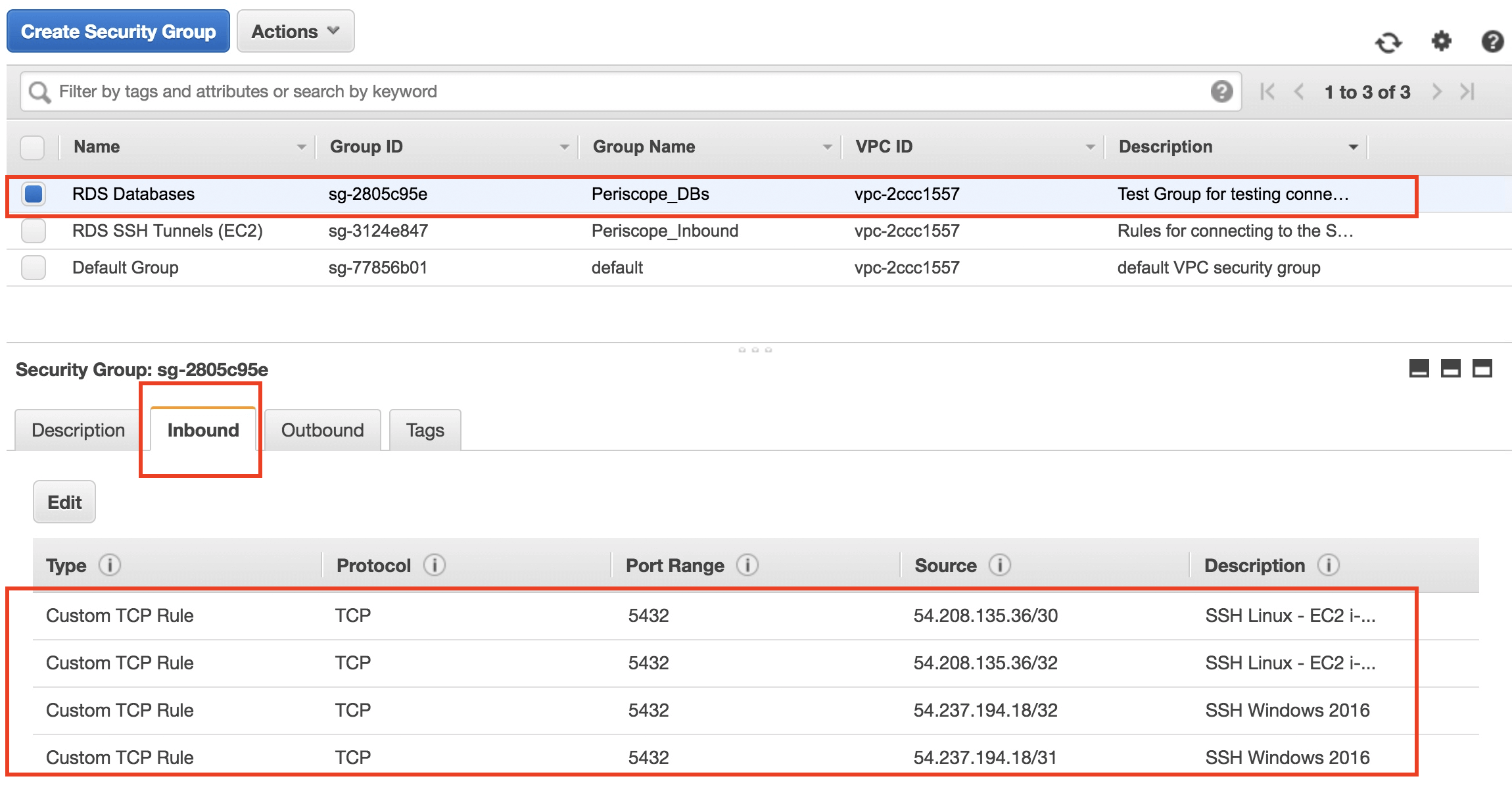
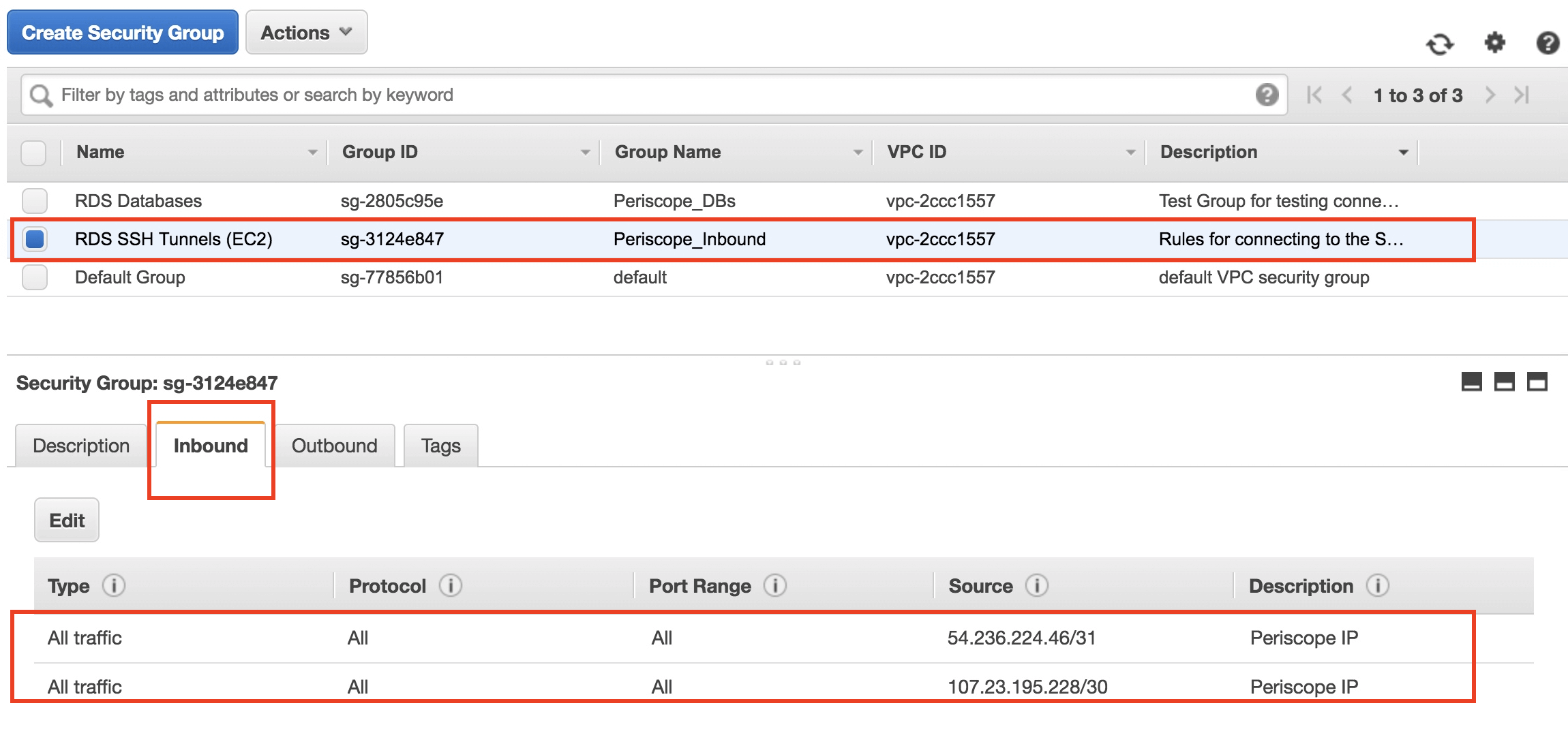
Configuring Security Groups
Security groups act as virtual firewalls for your EC2 instances. To allow SSH access, you need to configure the security group settings:
Read also:Alec Baldwin Wife A Comprehensive Look Into Her Life Career And Marriage
- Go to the EC2 dashboard and select "Security Groups."
- Create a new security group or edit an existing one.
- Add a rule to allow inbound SSH traffic (port 22) from trusted IP addresses.
- Save the changes and associate the security group with your EC2 instance.
Connecting IoT Devices via SSH
Once your AWS environment is set up, the next step is to connect your IoT devices using SSH. This section will guide you through the process of establishing secure SSH connections:
- Generate SSH Keys: Use tools like OpenSSL or ssh-keygen to generate public and private key pairs for authentication.
- Install SSH Client: Ensure your IoT devices have an SSH client installed and configured.
- Test the Connection: Use the SSH command to connect to your EC2 instance and verify the connection.
Securing Your Connection
Security is paramount when dealing with IoT devices and cloud services. Implement the following best practices to enhance the security of your RemoteIoT SSH AWS Example:
- Use Strong Passwords: Avoid using default passwords and opt for complex, unique credentials.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by requiring 2FA for SSH access.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities.
Example Use Cases
RemoteIoT SSH AWS Example can be applied in various real-world scenarios. Below are some example use cases:
- Smart Agriculture: Use SSH to securely monitor and control irrigation systems in remote locations.
- Industrial Automation: Implement SSH-based connections for factory equipment to enable remote diagnostics.
- Home Automation: Securely manage smart home devices through SSH tunnels to ensure privacy.
Troubleshooting Common Issues
While setting up RemoteIoT SSH AWS Example, you may encounter some challenges. Here are solutions to common issues:
- Connection Refused: Verify that the security group rules allow SSH traffic and the EC2 instance is running.
- Authentication Failed: Check the correctness of your SSH keys and ensure they are properly configured.
- Timeout Errors: Optimize network settings and ensure stable internet connectivity for your IoT devices.
Optimizing Performance
To ensure optimal performance of your RemoteIoT SSH AWS Example, consider the following strategies:
- Compress Data: Use compression techniques to reduce the size of transmitted data, improving transfer speeds.
- Implement Load Balancing: Distribute traffic across multiple EC2 instances to handle high workloads efficiently.
- Monitor Resource Usage: Keep track of CPU, memory, and network usage to identify and address bottlenecks.
Best Practices for RemoteIoT SSH AWS
Adhering to best practices is crucial for successful implementation of RemoteIoT SSH AWS Example. Follow these guidelines to maximize efficiency and security:
- Regular Updates: Keep your AWS environment and IoT devices up to date with the latest security patches.
- Documentation: Maintain comprehensive documentation of your setup and configurations for future reference.
- Testing: Conduct thorough testing of your SSH connections under different scenarios to ensure reliability.
Conclusion and Next Steps
In conclusion, RemoteIoT SSH AWS Example provides a reliable and secure solution for connecting IoT devices with AWS cloud services. By following the steps outlined in this guide, you can successfully deploy and manage IoT devices in your network. Remember to adhere to best practices and continuously monitor your system for optimal performance and security.
We encourage you to take the following actions:
- Leave a comment sharing your experience with RemoteIoT SSH AWS Example.
- Explore additional resources and tutorials on our website to deepen your knowledge.
- Subscribe to our newsletter for updates on the latest developments in IoT and cloud technologies.
For further reading, refer to authoritative sources such as AWS IoT Documentation and OpenSSH Official Website. Together, let's build a secure and connected future with RemoteIoT SSH AWS Example!