In today's hyper-connected world, the ability to manage and control devices remotely is no longer a luxury but a necessity. Best remote SSH IoT over internet AWS free solutions provide an affordable and efficient way to access and manage IoT devices from anywhere in the world. With the rapid advancement of technology, businesses and individuals can now harness the power of cloud computing to streamline operations and enhance productivity.
As remote work becomes increasingly common, the demand for secure and reliable remote access solutions continues to grow. AWS Free Tier offers an excellent opportunity for developers, hobbyists, and businesses to explore the potential of remote SSH IoT over the internet without breaking the bank. By leveraging this powerful combination, users can unlock new possibilities for automation, monitoring, and control.
In this comprehensive guide, we will delve into the intricacies of setting up and managing remote SSH IoT connections using AWS Free Tier. From understanding the basics to exploring advanced configurations, this article will equip you with the knowledge and tools needed to take full advantage of this cutting-edge technology.
Read also:Grizzlies Vs Trail Blazers A Deep Dive Into The Thrilling Nba Rivalry
Table of Contents
- Introduction to Remote SSH IoT
- AWS Free Tier Overview
- Benefits of Remote SSH IoT
- Setting Up SSH on AWS
- Securing Your Remote SSH Connection
- Optimizing Performance
- Troubleshooting Common Issues
- Best Practices for Remote SSH IoT
- Case Studies and Examples
- Conclusion and Next Steps
Introduction to Remote SSH IoT
Remote SSH IoT refers to the practice of using Secure Shell (SSH) protocols to establish secure and encrypted connections between IoT devices and remote servers or clients. This technology enables users to manage, monitor, and control IoT devices from anywhere in the world, provided they have internet access. The integration of SSH with IoT devices ensures secure communication, data integrity, and privacy.
With the proliferation of smart devices and the Internet of Things, the need for robust remote management solutions has never been greater. The best remote SSH IoT solutions offer a seamless way to interact with devices, whether for personal or commercial purposes.
In this section, we will explore the fundamental concepts of remote SSH IoT, its applications, and why it is essential in today's digital landscape.
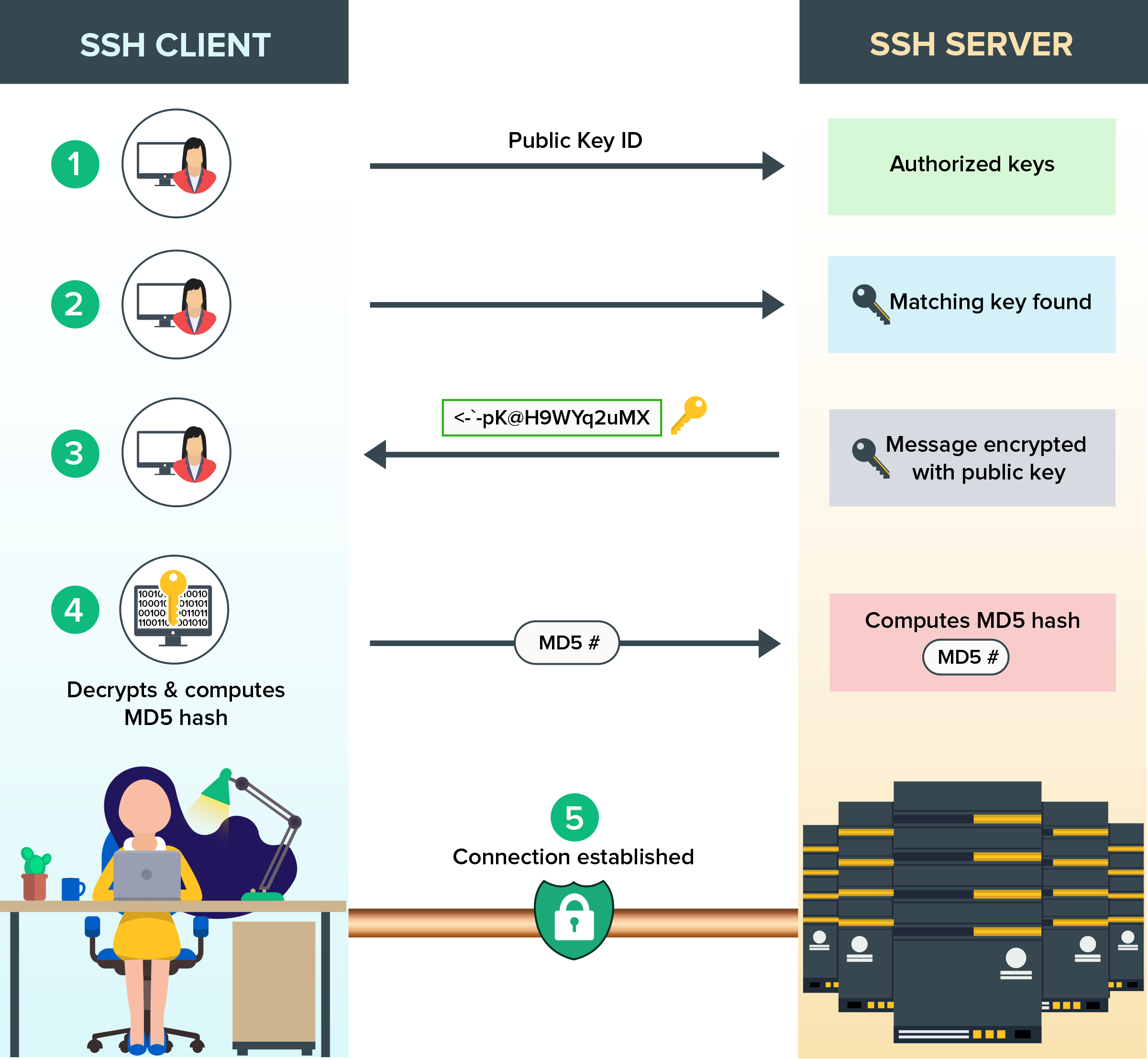
Understanding SSH Protocol
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over an unsecured network. It is widely used for remote login and other secure network services. By encrypting all data transmitted between devices, SSH ensures that sensitive information remains protected from unauthorized access.
- SSH provides secure authentication and encryption for remote connections.
- It supports various authentication methods, including password-based and public key authentication.
- SSH is widely supported across multiple platforms, making it a versatile solution for remote access.
AWS Free Tier Overview
AWS Free Tier offers a generous allowance for new users to explore and experiment with Amazon Web Services. This includes access to essential services such as EC2 instances, S3 storage, and database solutions. For those looking to implement remote SSH IoT over the internet, AWS Free Tier provides the perfect platform to get started without incurring any costs.
With AWS Free Tier, users can launch and manage virtual servers, store data, and deploy applications. The free tier is ideal for developers, hobbyists, and small businesses looking to test and deploy IoT solutions without committing to long-term expenses.
Read also:Dolly Parton A Legacy Of Music Philanthropy And Empowerment
Key Features of AWS Free Tier
- 750 hours per month of EC2 t2.micro instance usage.
- 5 GB of S3 storage and 20,000 GET requests per month.
- Up to 1 million free requests for AWS Lambda.
Benefits of Remote SSH IoT
Implementing remote SSH IoT solutions offers numerous advantages for both individuals and organizations. From enhanced security to increased flexibility, the benefits of this technology are undeniable. Below, we explore some of the key advantages of adopting remote SSH IoT over the internet.
Enhanced Security
SSH provides a secure channel for data transmission, protecting sensitive information from interception and unauthorized access. By encrypting all communication between devices, SSH ensures that data remains confidential and secure.
Increased Flexibility
With remote SSH IoT, users can access and manage devices from anywhere in the world. This flexibility is particularly beneficial for businesses with distributed teams or remote workers who need to monitor and control IoT devices in real-time.
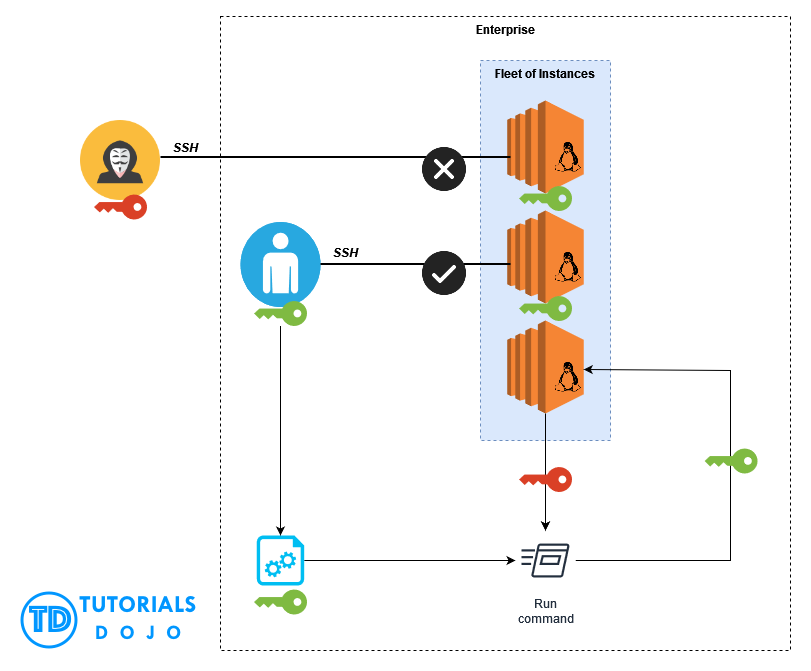
Setting Up SSH on AWS
Setting up SSH on AWS involves several steps, from launching an EC2 instance to configuring security groups and generating SSH keys. Below, we provide a step-by-step guide to help you get started with remote SSH IoT on AWS Free Tier.
Step 1: Launch an EC2 Instance
Begin by launching an EC2 instance through the AWS Management Console. Choose an appropriate AMI (Amazon Machine Image) and instance type, ensuring that it meets your requirements for remote SSH IoT.
Step 2: Configure Security Groups
Security groups act as virtual firewalls for your EC2 instances. Configure your security group to allow inbound SSH traffic on port 22, ensuring that only authorized IP addresses can access your instance.
Step 3: Generate SSH Keys
Create an SSH key pair using the AWS Management Console or a third-party tool like PuTTY. Save the private key securely, as it will be required for authentication when connecting to your EC2 instance.
Securing Your Remote SSH Connection
While SSH provides a secure method for remote access, it is essential to implement additional security measures to protect your IoT devices and data. Below, we outline some best practices for securing your remote SSH connection.
Use Strong Passwords and Public Key Authentication
Avoid using weak passwords and enable public key authentication for added security. Public key authentication eliminates the need for password-based login, reducing the risk of brute-force attacks.
Disable Root Login
Disable root login to prevent unauthorized users from gaining administrative access to your system. Instead, create a separate user account with limited privileges for remote access.
Optimizing Performance
To ensure optimal performance of your remote SSH IoT setup, consider the following tips:
Choose the Right Instance Type
Select an EC2 instance type that aligns with your workload requirements. For lightweight IoT applications, a t2.micro instance may suffice, but more demanding applications may require a more powerful instance type.
Monitor Resource Usage
Regularly monitor CPU, memory, and network usage to identify potential bottlenecks and optimize performance. AWS CloudWatch provides valuable insights into resource utilization and can help you make informed decisions about scaling your infrastructure.
Troubleshooting Common Issues
Despite careful planning and configuration, issues may arise when setting up remote SSH IoT on AWS. Below, we address some common problems and provide solutions to help you overcome them.
Connection Timeouts
Connection timeouts are often caused by misconfigured security groups or incorrect SSH key settings. Verify that your security group allows inbound SSH traffic and ensure that your private key matches the public key stored on your EC2 instance.
Authentication Failures
Authentication failures may occur if the private key is corrupted or if the permissions on the key file are incorrect. Ensure that the private key file has the correct permissions (e.g., 400) and that it is being used correctly during the SSH connection process.
Best Practices for Remote SSH IoT
To maximize the benefits of remote SSH IoT, adhere to the following best practices:
Regularly Update Software
Keep your operating system, SSH server, and other software up to date to protect against vulnerabilities and ensure optimal performance.
Implement Logging and Monitoring
Enable logging and monitoring to track system activity and detect potential security threats. AWS CloudTrail and CloudWatch can be invaluable tools for monitoring your infrastructure.
Case Studies and Examples
Real-world examples and case studies can provide valuable insights into the practical applications of remote SSH IoT. Below, we present two examples of organizations successfully implementing this technology:
Case Study 1: Smart Agriculture
Agricultural company XYZ implemented remote SSH IoT to monitor and control irrigation systems in real-time. By leveraging AWS Free Tier, the company was able to reduce water wastage and improve crop yields without incurring significant costs.
Case Study 2: Home Automation
Individual user John Doe used remote SSH IoT to manage smart home devices, including lighting and climate control systems. With AWS Free Tier, John was able to access and control his devices from anywhere in the world, enhancing convenience and security.
Conclusion and Next Steps
In conclusion, the best remote SSH IoT over internet AWS free solutions offer a powerful and cost-effective way to manage and control IoT devices remotely. By following the guidelines and best practices outlined in this article, you can unlock the full potential of this technology and enhance your digital infrastructure.
We encourage you to take the next step by experimenting with AWS Free Tier and exploring the possibilities of remote SSH IoT. Leave a comment below to share your experiences or ask questions, and don't forget to share this article with others who may find it useful. Together, let's build a smarter, more connected world!