Connecting remote IoT devices to AWS securely is a critical need for modern businesses and hobbyists alike. Whether you're managing home automation systems or deploying industrial-scale IoT solutions, ensuring secure communication is paramount. This guide will walk you through the process of securely connecting a Raspberry Pi to an AWS VPC, providing you with a free and efficient setup.
In today's digital age, the Internet of Things (IoT) has revolutionized how we interact with technology. From smart homes to industrial automation, IoT devices are becoming increasingly common. However, with this growth comes the challenge of ensuring that these devices communicate securely over the internet.
This article aims to provide you with a step-by-step guide to setting up a secure connection between your Raspberry Pi and AWS Virtual Private Cloud (VPC) without incurring unnecessary costs. By following this guide, you'll be able to protect your IoT devices and data while leveraging AWS's powerful infrastructure.
Read also:Meet Melanie Jolys Kids A Closer Look At Her Family Life
Table of Contents
- Introduction
- Why Securely Connect Remote IoT Devices?
- Raspberry Pi Overview
- AWS VPC Explained
- Setup Process
- Securing the Connection
- Best Practices for IoT Security
- Troubleshooting Common Issues
- Cost Analysis: Free vs Paid Options
- Conclusion
Introduction
The concept of connecting remote IoT devices to AWS securely has become a cornerstone of modern technology. IoT devices, such as Raspberry Pi, are often deployed in remote locations, making it essential to establish a secure connection to ensure data integrity and device safety. AWS provides a robust infrastructure for hosting and managing IoT devices through its Virtual Private Cloud (VPC) service.
This guide will focus on securely connecting a Raspberry Pi to an AWS VPC using free resources. By leveraging AWS's free tier and open-source tools, you can create a secure and cost-effective solution for managing your IoT devices.
Whether you're a hobbyist experimenting with smart home projects or a professional deploying industrial IoT solutions, this guide will provide you with the knowledge and tools needed to set up a secure connection.
Why Securely Connect Remote IoT Devices?
IoT devices are increasingly becoming targets for cyberattacks due to their often-limited security measures. A secure connection ensures that your data is protected from unauthorized access and potential breaches. Here are some reasons why securely connecting remote IoT devices is crucial:
- Data Protection: Prevent unauthorized access to sensitive data transmitted between devices and servers.
- Device Safety: Protect your IoT devices from malicious attacks and unauthorized control.
- Regulatory Compliance: Ensure compliance with industry standards and regulations, such as GDPR and HIPAA.
By following best practices and using secure protocols, you can minimize the risks associated with IoT deployments.
Raspberry Pi Overview
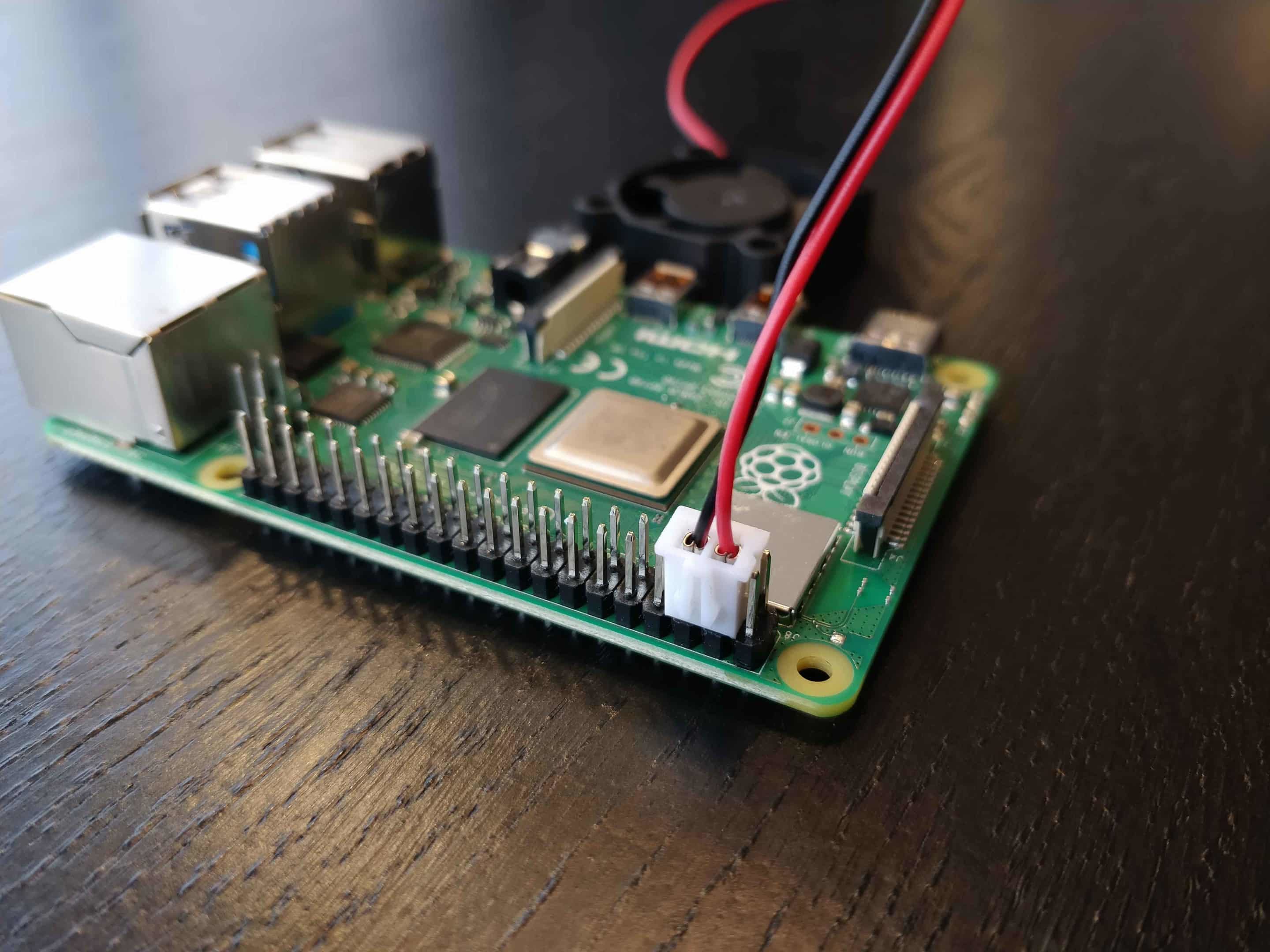
The Raspberry Pi is a popular single-board computer used for a wide range of applications, from educational projects to industrial automation. Its affordability, versatility, and open-source nature make it an ideal choice for IoT projects. Here are some key features of the Raspberry Pi:
Read also:Dolly Parton A Legacy Of Music Philanthropy And Empowerment
- Compact Size: Small form factor makes it easy to deploy in tight spaces.
- Low Power Consumption: Ideal for battery-powered devices.
- Community Support: A vast community of developers and enthusiasts provides extensive resources and support.
When connecting a Raspberry Pi to AWS, it's essential to ensure that the device is configured securely to prevent unauthorized access.
AWS VPC Explained
Amazon Web Services (AWS) Virtual Private Cloud (VPC) is a secure and isolated network environment where you can launch AWS resources. By using VPC, you can control the network configuration and manage access to your resources. Key features of AWS VPC include:
- Private Subnets: Isolate resources from the public internet.
- Security Groups: Control inbound and outbound traffic to your instances.
- Network Access Control Lists (ACLs): Add an additional layer of security by defining rules for traffic.
Using AWS VPC ensures that your IoT devices are protected from unauthorized access while still allowing secure communication with your cloud resources.
Setup Process
Step 1: Create a Free AWS Account
Before you begin, you'll need to create a free AWS account. AWS offers a free tier that includes many services for one year, making it an ideal choice for hobbyists and small-scale projects. Here's how to create an account:
- Visit the AWS Free Tier page.
- Sign up for an account using your email address or social media credentials.
- Verify your account and complete the registration process.
Once your account is set up, you can begin configuring your AWS VPC.
Step 2: Set Up Your Raspberry Pi
To connect your Raspberry Pi to AWS, you'll need to configure it properly. Follow these steps to set up your Raspberry Pi:
- Install the latest version of Raspberry Pi OS on your device.
- Enable SSH and configure Wi-Fi settings using the Raspberry Pi Configuration tool.
- Update the operating system and install any necessary software.
With your Raspberry Pi configured, you can proceed to set up the AWS VPC.
Step 3: Configure VPC
Configuring your AWS VPC involves several steps to ensure a secure connection. Here's a brief overview of the process:
- Create a new VPC in the AWS Management Console.
- Set up subnets and routing tables to define network traffic rules.
- Configure security groups to control access to your instances.
Once your VPC is configured, you can connect your Raspberry Pi to it using secure protocols.
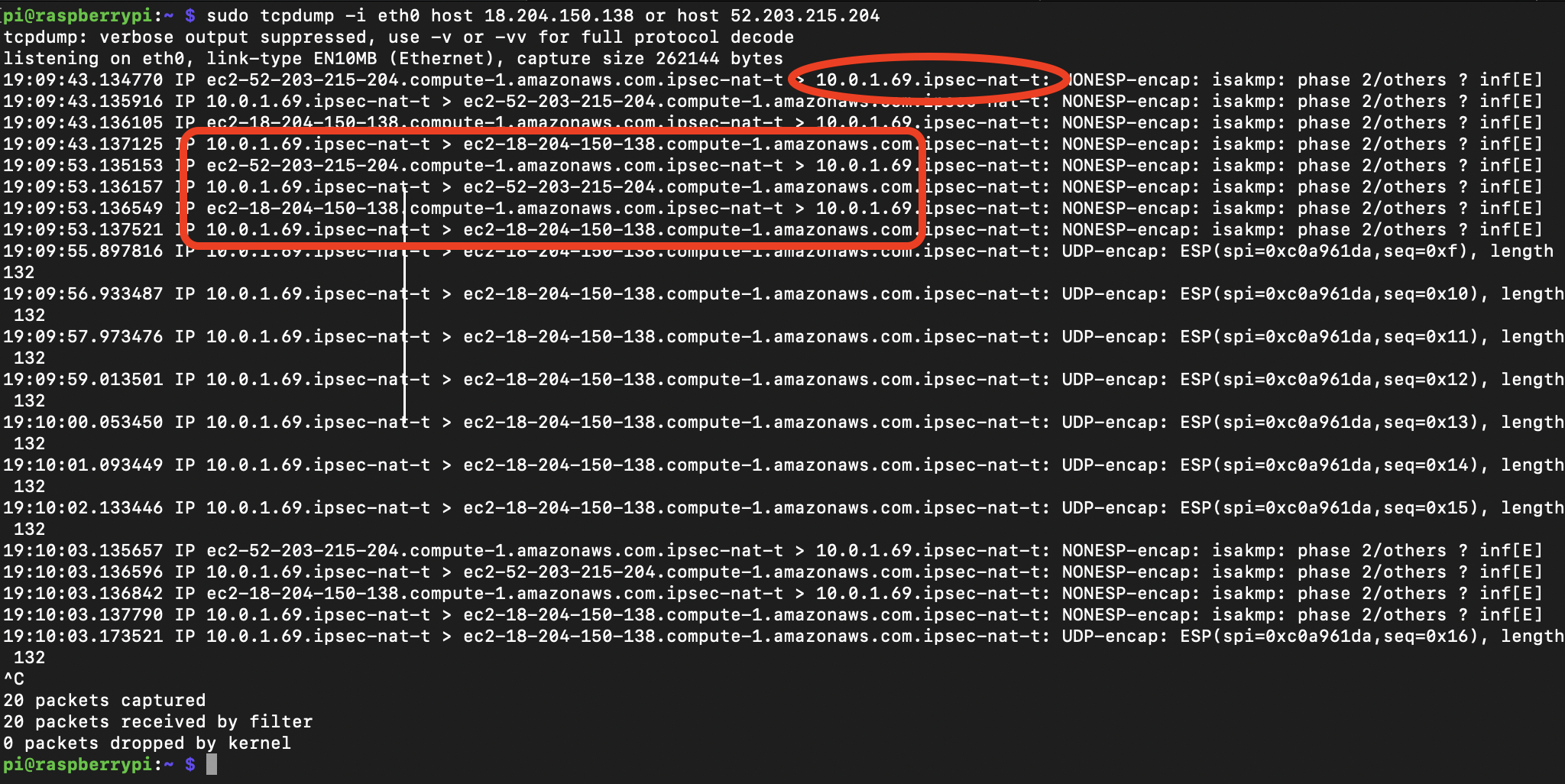
Securing the Connection
Securing the connection between your Raspberry Pi and AWS VPC is critical to protecting your data and devices. Here are some steps you can take to enhance security:
- Use SSL/TLS: Encrypt data transmitted between your devices and servers.
- Implement Authentication: Use strong passwords and multi-factor authentication for added security.
- Regularly Update Firmware: Keep your Raspberry Pi and AWS services up to date to protect against vulnerabilities.
By following these steps, you can ensure that your IoT devices are protected from potential threats.
Best Practices for IoT Security
Implementing best practices for IoT security is essential for maintaining the integrity of your devices and data. Here are some recommendations:
- Segment Networks: Isolate IoT devices from other networks to minimize risks.
- Monitor Traffic: Use network monitoring tools to detect and respond to suspicious activity.
- Regular Audits: Conduct regular security audits to identify and address vulnerabilities.
By adhering to these best practices, you can create a secure and reliable IoT environment.
Troubleshooting Common Issues
Even with careful planning, issues may arise when setting up your IoT environment. Here are some common problems and their solutions:
- Connection Issues: Check network settings and ensure that security groups allow necessary traffic.
- Authentication Failures: Verify credentials and ensure that authentication protocols are correctly configured.
- Performance Problems: Optimize resource allocation and monitor system performance to identify bottlenecks.
By addressing these issues promptly, you can ensure a smooth and secure IoT deployment.
Cost Analysis: Free vs Paid Options
AWS offers a free tier that includes many services for one year, making it an attractive option for small-scale projects. However, as your IoT deployment grows, you may need to consider paid options to meet your needs. Here's a breakdown of costs:
- Free Tier: Ideal for hobbyists and small-scale projects, includes many services for one year.
- Paid Services: Offer advanced features and scalability for larger deployments.
By carefully evaluating your requirements, you can choose the option that best fits your budget and needs.
Conclusion
Securing the connection between your Raspberry Pi and AWS VPC is essential for protecting your IoT devices and data. By following the steps outlined in this guide, you can create a secure and cost-effective solution for managing your IoT devices. Remember to implement best practices for IoT security and regularly monitor your environment for potential threats.
We encourage you to share your experiences and insights in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT and cloud computing. Together, we can build a safer and more connected world.
References: