In today's interconnected world, remote access to IoT devices is becoming increasingly essential for businesses and individuals alike. Whether it's managing smart home appliances or monitoring industrial equipment, the ability to connect remotely is indispensable. However, ensuring secure remote access without relying on third-party tools can be challenging. This article delves into how you can achieve secure remote access to IoT devices using SSH on Windows 10 without the need for additional software.
As the Internet of Things (IoT) continues to expand, so does the need for secure and reliable remote access solutions. With Windows 10 offering built-in tools like SSH, users can establish secure connections to IoT devices without the hassle of installing extra applications. This approach not only simplifies the process but also enhances security by minimizing dependencies on external tools.
In this comprehensive guide, we will explore the step-by-step process of setting up SSH for remote access, discuss best practices for security, and provide valuable tips to ensure a seamless experience. Whether you're a tech enthusiast or a professional looking to streamline your operations, this article is your go-to resource for mastering remote access to IoT devices on Windows 10.
Read also:Christina Applegate A Journey Through Her Life Career And Achievements
Table of Contents
- Introduction to Remote Access and IoT
- What is SSH and Why Use It?
- Enabling SSH on Windows 10
- Setting Up IoT Devices for SSH
- Connecting to IoT Devices via SSH
- Security Best Practices for SSH
- Troubleshooting Common Issues
- Benefits of Using SSH for IoT Remote Access
- Alternatives to SSH for Remote Access
- Conclusion and Next Steps
Introduction to Remote Access and IoT
Remote access refers to the ability to connect to and control devices or systems from a distant location. In the context of IoT, this capability allows users to manage and monitor connected devices, such as sensors, cameras, and smart home appliances, without being physically present. The importance of remote access in IoT cannot be overstated, as it enables efficient device management, real-time data collection, and improved operational efficiency.
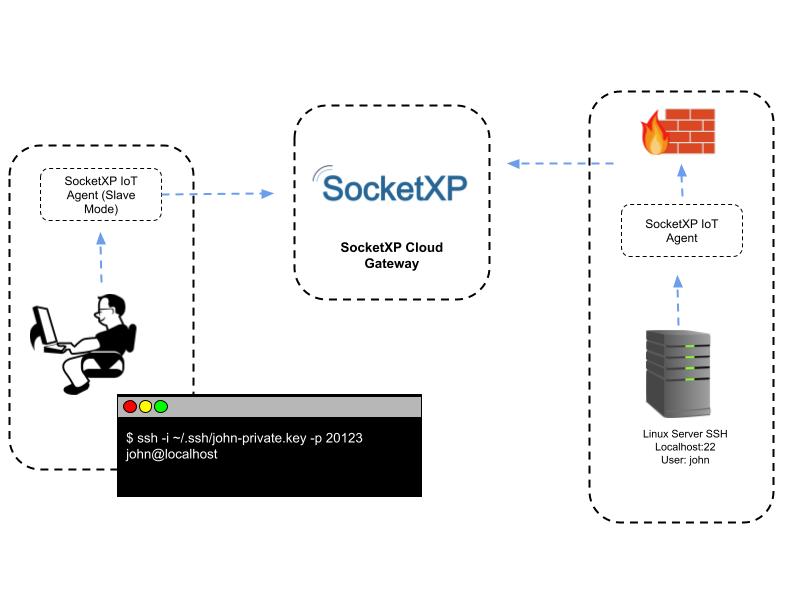
While there are numerous methods for achieving remote access, SSH (Secure Shell) stands out as one of the most secure and reliable options. Unlike other protocols, SSH encrypts all data transmitted between the client and server, ensuring confidentiality and integrity. This makes it an ideal choice for remote access to IoT devices, especially when sensitive information is involved.
Why Choose SSH for IoT Devices?
SSH offers several advantages for IoT remote access, including:
- Encryption for secure communication
- Authentication mechanisms to ensure authorized access
- Compatibility with a wide range of devices and platforms
- Support for command-line interfaces for efficient device management
What is SSH and Why Use It?
SSH, or Secure Shell, is a network protocol that provides a secure way to access remote devices over an unsecured network. It uses encryption to protect data in transit, making it an essential tool for secure remote access. SSH is widely used in IT infrastructure management, server administration, and IoT device control due to its robust security features and ease of use.
One of the key reasons to use SSH for IoT remote access is its ability to prevent unauthorized access and data breaches. By implementing strong authentication methods, such as public key authentication, SSH ensures that only authorized users can connect to IoT devices. Additionally, SSH supports various encryption algorithms, allowing users to choose the level of security that best suits their needs.
SSH vs. Other Remote Access Protocols
Compared to other remote access protocols like Telnet or FTP, SSH offers superior security and reliability. While Telnet transmits data in plain text, making it vulnerable to eavesdropping, SSH encrypts all communication, ensuring that sensitive information remains confidential. Similarly, FTP lacks built-in security features, whereas SSH provides a secure channel for file transfers through SFTP (Secure File Transfer Protocol).
Read also:Social Security Identity Verification A Comprehensive Guide To Protecting Your Identity
Enabling SSH on Windows 10
Windows 10 includes built-in support for SSH, allowing users to establish secure connections without the need for third-party software. To enable SSH on Windows 10, follow these steps:
- Open the Start menu and go to Settings > Apps > Optional Features.
- Click on "Add a feature" and search for "OpenSSH Client."
- Select "OpenSSH Client" and click Install.
- Once installed, you can use the SSH client from the Command Prompt or PowerShell.
By enabling SSH on Windows 10, you gain access to a powerful tool for remote access and device management. This built-in functionality simplifies the setup process and eliminates the need for additional software, reducing potential security risks.
Tips for Using SSH on Windows 10
To make the most of SSH on Windows 10, consider the following tips:
- Use PowerShell for advanced scripting and automation.
- Configure SSH settings in the Windows Registry for enhanced control.
- Regularly update your system to ensure compatibility with the latest SSH features.
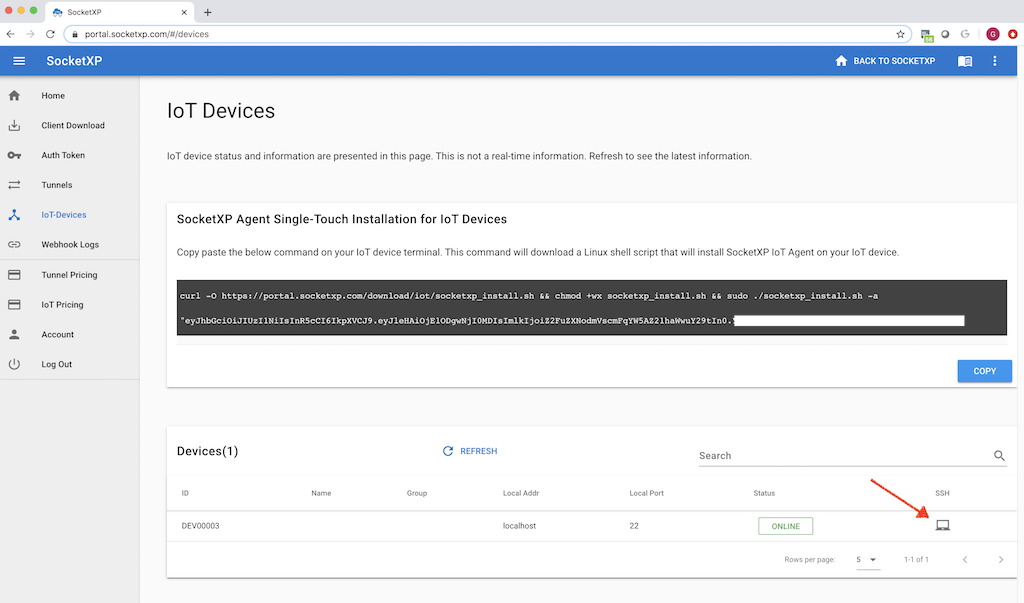
Setting Up IoT Devices for SSH
Before you can connect to an IoT device via SSH, you need to configure the device to accept SSH connections. This typically involves installing an SSH server on the device and configuring network settings to allow remote access. The exact steps may vary depending on the type of IoT device and its operating system.
For devices running Linux-based operating systems, such as Raspberry Pi or other single-board computers, you can enable SSH by following these steps:
- Access the device's terminal or command-line interface.
- Install an SSH server using a package manager like apt or yum.
- Start the SSH service and configure it to start automatically on boot.
- Set up a static IP address to ensure consistent connectivity.
Securing IoT Devices for Remote Access
When setting up IoT devices for SSH, it's crucial to implement security measures to protect against unauthorized access. Some best practices include:
- Changing default passwords and usernames.
- Enabling firewall rules to restrict access to specific IP addresses.
- Disabling password authentication and using public key authentication instead.
Connecting to IoT Devices via SSH
Once SSH is enabled on both your Windows 10 machine and the IoT device, you can establish a connection using the SSH client. Open the Command Prompt or PowerShell and enter the following command:
ssh username@device_ip_address
Replace "username" with the username for the IoT device and "device_ip_address" with the IP address of the device. If public key authentication is enabled, you may need to specify the path to your private key using the "-i" option:
ssh -i /path/to/private/key username@device_ip_address
Common Connection Issues and Solutions
While connecting to IoT devices via SSH is generally straightforward, you may encounter issues such as connection timeouts or authentication failures. Here are some common problems and their solutions:
- Connection timeout: Ensure that the device is reachable over the network and that the SSH service is running.
- Authentication failure: Verify that the username and password are correct and that public key authentication is properly configured.
- Permission denied: Check file permissions for the private key and ensure that the SSH configuration file is correctly set up.
Security Best Practices for SSH
Security is paramount when it comes to remote access, especially for IoT devices that may handle sensitive data. To ensure the highest level of security, follow these best practices:
- Use strong, unique passwords or public key authentication.
- Limit access to specific IP addresses using firewall rules.
- Regularly update the SSH server and client software to patch vulnerabilities.
- Monitor logs for suspicious activity and take appropriate action if unauthorized access attempts are detected.
By implementing these security measures, you can significantly reduce the risk of unauthorized access and data breaches.
Advanced Security Features of SSH
SSH offers several advanced security features that can further enhance the security of your remote connections:
- Two-factor authentication for added security.
- Chroot jails to restrict access to specific directories.
- Port forwarding for secure communication between devices.
Troubleshooting Common Issues
Even with proper configuration, you may encounter issues when setting up SSH for remote access to IoT devices. Here are some common problems and their solutions:
- Device not reachable: Verify the network configuration and ensure that the device's IP address is correct.
- SSH service not running: Check the status of the SSH service and restart it if necessary.
- Authentication issues: Confirm that the public key is correctly installed on the device and that the private key is accessible on the client machine.
For more complex issues, consult the device's documentation or seek assistance from online forums and communities.
Resources for Troubleshooting
Several resources are available to help you troubleshoot SSH-related issues:
- Official SSH documentation and user guides.
- Online forums and communities, such as Stack Overflow and Reddit.
- Vendor-specific support channels for IoT devices.
Benefits of Using SSH for IoT Remote Access
Using SSH for remote access to IoT devices offers numerous benefits, including:
- Enhanced security through encryption and authentication.
- Reliability and stability for mission-critical applications.
- Compatibility with a wide range of devices and platforms.
- Cost-effectiveness by eliminating the need for third-party tools.
By leveraging SSH for IoT remote access, you can achieve a secure, efficient, and scalable solution that meets the demands of modern connected environments.
Real-World Applications of SSH in IoT
SSH is widely used in various industries for IoT remote access, including:
- Smart home automation for managing connected devices.
- Industrial IoT for monitoring and controlling machinery.
- Healthcare IoT for secure data transmission and device management.
Alternatives to SSH for Remote Access
While SSH is a powerful tool for remote access, there are alternative methods that may be suitable for certain use cases:
- VPN: Provides a secure tunnel for accessing remote networks but requires additional setup and maintenance.
- Web-based interfaces: Offer user-friendly access but may lack the security features of SSH.
- Third-party remote access tools: Provide additional features but introduce potential security risks.
When choosing a remote access method, consider factors such as security requirements, ease of use, and compatibility with your devices and infrastructure.
Conclusion and Next Steps
In conclusion, SSH is a secure and reliable solution for remote access to IoT devices on Windows 10 without the need for third-party tools. By following the steps outlined in this article, you can establish secure connections, implement best practices for security, and troubleshoot common issues effectively.
We encourage you to try out the techniques discussed in this guide and share your experiences in the comments section below. For further reading, explore our other articles on IoT security, networking, and device management. Together, let's build a safer and more connected world!
Call to Action: Leave a comment or question below, and don't forget to share this article with others who may find it useful. Your feedback helps us improve and create more valuable content for you!