In today's digital era, the demand for secure remote access solutions has skyrocketed. RemoteIoT SSH free download offers users a reliable and efficient way to access their devices remotely while ensuring robust security. Whether you're a tech enthusiast, a business owner, or an IT professional, understanding how RemoteIoT SSH works and how to download it can significantly enhance your remote connectivity experience.
RemoteIoT SSH is a powerful tool designed to provide secure shell access to remote devices. It enables users to manage and monitor their systems from anywhere in the world with ease. With its intuitive interface and advanced encryption protocols, RemoteIoT SSH ensures that your data remains protected while you work remotely.
This comprehensive guide will walk you through everything you need to know about RemoteIoT SSH, including its features, benefits, and how to download it for free. By the end of this article, you'll have a clear understanding of why RemoteIoT SSH is an essential tool for anyone looking to enhance their remote access capabilities.
Read also:Jon Scheyer The Inspirational Journey Of A Basketball Legend
Table of Contents
- Introduction to RemoteIoT SSH
- Key Features of RemoteIoT SSH
- Benefits of Using RemoteIoT SSH
- Security Aspects of RemoteIoT SSH
- How to Download RemoteIoT SSH Free
- Installation Process
- Using RemoteIoT SSH Effectively
- Comparison with Other Tools
- Common Issues and Troubleshooting
- Conclusion and Next Steps
Introduction to RemoteIoT SSH
RemoteIoT SSH is a cutting-edge software solution designed to facilitate secure remote access to IoT devices and systems. It leverages the Secure Shell (SSH) protocol, which is widely regarded as one of the most secure methods for remote communication. The tool is particularly useful for businesses and individuals who need to manage their devices and networks remotely without compromising on security.
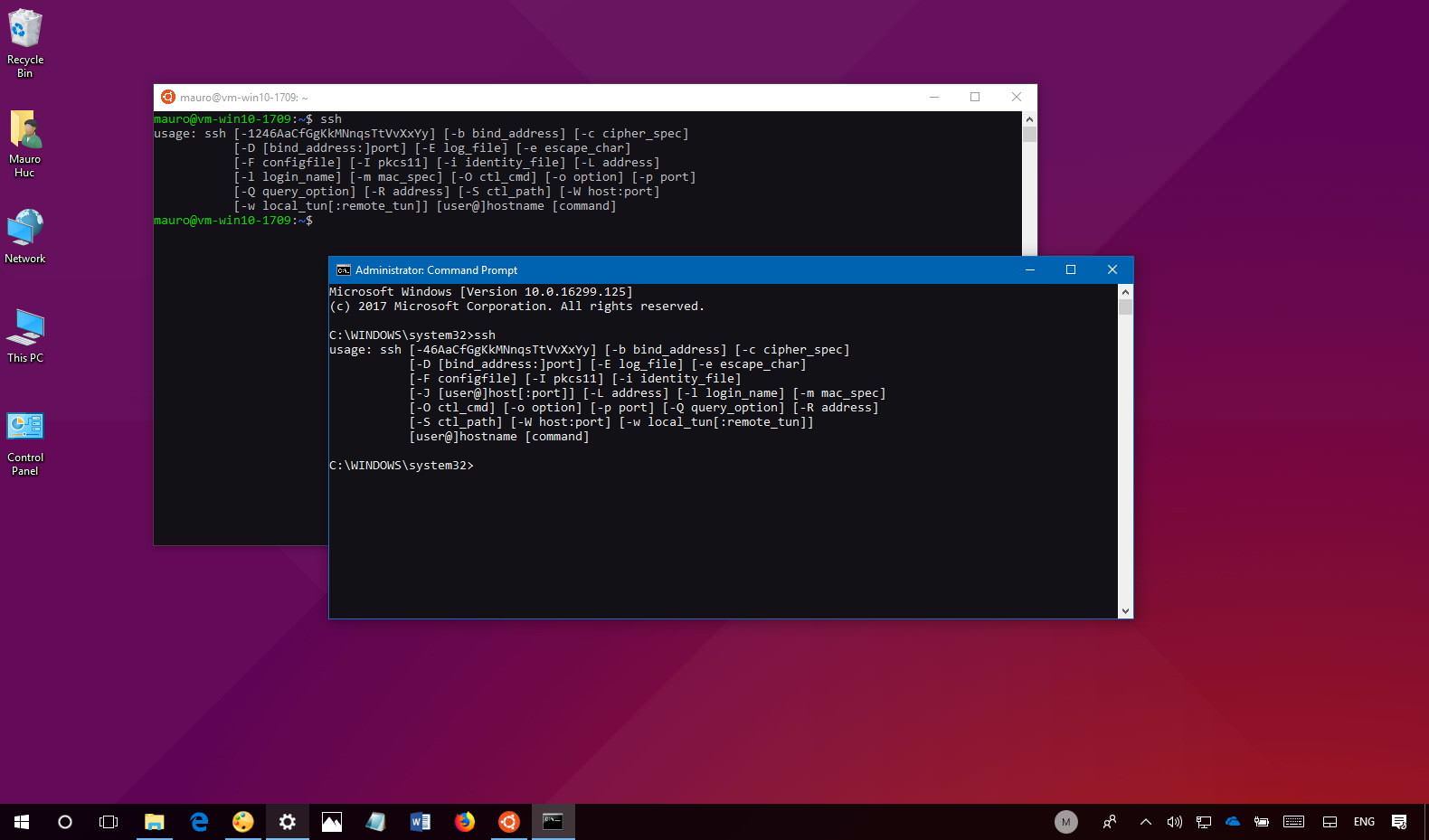
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol that provides secure data communication, remote command execution, and file transfer between computers. It encrypts all data transmitted between the client and server, making it virtually impossible for unauthorized users to intercept or decipher the information.
Why Choose RemoteIoT SSH?
RemoteIoT SSH stands out from other remote access tools due to its robust security features, ease of use, and compatibility with a wide range of devices. Whether you're managing a small home network or a large enterprise system, RemoteIoT SSH offers the flexibility and reliability you need to stay connected and productive.
Key Features of RemoteIoT SSH
RemoteIoT SSH is packed with features that make it an ideal choice for remote access. Below are some of its standout features:
Read also:Utah Valley Basketball Exploring The Thrilling World Of College And Local Basketball
- Advanced Encryption: Utilizes strong encryption algorithms to protect your data from unauthorized access.
- Cross-Platform Compatibility: Works seamlessly on Windows, macOS, Linux, and various IoT devices.
- Easy Configuration: Simple setup process ensures you can start using the tool in no time.
- Command-Line Interface: Offers a powerful CLI for advanced users who prefer more control over their systems.
- File Transfer: Securely transfer files between your local and remote systems with ease.
Benefits of Using RemoteIoT SSH
Adopting RemoteIoT SSH for your remote access needs comes with numerous advantages. Here are some of the key benefits:
Enhanced Security
With its advanced encryption and authentication mechanisms, RemoteIoT SSH ensures that your data remains secure during transmission. This is particularly important for businesses handling sensitive information.
Cost-Effectiveness
RemoteIoT SSH offers a free download option, making it an affordable solution for individuals and small businesses. This eliminates the need for costly proprietary software.
Improved Productivity
By allowing you to access and manage your systems remotely, RemoteIoT SSH helps you stay productive regardless of your location. You can troubleshoot issues, update software, and perform routine maintenance tasks without being physically present.
Security Aspects of RemoteIoT SSH
Security is at the core of RemoteIoT SSH's design. Here's how the tool ensures your data remains protected:
- Encryption Protocols: Uses industry-standard encryption protocols such as AES-256 and RSA to safeguard your data.
- Authentication Mechanisms: Supports multiple authentication methods, including password-based and public key authentication.
- Firewall Integration: Can be easily integrated with firewalls to enhance network security.
Data Privacy
RemoteIoT SSH prioritizes user privacy by ensuring that all data transmitted through its network is encrypted and cannot be accessed by unauthorized parties. This makes it an ideal choice for businesses and individuals who value their privacy.
How to Download RemoteIoT SSH Free
Downloading RemoteIoT SSH is a straightforward process. Follow these steps to get started:
- Visit the official RemoteIoT SSH website.
- Navigate to the "Downloads" section.
- Select the version compatible with your operating system.
- Click on the "Free Download" button to start the download process.
Things to Keep in Mind
When downloading RemoteIoT SSH, ensure that you are downloading it from a legitimate source to avoid potential security risks. Always verify the authenticity of the download link before proceeding.
Installation Process
Once you've downloaded RemoteIoT SSH, the next step is to install it on your system. Here's a step-by-step guide to help you through the process:
- Locate the downloaded installation file on your computer.
- Run the installation file and follow the on-screen instructions.
- Choose the installation directory and customize settings as needed.
- Complete the installation process and launch the application.
Post-Installation Tips
After installation, it's essential to configure the tool properly to ensure optimal performance. This includes setting up authentication methods, configuring firewall rules, and testing the connection to your remote devices.
Using RemoteIoT SSH Effectively
To make the most of RemoteIoT SSH, here are some tips and best practices:
- Regular Updates: Keep the tool updated to benefit from the latest features and security patches.
- Secure Passwords: Use strong, unique passwords for authentication to prevent unauthorized access.
- Backup Configurations: Regularly back up your configuration files to avoid data loss in case of system failure.
Advanced Usage
For advanced users, RemoteIoT SSH offers a range of customization options, including scripting and automation capabilities. These features allow you to automate routine tasks and streamline your workflow.
Comparison with Other Tools
While there are several remote access tools available, RemoteIoT SSH stands out due to its superior security features and ease of use. Below is a comparison with some popular alternatives:
| Feature | RemoteIoT SSH | Tool A | Tool B |
|---|---|---|---|
| Security | High | Medium | Low |
| Cost | Free | Paid | Paid |
| Compatibility | Wide | Limited | Limited |
Common Issues and Troubleshooting
Like any software, RemoteIoT SSH may encounter issues from time to time. Here are some common problems and their solutions:
- Connection Issues: Ensure that your firewall settings allow SSH traffic and that the correct port is open.
- Authentication Failures: Double-check your credentials and ensure that the authentication method is correctly configured.
- Performance Problems: Optimize your network settings and update the tool to the latest version for improved performance.
Conclusion and Next Steps
In conclusion, RemoteIoT SSH offers a secure, reliable, and cost-effective solution for remote access. Its advanced security features, ease of use, and compatibility with a wide range of devices make it an excellent choice for anyone looking to enhance their remote connectivity experience.
We encourage you to download RemoteIoT SSH and explore its capabilities for yourself. Feel free to leave a comment below if you have any questions or feedback. Additionally, don't forget to share this article with your network and explore other informative content on our website.
References: