In today's digital age, remote IoT platform SSH download has become an essential tool for managing and securing devices from anywhere in the world. As businesses increasingly rely on IoT technology, the need for secure and efficient remote access solutions grows stronger. This comprehensive guide will delve into everything you need to know about downloading and implementing SSH on the RemoteIoT platform.
Whether you're a seasoned IT professional or a beginner exploring the world of IoT, this article will provide you with valuable insights. We will cover essential topics such as the benefits of using SSH, step-by-step guides, troubleshooting tips, and much more. By the end of this article, you'll be equipped with the knowledge to confidently download and configure SSH on your RemoteIoT platform.
Our goal is to ensure you have a seamless experience when setting up secure connections for your IoT devices. Let's dive in and explore the world of remote IoT platform SSH download together!
Read also:Cavaliers Vs Kings A Deep Dive Into The Rivalry And Matchups
Table of Contents
- Introduction to RemoteIoT Platform
- Benefits of Using SSH for RemoteIoT
- How to Download SSH for RemoteIoT
- Installation Guide for SSH on RemoteIoT
- Configuring SSH for Secure Connections
- Common Issues and Troubleshooting Tips
- Security Best Practices for RemoteIoT SSH
- Performance Optimization Techniques
- Comparison with Other Remote Access Solutions
- Future Trends in RemoteIoT and SSH
- Conclusion
Introduction to RemoteIoT Platform
The RemoteIoT platform is a cutting-edge solution designed to facilitate remote management and monitoring of IoT devices. It enables users to control and interact with their devices from anywhere in the world, providing unparalleled convenience and flexibility. This platform leverages advanced technologies to ensure secure and efficient communication between devices and users.
What Makes RemoteIoT Unique?
- Scalable architecture for managing multiple devices.
- Advanced encryption protocols for data security.
- User-friendly interface for easy navigation.
- Real-time monitoring and analytics capabilities.
By integrating SSH into the RemoteIoT platform, users can enhance their security measures and ensure that all communication remains protected from unauthorized access. This combination makes it an ideal choice for businesses and individuals looking to safeguard their IoT ecosystems.
Benefits of Using SSH for RemoteIoT
Secure Shell (SSH) is a network protocol that provides secure communication between devices over an unsecured network. When used with the RemoteIoT platform, SSH offers several advantages:
- Data Encryption: SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains confidential.
- Authentication: It supports various authentication methods, such as passwords and public key authentication, to verify user identities.
- Remote Command Execution: Users can execute commands on remote devices securely, streamlining device management processes.
- File Transfer: SSH allows secure file transfers through protocols like SFTP, making it easier to manage files on remote servers.
These benefits make SSH an indispensable tool for anyone using the RemoteIoT platform to manage IoT devices remotely.
How to Download SSH for RemoteIoT
Downloading SSH for the RemoteIoT platform involves a few straightforward steps. First, ensure that your system meets the necessary requirements:
System Requirements
- Operating System: Windows, macOS, or Linux
- Internet Connection: Stable broadband connection
- Storage: At least 50 MB of free disk space
Once you have verified the system requirements, follow these steps to download SSH:
Read also:Rodney Peete The Remarkable Journey Of A Nfl Quarterback
- Visit the official RemoteIoT website or trusted repositories.
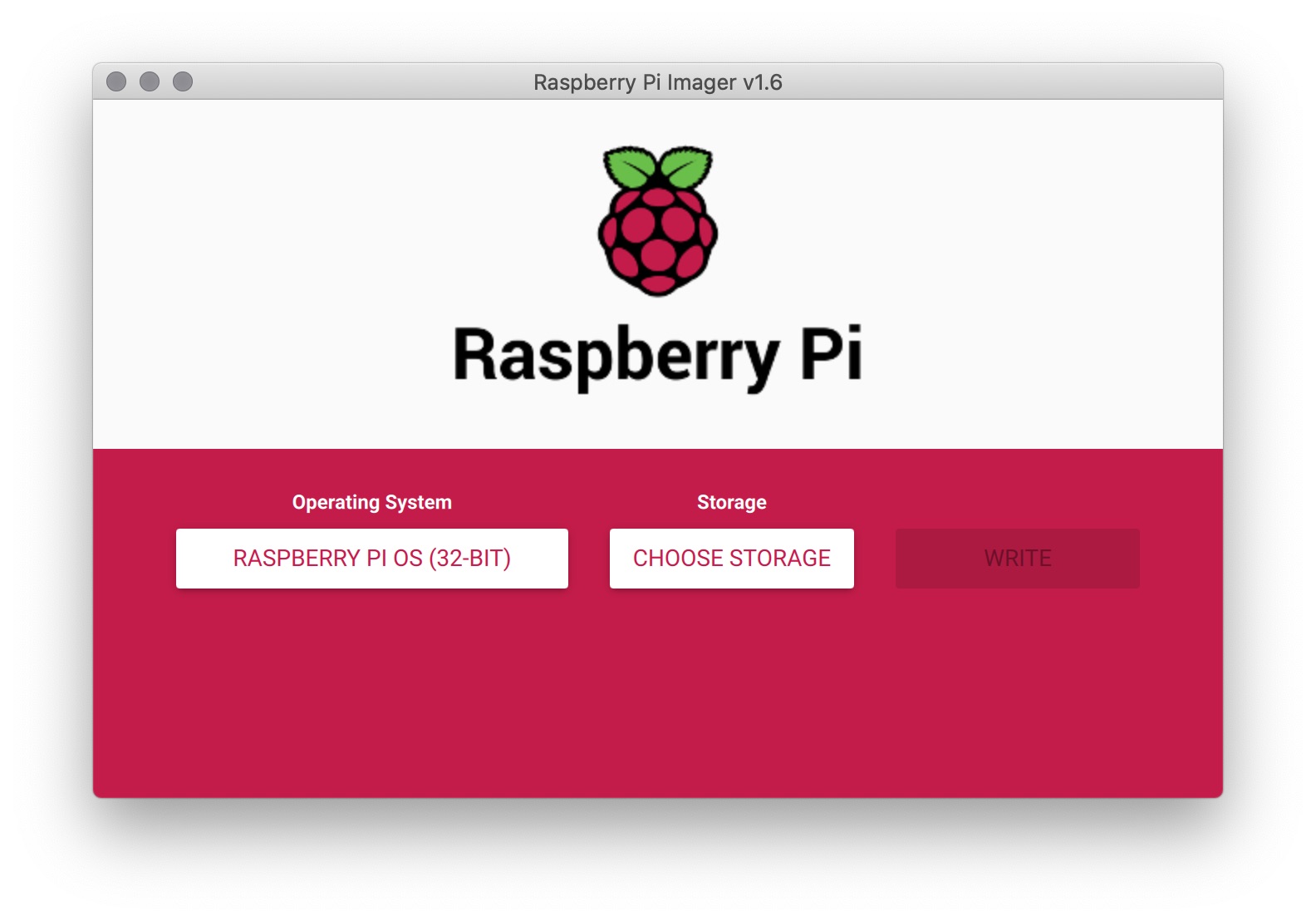
- Locate the SSH download section and select the appropriate version for your operating system.
- Download the installation package and save it to your desired location.
By following these steps, you'll have the necessary tools to set up SSH on your RemoteIoT platform.
Installation Guide for SSH on RemoteIoT
Installing SSH on the RemoteIoT platform is a simple process that can be completed in a few steps. Below is a detailed guide to help you through the installation:
Step 1: Prepare Your Environment
Before beginning the installation, ensure that your RemoteIoT platform is properly configured and running. Verify that all necessary ports are open and accessible.
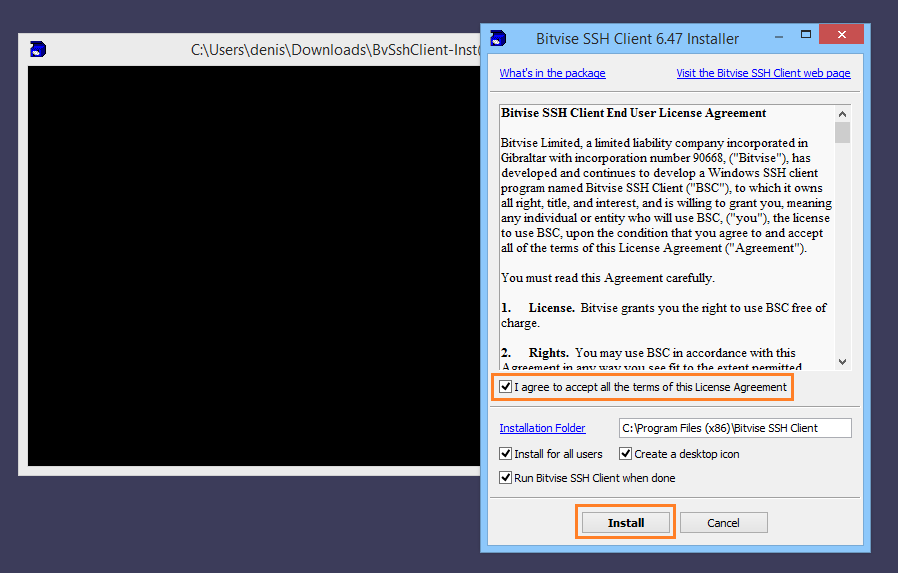
Step 2: Execute the Installation
Run the downloaded SSH installation package and follow the on-screen instructions. The installer will guide you through the process, allowing you to customize settings as needed.
Step 3: Verify the Installation
After completing the installation, test the SSH connection to ensure everything is functioning correctly. Use a terminal or command prompt to connect to your RemoteIoT server and verify the connection.
By following this guide, you'll have SSH up and running on your RemoteIoT platform in no time.
Configuring SSH for Secure Connections
Configuring SSH for secure connections involves modifying the SSH configuration file and implementing best practices to enhance security. Below are some key steps to consider:
Editing the SSH Configuration File
Locate the SSH configuration file (usually found at /etc/ssh/sshd_config) and open it using a text editor. Make the following changes:
- Disable password authentication and use public key authentication instead.
- Change the default SSH port to a non-standard port to reduce the risk of automated attacks.
- Limit access to specific users or IP addresses.
After making these changes, restart the SSH service to apply the new settings.
Common Issues and Troubleshooting Tips
While setting up SSH on the RemoteIoT platform, you may encounter some common issues. Below are a few troubleshooting tips to help you resolve these problems:
- Connection Refused: Ensure that the SSH service is running and the required ports are open.
- Authentication Failed: Double-check your public key and ensure it is correctly added to the authorized_keys file.
- Timeout Errors: Verify your network connection and ensure there are no firewalls blocking the SSH connection.
By addressing these issues promptly, you can maintain a stable and secure SSH connection for your RemoteIoT platform.
Security Best Practices for RemoteIoT SSH
Implementing security best practices is crucial for protecting your RemoteIoT platform and its connected devices. Consider the following tips:
- Regularly update your SSH software to patch any security vulnerabilities.
- Use strong, unique passwords and enable two-factor authentication (2FA) whenever possible.
- Monitor access logs for suspicious activities and take immediate action if any unauthorized access is detected.
These practices will help safeguard your RemoteIoT platform and ensure that your IoT devices remain secure.
Performance Optimization Techniques
Optimizing the performance of your RemoteIoT platform with SSH involves fine-tuning various settings to improve efficiency. Here are some techniques to consider:
- Enable compression to reduce data transfer times.
- Limit the number of concurrent connections to prevent server overload.
- Use caching mechanisms to store frequently accessed data.
By implementing these techniques, you can enhance the performance of your RemoteIoT platform and ensure seamless remote access.
Comparison with Other Remote Access Solutions
While SSH is a powerful tool for remote access, it's important to compare it with other solutions to determine the best fit for your needs. Below is a comparison of SSH with popular alternatives:
SSH vs. RDP
- SSH: Best suited for command-line access and secure file transfers.
- RDP: Ideal for graphical user interface (GUI) access and remote desktop sessions.
SSH vs. VNC
- SSH: Provides robust security features and is ideal for managing servers and devices.
- VNC: Offers screen-sharing capabilities and is better suited for remote desktop control.
Choosing the right solution depends on your specific requirements and the nature of your IoT deployment.
Future Trends in RemoteIoT and SSH
As technology continues to evolve, the future of RemoteIoT and SSH looks promising. Some emerging trends include:
- Increased adoption of quantum-resistant encryption algorithms to protect against future threats.
- Integration of artificial intelligence (AI) for automated threat detection and response.
- Development of more user-friendly interfaces to simplify the management of IoT devices.
By staying informed about these trends, you can prepare for the future and ensure that your RemoteIoT platform remains up-to-date and secure.
Conclusion
In conclusion, downloading and configuring SSH for your RemoteIoT platform is a vital step in ensuring secure and efficient remote access to your IoT devices. By following the guidelines outlined in this article, you can confidently set up SSH and take advantage of its numerous benefits.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT and cybersecurity. Together, let's build a safer and more connected world!