RemoteIoT web SSH download has become increasingly important in the realm of remote system management and IoT deployment. As businesses and individuals seek to streamline their operations and enhance security, understanding how to effectively utilize RemoteIoT web SSH download is crucial. Whether you're a network administrator or a tech enthusiast, this guide will provide you with the insights and tools you need to excel in this area.
In today's fast-paced digital landscape, the ability to manage devices remotely is no longer a luxury but a necessity. RemoteIoT web SSH download plays a pivotal role in enabling secure access to servers and IoT devices from anywhere in the world. This capability not only improves efficiency but also ensures that data remains protected against unauthorized access.
This article delves into the intricacies of RemoteIoT web SSH download, offering detailed explanations, practical tips, and expert advice. By the end of this guide, you'll have a comprehensive understanding of how to leverage this technology effectively, ensuring your systems are both secure and efficient.
Read also:Mount Rushmore Presidents The Iconic Monument And The Men Who Shaped A Nation
Table of Contents
- Introduction to RemoteIoT Web SSH Download
- Benefits of RemoteIoT Web SSH Download
- Setting Up RemoteIoT Web SSH
- Security Considerations for RemoteIoT Web SSH
- Tools and Software for RemoteIoT Web SSH Download
- Troubleshooting Common Issues
- Optimizing RemoteIoT Web SSH Performance
- Applications of RemoteIoT Web SSH
- Best Practices for RemoteIoT Web SSH Download
- Future Trends in RemoteIoT Web SSH
Introduction to RemoteIoT Web SSH Download
Understanding RemoteIoT Web SSH
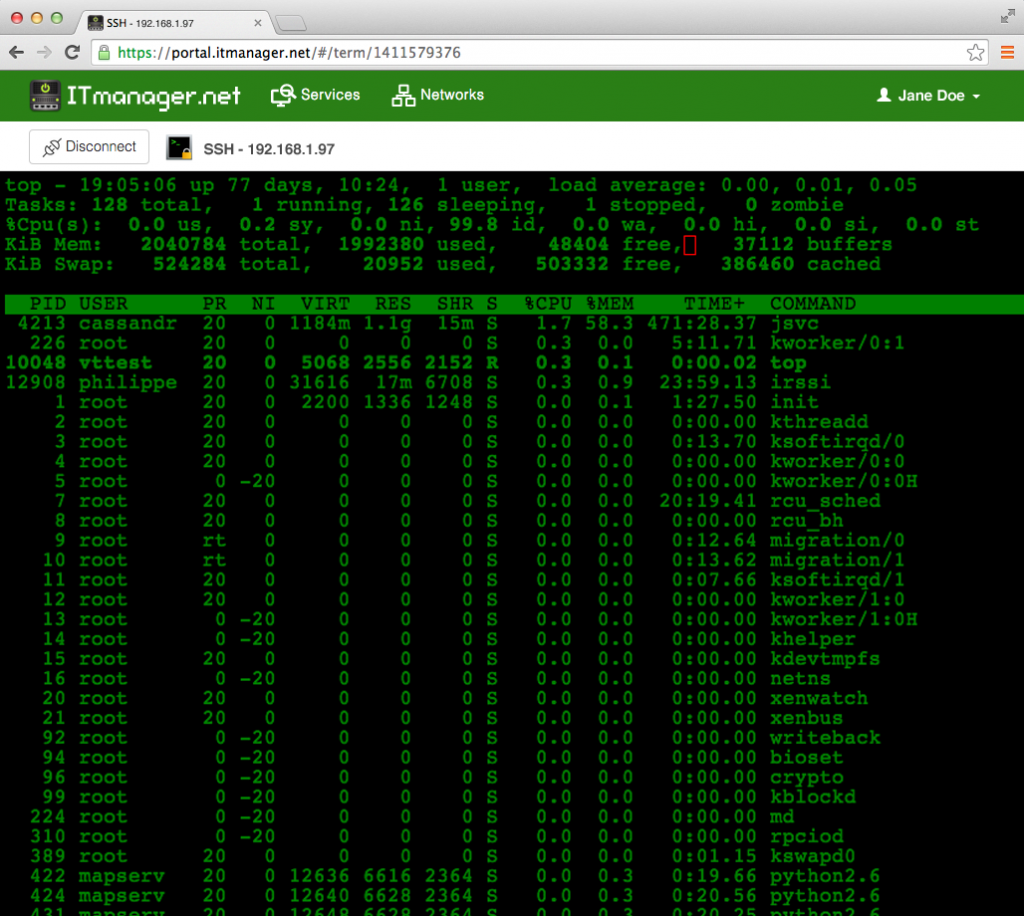
RemoteIoT web SSH download refers to the process of accessing and managing IoT devices or servers remotely using Secure Shell (SSH) protocols via a web interface. This method allows users to securely connect to remote systems without the need for physical access, making it an invaluable tool for modern IT professionals.
SSH provides a secure channel over an unsecured network, ensuring that data transmitted between devices remains encrypted and protected. With RemoteIoT web SSH download, administrators can perform tasks such as file transfers, configuration updates, and system monitoring with ease.
Understanding the basics of RemoteIoT web SSH is essential for anyone looking to enhance their remote management capabilities. From setting up the initial connection to troubleshooting common issues, this section will guide you through the foundational aspects of RemoteIoT web SSH download.
Benefits of RemoteIoT Web SSH Download
Enhanced Security
One of the primary benefits of RemoteIoT web SSH download is the enhanced security it offers. By utilizing SSH protocols, users can ensure that all data transmitted between devices remains encrypted and protected from unauthorized access.
SSH employs robust encryption algorithms, such as AES and RSA, to safeguard sensitive information. This level of security is particularly important in the IoT landscape, where devices often handle critical data that must remain confidential.
- Encrypted data transmission
- Authentication mechanisms
- Protection against man-in-the-middle attacks
Setting Up RemoteIoT Web SSH
Step-by-Step Guide
Setting up RemoteIoT web SSH download involves several key steps. Below is a detailed guide to help you configure your system for secure remote access:
Read also:Eliminatorias Conmebol The Ultimate Guide To South Americas Road To The World Cup
- Install an SSH server on your target device.
- Configure firewall settings to allow SSH traffic.
- Set up user authentication using SSH keys or passwords.
- Test the connection using an SSH client.
By following these steps, you can establish a secure and reliable connection to your remote devices. Proper configuration is essential to ensure that your system remains protected against potential threats.
Security Considerations for RemoteIoT Web SSH
Best Security Practices
While RemoteIoT web SSH download offers robust security features, it is important to implement best practices to further enhance protection. Below are some key considerations:
- Use strong, unique passwords or SSH keys for authentication.
- Limit access to authorized users only.
- Regularly update SSH software to patch vulnerabilities.
- Monitor system logs for suspicious activity.
By adhering to these security practices, you can minimize the risk of unauthorized access and ensure the integrity of your remote systems.
Tools and Software for RemoteIoT Web SSH Download
Popular SSH Clients
Several tools and software are available to facilitate RemoteIoT web SSH download. Below are some of the most popular options:
- Putty: A widely used SSH client for Windows users.
- OpenSSH: A free and open-source SSH client available on Linux and macOS.
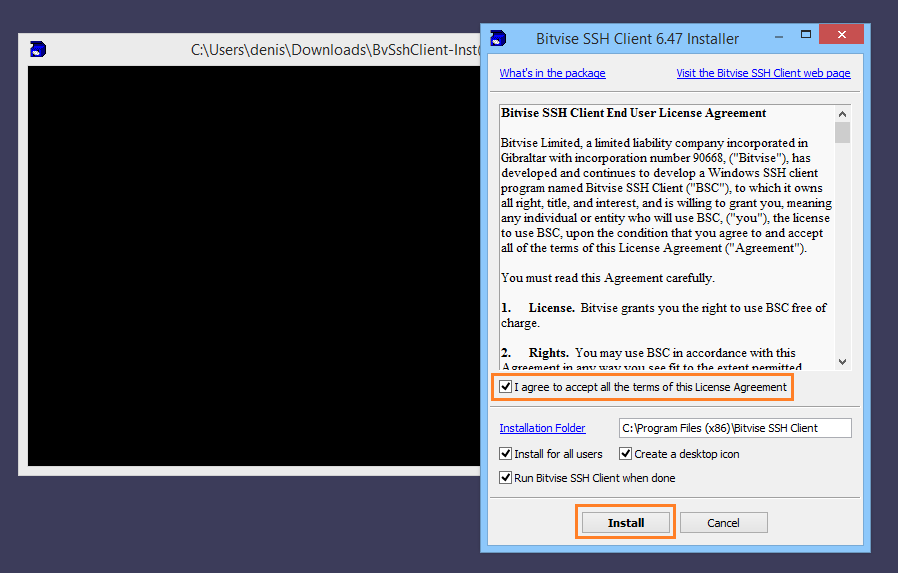
- Bitvise: A feature-rich SSH client with support for SFTP and terminal sessions.
Choosing the right tool depends on your specific needs and preferences. Each option offers unique features and capabilities, so it's important to evaluate them carefully before making a decision.
Troubleshooting Common Issues
Solving Connection Problems
Despite its reliability, RemoteIoT web SSH download can sometimes encounter issues. Below are some common problems and their solutions:
- Connection timeouts: Check network settings and ensure that the SSH server is running.
- Authentication failures: Verify that the correct credentials are being used and that SSH keys are properly configured.
- Firewall blocks: Adjust firewall rules to allow SSH traffic on the appropriate port (default is 22).
By addressing these issues promptly, you can maintain a stable and secure connection to your remote systems.
Optimizing RemoteIoT Web SSH Performance
Tips for Faster Connections
To optimize the performance of RemoteIoT web SSH download, consider the following tips:
- Use compression to reduce data transfer times.
- Implement keepalive settings to prevent idle connections from dropping.
- Choose the most efficient encryption algorithms for your use case.
By fine-tuning these settings, you can achieve faster and more reliable connections, improving overall efficiency and productivity.
Applications of RemoteIoT Web SSH
Real-World Use Cases
RemoteIoT web SSH download has a wide range of applications across various industries. Below are some examples:
- Network administration: Manage servers and network devices remotely.
- IoT deployment: Monitor and control IoT devices in real-time.
- Software development: Deploy and debug applications on remote servers.
These applications demonstrate the versatility and importance of RemoteIoT web SSH download in modern technology environments.
Best Practices for RemoteIoT Web SSH Download
Maximizing Efficiency and Security
To maximize the efficiency and security of RemoteIoT web SSH download, follow these best practices:
- Regularly update SSH software and firmware.
- Use multi-factor authentication for added security.
- Document and share configuration settings with your team.
By adhering to these practices, you can ensure that your RemoteIoT web SSH setup remains secure and efficient, meeting the demands of modern remote management.
Future Trends in RemoteIoT Web SSH
Emerging Technologies
As technology continues to evolve, several trends are shaping the future of RemoteIoT web SSH download:
- Quantum encryption: Enhanced security measures to protect against quantum computing threats.
- AI-driven monitoring: Intelligent systems to detect and respond to security threats in real-time.
- Cloud-based solutions: Increased adoption of cloud-based SSH services for greater scalability.
Staying informed about these trends will help you prepare for the future of remote system management and IoT deployment.
Conclusion
In conclusion, RemoteIoT web SSH download is a powerful tool for managing remote systems and IoT devices securely and efficiently. By understanding its benefits, setting it up correctly, and implementing best practices, you can harness its full potential to enhance your operations.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into technology and security. Together, let's continue to advance the field of remote system management and IoT deployment.