As the Internet of Things (IoT) continues to expand, remotely accessing IoT devices has become a critical task for modern developers and system administrators. Whether it's for monitoring, maintenance, or troubleshooting, the ability to securely connect to IoT devices from anywhere is essential. In this article, we will explore the best methods to remotely access IoT devices using SSH, web-based interfaces, and AWS services.
With billions of IoT devices connected globally, ensuring secure and efficient remote access is paramount. The increasing reliance on cloud platforms like AWS has further simplified the process, allowing users to manage IoT devices from anywhere in the world. This article will provide you with a comprehensive guide to setting up and managing remote access for IoT devices using SSH, web-based tools, and AWS services.
Whether you're a beginner or an experienced professional, this guide will equip you with the knowledge and tools to implement secure remote access solutions for your IoT devices. Let's dive into the details!
Read also:Fmcs The Ultimate Guide To Understanding Its Role In Modern Industry
Table of Contents
- Introduction to Remote Access for IoT Devices
- Understanding SSH for Remote Access
- Web-Based Remote Access Solutions
- AWS Services for IoT Remote Access
- Ensuring Security in Remote Access
- Best Tools for IoT Remote Access
- Setting Up Remote Access for IoT Devices
- Optimizing Remote Access Performance
- Troubleshooting Common Issues
- Conclusion
Introduction to Remote Access for IoT Devices
Remote access to IoT devices is a fundamental requirement in today's connected world. IoT devices are deployed in various environments, from industrial settings to smart homes, and the ability to manage them remotely is crucial for efficiency and scalability.
The best remotely access IoT devices methods involve using secure protocols and tools that ensure data integrity and device security. Among these methods, SSH, web-based interfaces, and AWS services stand out as the most reliable options.
In this section, we will explore why remote access is important, the challenges associated with it, and how modern solutions address these challenges.
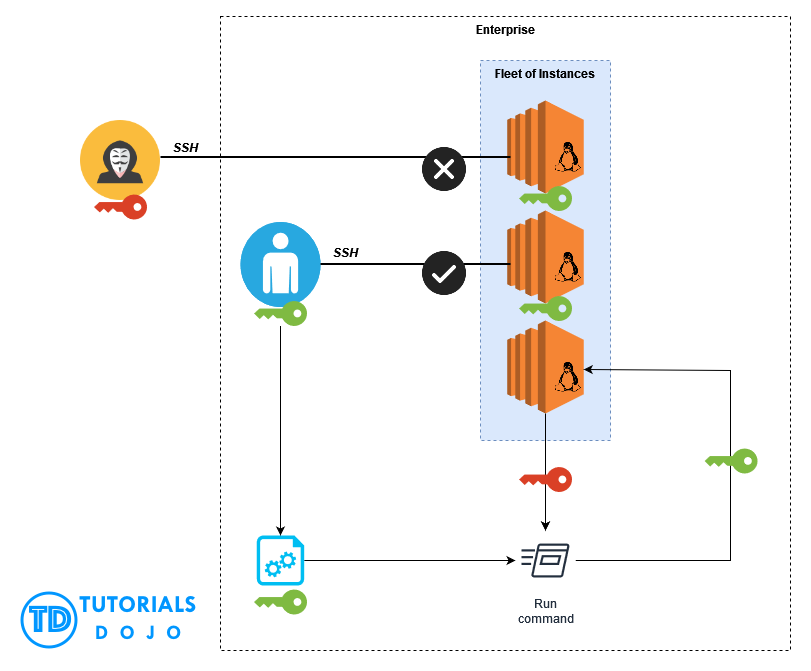
Understanding SSH for Remote Access
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol used for secure communication between devices over an unsecured network. It is widely used for remote access to IoT devices due to its robust security features.
SSH provides encrypted communication, ensuring that sensitive data is protected from unauthorized access. It also supports authentication mechanisms, such as passwords and public key infrastructure (PKI), to verify the identity of users and devices.
Advantages of Using SSH
- Highly secure and encrypted communication
- Supports multiple authentication methods
- Compatible with a wide range of devices and operating systems
- Easy to configure and manage
Web-Based Remote Access Solutions
Why Use Web-Based Access?
Web-based remote access solutions offer a convenient way to manage IoT devices without the need for specialized software. These solutions typically provide a browser-based interface that allows users to interact with devices directly from a web page.
Read also:E Zpass Scam What You Need To Know To Protect Yourself
Some popular web-based solutions include cloud platforms, device management portals, and custom-built web applications. These tools are particularly useful for organizations that require centralized control over multiple IoT devices.
Key Features of Web-Based Solutions
- Easy-to-use graphical user interface (GUI)
- Real-time monitoring and control
- Integration with cloud services
- Scalability and flexibility
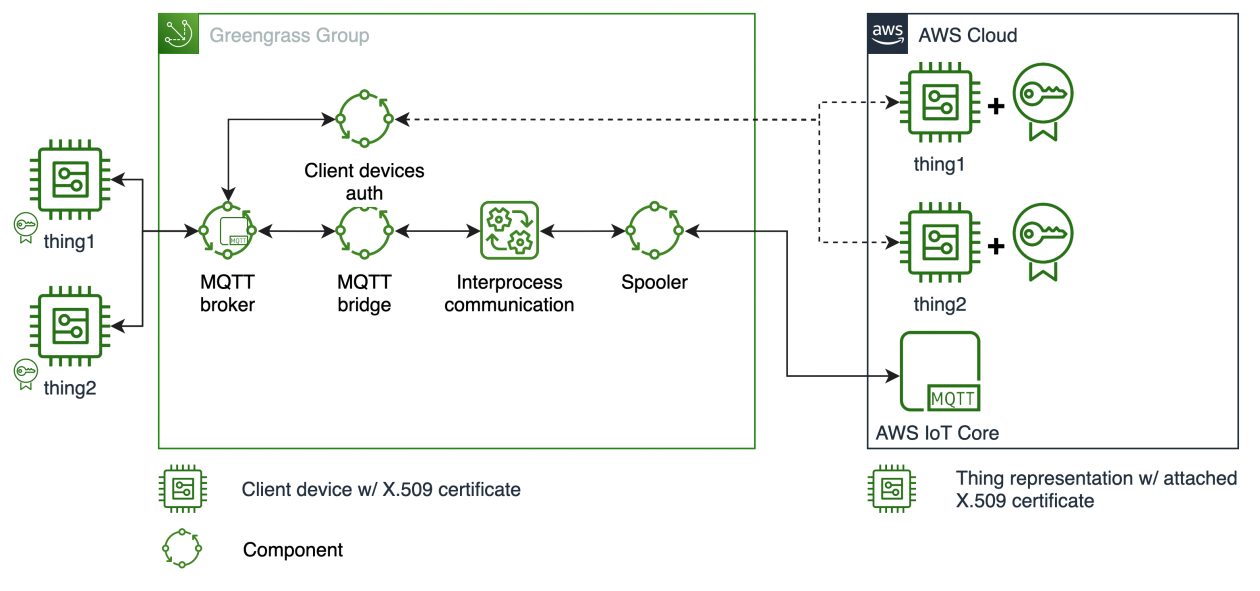
AWS Services for IoT Remote Access
Overview of AWS IoT Core
Amazon Web Services (AWS) offers a suite of tools and services specifically designed for IoT applications. AWS IoT Core is one of the most popular services, providing a managed cloud platform for connecting, monitoring, and managing IoT devices.
AWS IoT Core supports secure communication using MQTT, HTTP, and WebSockets, making it an ideal choice for remote access applications. It also integrates seamlessly with other AWS services, such as AWS Lambda and AWS IoT Device Management.
Benefits of Using AWS for IoT
- Scalable infrastructure for large-scale deployments
- Advanced security features, including device authentication and encryption
- Real-time data processing and analytics
- Global availability and low latency
Ensuring Security in Remote Access
Best Practices for Secure Remote Access
Security is a top priority when remotely accessing IoT devices. To ensure the safety of your devices and data, it is essential to follow best practices for secure remote access. Some of these practices include:
- Using strong passwords and multi-factor authentication (MFA)
- Regularly updating firmware and software
- Implementing network segmentation and firewalls
- Monitoring access logs for suspicious activity
Common Security Threats
Remote access systems are vulnerable to various security threats, including unauthorized access, malware, and data breaches. By implementing robust security measures, you can mitigate these risks and protect your IoT devices.
Stay informed about the latest security trends and vulnerabilities to ensure your remote access setup remains secure.
Best Tools for IoT Remote Access
Top Tools for Managing IoT Devices
Several tools are available for managing IoT devices remotely. Some of the best tools include:
- SSH clients like PuTTY and OpenSSH
- Web-based platforms like Node-RED and ThingsBoard
- Cloud services like AWS IoT Core and Microsoft Azure IoT Hub
Each tool offers unique features and capabilities, so it's important to choose the one that best fits your needs.
Setting Up Remote Access for IoT Devices
Step-by-Step Guide to Setting Up SSH
Setting up SSH for remote access involves several steps, including:
- Installing an SSH server on the IoT device
- Configuring firewall rules to allow SSH traffic
- Generating SSH keys for secure authentication
- Connecting to the device using an SSH client
Follow these steps carefully to ensure a secure and reliable connection.
Configuring Web-Based Access
To set up web-based remote access, you will need to:
- Deploy a web server or use a cloud-based platform
- Create a user-friendly interface for device management
- Implement security measures, such as HTTPS and authentication
- Test the setup to ensure proper functionality
Optimizing Remote Access Performance
Tips for Improving Performance
Optimizing the performance of your remote access setup can enhance the user experience and reduce latency. Some tips for improving performance include:
- Using compression and caching techniques
- Optimizing network configurations
- Minimizing the number of open connections
- Monitoring system resources and adjusting settings as needed
Troubleshooting Common Issues
Identifying and Resolving Problems
Common issues with remote access include connection errors, authentication failures, and slow performance. To troubleshoot these problems, you can:
- Check network settings and connectivity
- Verify authentication credentials and permissions
- Review logs for error messages and diagnostics
- Consult documentation and support resources for additional assistance
Conclusion
In conclusion, the best remotely access IoT devices methods involve a combination of secure protocols, web-based interfaces, and cloud services like AWS. By following the guidelines and best practices outlined in this article, you can ensure a secure and efficient remote access setup for your IoT devices.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more information on IoT and related technologies. Together, let's build a smarter, more connected world!
References: