In today's rapidly evolving technological landscape, remote IoT device SSH has become an essential tool for businesses and individuals alike. As more devices become interconnected, ensuring secure communication between them is paramount. This article delves into the best remote IoT device SSH solutions, offering comprehensive insights for both beginners and experts.
With the proliferation of Internet of Things (IoT) devices, the demand for secure remote access has surged. Remote SSH (Secure Shell) provides a reliable and encrypted method to manage and interact with IoT devices from anywhere in the world. This technology ensures that sensitive data remains protected while enabling seamless remote operations.
Whether you're a tech enthusiast, a network administrator, or a business owner, understanding remote IoT device SSH is crucial for enhancing security and efficiency. This guide will walk you through everything you need to know, from the basics to advanced implementations, ensuring you make informed decisions about your IoT infrastructure.
Read also:Understanding Federal Reserve Interest Rates A Comprehensive Guide
Table of Contents
- Introduction to Remote IoT Device SSH
- Why Is Remote IoT Device SSH Important?
- How Does Remote IoT Device SSH Work?
- Top Remote IoT Device SSH Solutions
- Choosing the Right Remote IoT Device SSH
- Security Best Practices for Remote IoT Device SSH
- Common Challenges and Solutions
- Case Studies of Remote IoT Device SSH
- Future Trends in Remote IoT Device SSH
- Conclusion and Call to Action
Introduction to Remote IoT Device SSH
What Is Remote IoT Device SSH?
Remote IoT device SSH refers to the use of Secure Shell (SSH) protocols to establish secure connections with Internet of Things (IoT) devices remotely. SSH is a network protocol that encrypts data transmitted between devices, ensuring that sensitive information remains protected from unauthorized access.
SSH is widely regarded as one of the most secure methods for remote device management. It supports authentication, encryption, and data integrity, making it ideal for IoT applications where security is paramount.
Benefits of Using Remote IoT Device SSH
The adoption of remote IoT device SSH offers numerous advantages:
- Enhanced security through encryption and authentication
- Seamless remote management of IoT devices
- Reduced operational costs by minimizing on-site interventions
- Improved efficiency in monitoring and troubleshooting
Why Is Remote IoT Device SSH Important?
In the era of smart devices, the importance of remote IoT device SSH cannot be overstated. With billions of IoT devices connected globally, the risk of cyberattacks has increased exponentially. Remote SSH ensures that data transmitted between devices remains secure, reducing the likelihood of unauthorized access and data breaches.
Moreover, remote IoT device SSH enables organizations to manage their IoT infrastructure more effectively. By providing a secure and reliable method for remote access, SSH empowers administrators to monitor, configure, and troubleshoot devices from anywhere in the world.
How Does Remote IoT Device SSH Work?
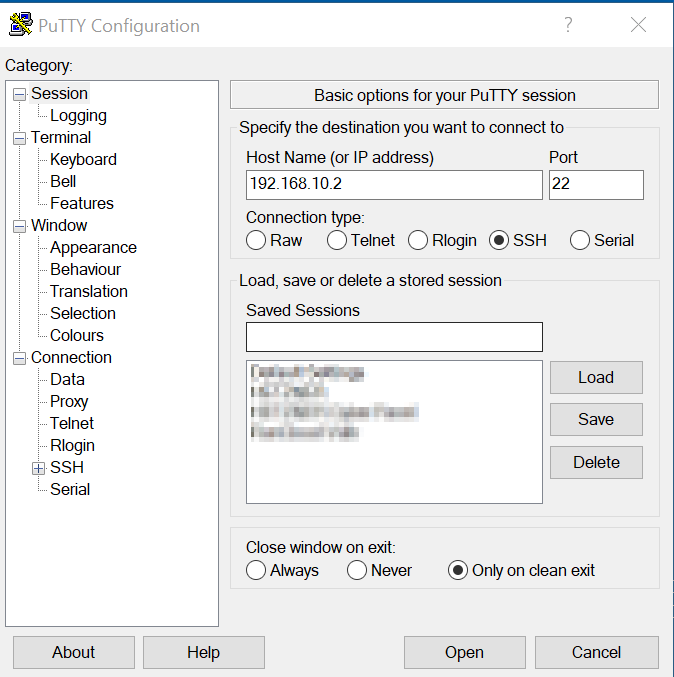
Remote IoT device SSH operates by establishing an encrypted connection between a client and a server. The process involves several key steps:
Read also:India Vs Maldives A Comprehensive Analysis Of Their Relations And Key Comparisons
- Authentication: The client authenticates with the server using credentials such as passwords or public key authentication.
- Encryption: Once authenticated, all data transmitted between the client and server is encrypted to prevent eavesdropping.
- Data Integrity: SSH ensures that data remains unaltered during transmission by implementing cryptographic techniques.
This robust framework makes SSH an ideal choice for securing IoT device communications.
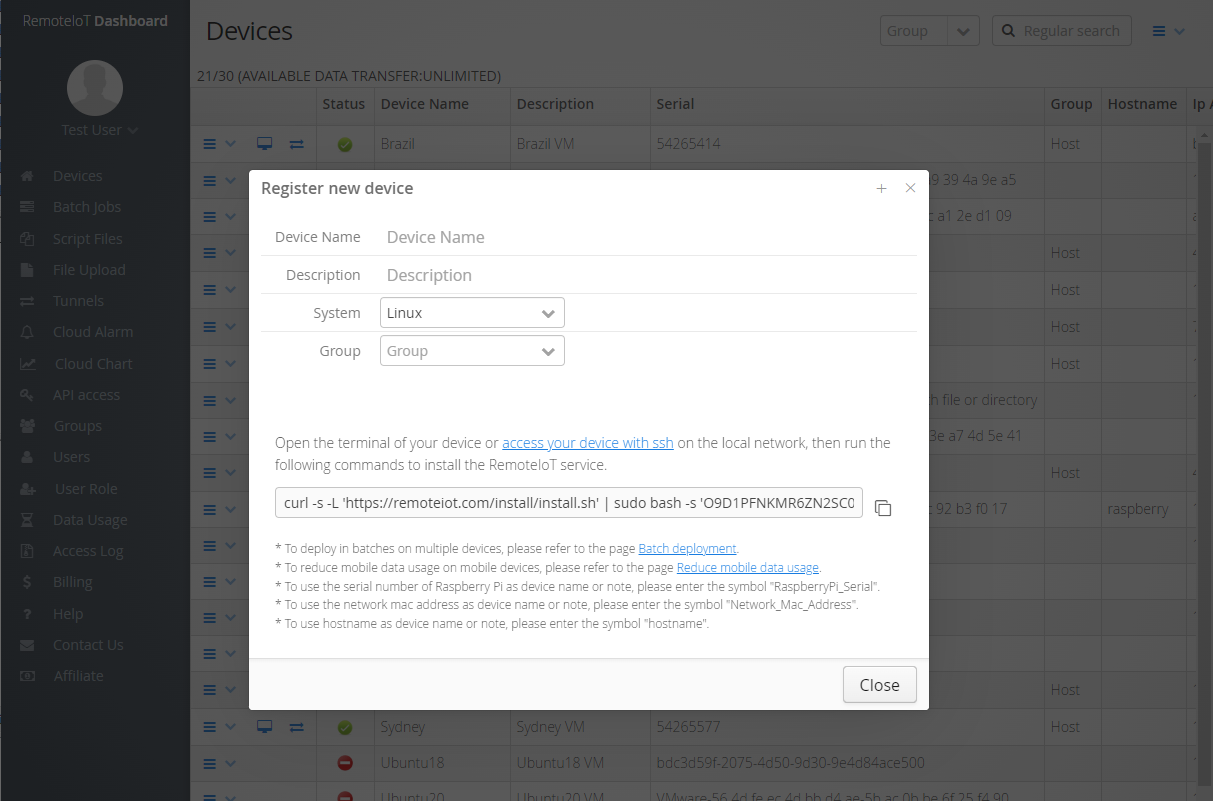
Top Remote IoT Device SSH Solutions
1. OpenSSH
OpenSSH is one of the most widely used SSH implementations, offering a comprehensive suite of tools for secure remote access. It is open-source, highly customizable, and compatible with a wide range of IoT devices.
2. Dropbear SSH
Dropbear SSH is a lightweight alternative to OpenSSH, designed specifically for resource-constrained environments. It is ideal for IoT devices with limited processing power and memory.
3. Bitvise SSH
Bitvise SSH provides a user-friendly interface and advanced features such as SFTP file transfer and tunneling. It is particularly useful for enterprise-level IoT deployments.
Choosing the Right Remote IoT Device SSH
Selecting the appropriate remote IoT device SSH solution depends on several factors:
- Device Compatibility: Ensure the SSH solution is compatible with your IoT devices' hardware and software.
- Security Features: Prioritize solutions that offer robust encryption and authentication mechanisms.
- Scalability: Choose a solution that can grow with your IoT infrastructure as it expands.
- User-Friendliness: Consider the ease of use and availability of support resources.
Security Best Practices for Remote IoT Device SSH
To maximize the security of your remote IoT device SSH setup, follow these best practices:
- Use strong, unique passwords or implement public key authentication.
- Disable root login to prevent unauthorized access.
- Regularly update SSH software to address vulnerabilities.
- Monitor SSH logs for suspicious activity and take immediate action if necessary.
Common Challenges and Solutions
Challenge: Limited Bandwidth
Solution: Optimize SSH configurations to minimize bandwidth usage, such as disabling compression for lightweight data transfers.
Challenge: Device Heterogeneity
Solution: Use universal SSH clients and servers that support a wide range of devices and operating systems.
Challenge: Security Threats
Solution: Implement multi-factor authentication and regularly audit SSH configurations for potential weaknesses.
Case Studies of Remote IoT Device SSH
Case Study 1: Smart Agriculture
In the agricultural sector, remote IoT device SSH enables farmers to monitor soil moisture levels, weather conditions, and crop health in real-time. This has led to increased productivity and reduced resource wastage.
Case Study 2: Smart Cities
Smart city initiatives rely heavily on IoT devices for traffic management, energy consumption, and public safety. Remote SSH ensures secure and reliable communication between these devices, enhancing urban living standards.
Future Trends in Remote IoT Device SSH
The future of remote IoT device SSH is promising, with several emerging trends:
- Quantum-Resistant Encryption: As quantum computing advances, SSH protocols will need to adapt to maintain security.
- Edge Computing Integration: SSH will play a crucial role in securing edge devices, enabling faster and more efficient data processing.
- Artificial Intelligence: AI-driven SSH solutions will enhance threat detection and response capabilities.
Conclusion and Call to Action
Remote IoT device SSH is a vital component of modern IoT infrastructure, offering secure and efficient remote access to devices worldwide. By understanding its importance, functionality, and best practices, you can make informed decisions to enhance your IoT security.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore our other articles for more insights into IoT and cybersecurity. Together, let's build a safer and more connected world!