SSH remote IoT example is a vital concept in modern networking and device management. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices is more important than ever. Secure Shell (SSH) plays a crucial role in this process by providing a secure method for remote access and communication. In this article, we will delve into the specifics of how SSH works in IoT environments and provide practical examples to help you better understand its applications.
With billions of connected devices globally, securing data and communication channels has become a top priority for businesses and individuals alike. SSH offers a robust solution for this challenge, enabling secure communication between IoT devices, servers, and other network components. By encrypting data during transmission, SSH helps protect sensitive information from unauthorized access and cyber threats.
In this article, we will explore the fundamental concepts of SSH in IoT, its advantages, and how to implement it effectively. Whether you're a developer, network administrator, or simply someone interested in understanding the technology behind IoT security, this guide will provide valuable insights into SSH remote IoT examples and their practical applications.
Read also:Wizards Vs Jazz A Comprehensive Analysis Of The Nba Rivalry
Table of Contents
- What is SSH?
- SSH in IoT
- Benefits of Using SSH in IoT
- How SSH Works
- SSH Remote IoT Example
- Setting Up SSH
- Best Practices for SSH in IoT
- Common Issues and Troubleshooting
- Real-World Applications of SSH in IoT
- Future Trends in SSH and IoT
What is SSH?
Secure Shell (SSH) is a cryptographic network protocol designed to enable secure communication over an unsecured network. It provides a secure channel for remote login and other secure network services. SSH uses encryption to protect data integrity, confidentiality, and authenticity during transmission. This makes it an ideal solution for managing IoT devices remotely, ensuring that communication between devices remains private and secure.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between devices, making it difficult for unauthorized parties to intercept or decipher the information.
- Authentication: SSH supports various authentication methods, including password-based and public key authentication, ensuring that only authorized users can access devices.
- Integrity: SSH ensures data integrity by using cryptographic checksums to detect any unauthorized modifications during transmission.
SSH in IoT
SSH plays a critical role in securing IoT environments. As IoT devices often operate in unsecured networks, ensuring secure communication is essential to protect sensitive data and prevent unauthorized access. SSH remote IoT example demonstrates how this protocol can be used to manage and monitor IoT devices securely.
Why Use SSH in IoT?
- Secure Communication: SSH encrypts all data transmitted between IoT devices, ensuring that sensitive information remains private and secure.
- Remote Access: SSH allows administrators to access and manage IoT devices remotely, streamlining device management and reducing the need for physical interaction.
- Scalability: SSH can be easily implemented across large IoT networks, making it a scalable solution for securing device communication.
Benefits of Using SSH in IoT
Implementing SSH in IoT environments offers several advantages, including enhanced security, improved device management, and increased efficiency. Below are some of the key benefits of using SSH in IoT:
Security Benefits
- Data Encryption: SSH encrypts all data transmitted between devices, protecting sensitive information from unauthorized access and cyber threats.
- Strong Authentication: SSH supports robust authentication methods, ensuring that only authorized users can access IoT devices.
Operational Benefits
- Remote Management: SSH enables administrators to manage IoT devices remotely, reducing the need for physical interaction and improving operational efficiency.
- Automation: SSH can be used to automate various tasks, such as device configuration and firmware updates, further streamlining device management.
How SSH Works
SSH operates by establishing a secure channel between a client and a server. The process involves several steps, including key exchange, authentication, and data encryption. Below is a brief overview of how SSH works:
Key Exchange
During the initial connection, SSH performs a key exchange to establish a shared secret between the client and server. This shared secret is used to encrypt and decrypt data during transmission.
Authentication
Once the key exchange is complete, SSH performs user authentication to verify the identity of the connecting client. This can be done using password-based or public key authentication methods.
Read also:Utah Valley Basketball Exploring The Thrilling World Of College And Local Basketball
Data Encryption
After successful authentication, SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains private and secure.
SSH Remote IoT Example
A practical example of SSH in IoT is managing a remote weather station. Suppose you have a weather station equipped with sensors to measure temperature, humidity, and wind speed. By implementing SSH, you can securely access and monitor the weather station remotely, retrieve sensor data, and perform maintenance tasks as needed.
Steps to Implement SSH in a Weather Station
- Install an SSH server on the weather station's control unit.
- Configure the SSH server to use public key authentication for added security.
- Connect to the weather station remotely using an SSH client, such as PuTTY or OpenSSH.
- Retrieve sensor data and perform maintenance tasks as required.
Setting Up SSH
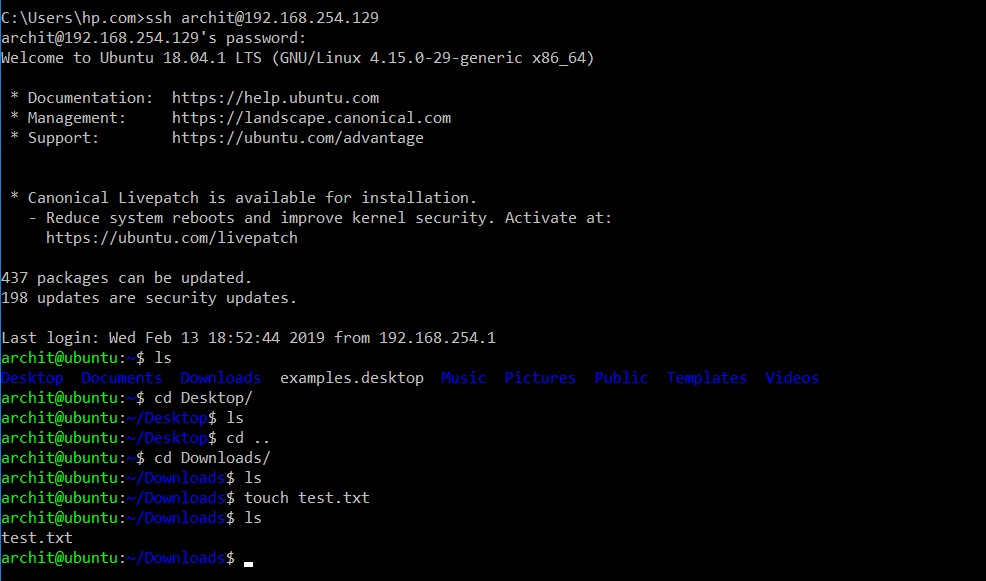
Setting up SSH in an IoT environment involves several steps, including installing an SSH server, configuring security settings, and testing the connection. Below is a step-by-step guide to setting up SSH for your IoT devices:
Installing an SSH Server
Most IoT devices come with an SSH server pre-installed. If not, you can install one using a package manager like apt or yum. For example, on a Linux-based device, you can install OpenSSH server using the following command:
sudo apt-get install openssh-server
Configuring Security Settings
To enhance security, configure the SSH server to use public key authentication instead of password-based authentication. This involves generating a public-private key pair and adding the public key to the authorized_keys file on the server.
Testing the Connection
Once the SSH server is installed and configured, test the connection by connecting to the device using an SSH client. Ensure that you can access the device securely and perform the necessary tasks.
Best Practices for SSH in IoT
To ensure the security and reliability of SSH in IoT environments, follow these best practices:
Use Strong Authentication Methods
- Implement public key authentication to reduce the risk of brute-force attacks.
- Disable password-based authentication to further enhance security.
Regularly Update Software
- Keep the SSH server and client software up-to-date to protect against known vulnerabilities.
- Apply security patches and updates promptly to maintain the integrity of your IoT environment.
Common Issues and Troubleshooting
While SSH is a robust protocol, issues can arise during implementation. Below are some common issues and solutions:
Connection Problems
- Ensure that the SSH server is running and configured correctly.
- Check firewall settings to ensure that the necessary ports are open.
Authentication Failures
- Verify that the public key is correctly added to the authorized_keys file on the server.
- Ensure that the private key is securely stored on the client device.
Real-World Applications of SSH in IoT
SSH has numerous real-world applications in IoT, including:
Smart Home Automation
SSH can be used to manage and monitor smart home devices, such as lighting systems, thermostats, and security cameras, ensuring secure communication and remote access.
Industrial IoT
In industrial settings, SSH can secure communication between machines and sensors, enabling remote monitoring and maintenance of critical infrastructure.
Future Trends in SSH and IoT
As IoT continues to evolve, so too will the role of SSH in securing device communication. Future trends in SSH and IoT include:
Quantum-Resistant Cryptography
With the advent of quantum computing, new cryptographic methods will be needed to ensure the security of SSH and IoT communication. Research into quantum-resistant algorithms is ongoing, with promising developments expected in the coming years.
AI-Driven Security
Artificial intelligence and machine learning will play an increasingly important role in enhancing SSH security, enabling real-time threat detection and automated response to potential security breaches.
Conclusion
SSH remote IoT example demonstrates the importance of secure communication in IoT environments. By implementing SSH, you can protect sensitive data, ensure secure remote access, and streamline device management. Following best practices and staying informed about future trends will help you maintain a secure and efficient IoT network.
We encourage you to share your thoughts and experiences with SSH in IoT in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics.