As technology advances, securely connecting remote IoT devices through a Virtual Private Cloud (VPC) using Raspberry Pi has become a crucial aspect of modern networking. The ability to create a private and secure connection for IoT devices ensures data integrity and privacy. Whether you're a hobbyist, developer, or enterprise professional, understanding how to implement secure IoT connections is essential. This guide will explore the steps and best practices to ensure a seamless and secure connection for your remote IoT devices.
With the growing number of IoT devices being deployed globally, the need for secure communication channels has never been more important. According to a report by Statista, the number of IoT devices is projected to reach over 25 billion by 2030. This massive growth highlights the importance of securing these devices against cyber threats. In this article, we will delve into the technical aspects of setting up a secure connection using Raspberry Pi.
This article will provide step-by-step instructions, expert insights, and practical tips to help you securely connect remote IoT devices. By the end of this guide, you'll have the knowledge and tools necessary to implement a secure VPC environment for your IoT projects. Let's dive in and explore how you can protect your IoT ecosystem while ensuring efficient data transfer.
Read also:Anna Malygon Leak A Comprehensive Analysis Of The Controversy
Table of Contents
- Introduction to Secure IoT Connections
- Understanding VPC Basics
- Setting Up Raspberry Pi for IoT
- Steps to Securely Connect Remote IoT VPC
- Essential Tools and Technologies
- Enhancing Network Security
- Protecting Data in IoT Devices
- Troubleshooting Common Issues
- Future Trends in IoT Security
- Conclusion and Next Steps
Introduction to Secure IoT Connections
IoT devices are revolutionizing industries and everyday life, but their security remains a significant concern. A secure connection ensures that sensitive data transmitted between devices remains protected from unauthorized access. Using Raspberry Pi as a central hub for IoT devices can enhance security and provide a stable platform for managing remote connections.
Connecting IoT devices through a Virtual Private Cloud (VPC) offers several advantages, including isolation from public networks and enhanced security protocols. This section will outline the importance of secure IoT connections and the role Raspberry Pi plays in this process.
Why Secure Connections Matter
Security breaches in IoT devices can lead to catastrophic consequences, from financial losses to privacy violations. Here are some key reasons why secure connections are critical:
- Preventing unauthorized access to sensitive data.
- Ensuring compliance with industry regulations.
- Protecting user privacy and maintaining trust.
Understanding VPC Basics
A Virtual Private Cloud (VPC) is a dedicated network environment that provides secure and isolated connectivity for cloud resources. By leveraging VPC, you can create a private network for your IoT devices, ensuring that communication remains secure and protected from external threats.
Key Features of VPC
VPC offers several features that make it ideal for IoT applications:
- Private IP addresses for devices.
- Customizable subnets and routing tables.
- Network access control lists (ACLs) for enhanced security.
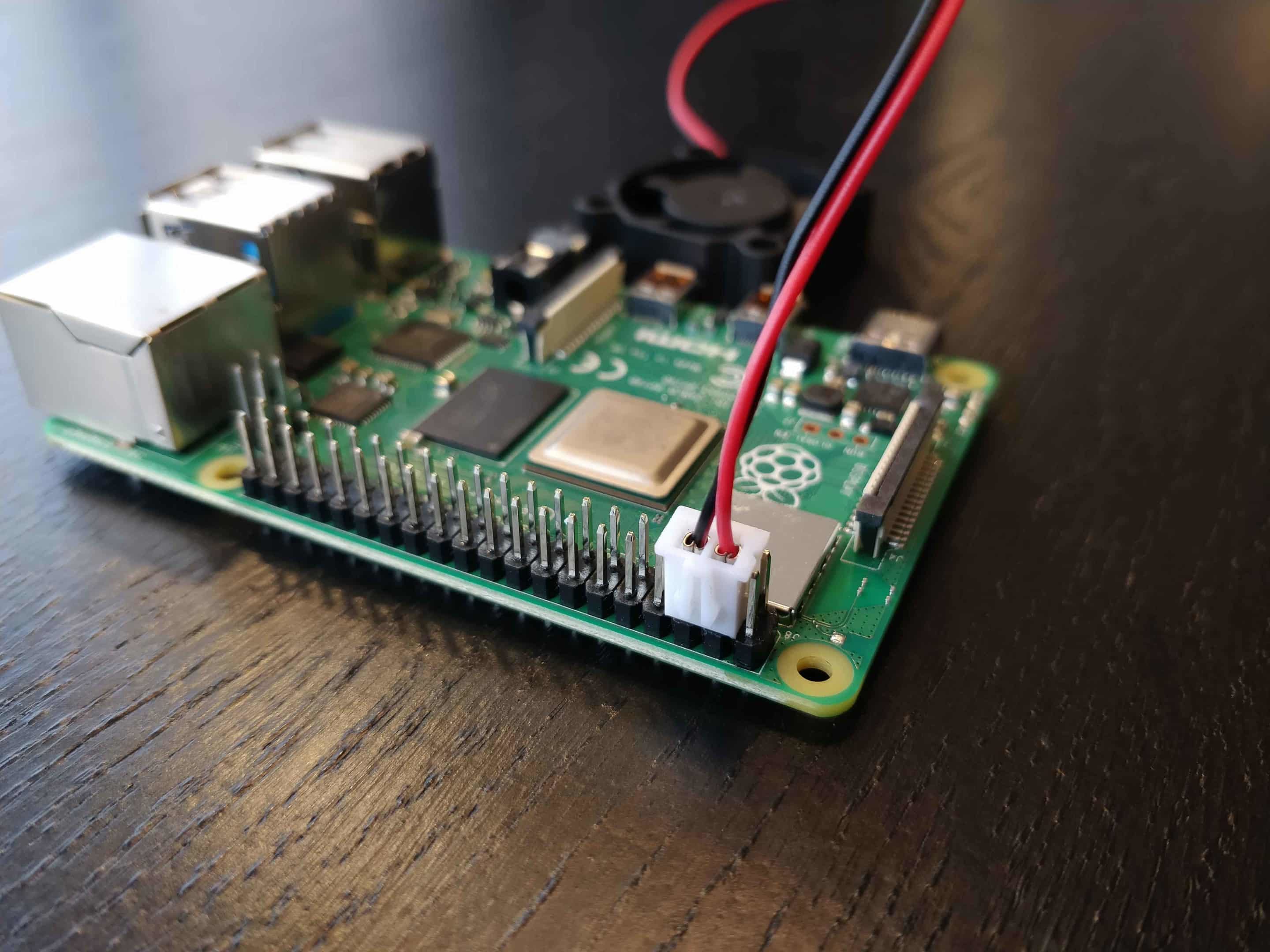
Setting Up Raspberry Pi for IoT
Raspberry Pi is a versatile and cost-effective platform for IoT projects. Setting it up correctly is the first step toward creating a secure IoT environment. This section will guide you through the initial setup process.
Read also:Michelle Williams A Journey Through Her Inspiring Career And Personal Life
Step-by-Step Raspberry Pi Setup
To set up Raspberry Pi for IoT, follow these steps:
- Install the latest version of Raspberry Pi OS.
- Configure Wi-Fi and SSH settings for remote access.
- Install necessary libraries and dependencies for IoT communication.
Steps to Securely Connect Remote IoT VPC
Securing a remote IoT connection involves multiple layers of protection. This section will outline the steps required to establish a secure VPC environment using Raspberry Pi.
1. Configure VPC Settings
Start by configuring your VPC settings to ensure proper isolation and security. Use the following guidelines:
- Create separate subnets for different types of devices.
- Implement security groups to control inbound and outbound traffic.
2. Establish Secure Communication Protocols
Using secure communication protocols like TLS/SSL ensures that data transmitted between devices remains encrypted. Here's how you can implement these protocols:
- Generate and install SSL certificates on your Raspberry Pi.
- Configure MQTT or HTTP clients to use encrypted connections.
Essential Tools and Technologies
Several tools and technologies can enhance the security of your IoT VPC environment. This section will introduce you to some of the most effective solutions.
Popular Tools for IoT Security
- Firewalls: Use firewalls to monitor and control network traffic.
- Intrusion Detection Systems (IDS): Implement IDS to detect and respond to potential threats.
Enhancing Network Security
Network security is a critical component of any IoT project. By implementing best practices, you can significantly reduce the risk of security breaches.
Best Practices for Network Security
- Regularly update firmware and software on all devices.
- Use strong passwords and enable two-factor authentication (2FA).
Protecting Data in IoT Devices
Data protection is essential to maintaining the integrity of IoT systems. This section will explore methods for safeguarding data in IoT devices.
Data Encryption Techniques
Encrypting data ensures that even if it is intercepted, it remains unreadable to unauthorized parties. Consider the following encryption techniques:
- End-to-end encryption for all data transmissions.
- Use of advanced encryption standards (AES) for data storage.
Troubleshooting Common Issues
Despite best efforts, issues may arise during the setup and operation of your IoT VPC environment. This section will address common problems and provide solutions.
Common Issues and Solutions
- Connection errors: Check network settings and ensure proper configuration.
- Security breaches: Review logs and update security protocols as needed.
Future Trends in IoT Security
The field of IoT security is constantly evolving. Staying informed about emerging trends can help you stay ahead of potential threats. This section will highlight some of the latest developments in IoT security.
Emerging Technologies
- Blockchain for secure data transactions.
- AI-driven threat detection systems.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT devices through a VPC using Raspberry Pi is a critical step in ensuring data integrity and privacy. By following the steps outlined in this guide, you can create a robust and secure IoT environment. Remember to regularly update your systems and stay informed about the latest security trends.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and cybersecurity. Together, we can build a safer and more connected world.
References:
- Statista. (2023). Internet of Things (IoT) connected devices installed base worldwide from 2015 to 2030.
- Raspberry Pi Foundation. (2023). Official Raspberry Pi Documentation.