In today's interconnected world, securely connecting remote IoT devices to a Virtual Private Cloud (VPC) is more important than ever. As businesses and individuals increasingly rely on IoT technology, ensuring robust security measures is critical to protecting sensitive data. With the rise of remote work and distributed systems, understanding how to securely connect a Raspberry Pi to your VPC is a valuable skill that can enhance your cybersecurity capabilities.
This article will provide a detailed exploration of securely connecting remote IoT devices to a VPC using Raspberry Pi. We'll cover essential topics such as setting up a secure connection, understanding VPC configurations, and downloading the necessary software for Raspberry Pi. By the end of this guide, you'll have a comprehensive understanding of how to implement secure connections for your IoT devices.
Whether you're a beginner or an experienced professional, this article aims to equip you with the knowledge and tools necessary to safeguard your IoT infrastructure. Let's dive into the world of secure IoT connections and explore how Raspberry Pi can play a pivotal role in your network's security.
Read also:76ers Vs Thunder A Deep Dive Into The Rivalry Stats And Game Analysis
Table of Contents
- Introduction to VPC
- Raspberry Pi Setup
- Secure Connection Methods
- IoT Security Challenges
- Remote Access Solutions
- Software Downloads
- Optimizing VPC Security
- Troubleshooting Tips
- Best Practices
- Conclusion
Introduction to VPC
A Virtual Private Cloud (VPC) is a private, isolated section of a cloud provider's infrastructure that allows users to deploy and manage their resources securely. By creating a VPC, you can control the networking environment, including IP address ranges, subnets, route tables, and network gateways. This level of control is essential for securely connecting remote IoT devices.
Benefits of Using VPC for IoT
Using a VPC for IoT devices offers several advantages:
- Enhanced Security: VPCs allow you to implement network-level security policies, such as firewalls and access controls.
- Scalability: VPCs can easily scale to accommodate growing numbers of IoT devices.
- Flexibility: You can customize your VPC to meet the specific needs of your IoT deployment.
Raspberry Pi Setup
The Raspberry Pi is a versatile, low-cost single-board computer that is ideal for IoT applications. Setting up a Raspberry Pi for secure IoT connections involves several steps, including installing the operating system, configuring network settings, and securing the device.
Steps for Raspberry Pi Setup
To set up your Raspberry Pi for secure IoT connections:
- Download and install the Raspberry Pi OS from the official website.
- Configure the network settings to connect to your local Wi-Fi or Ethernet network.
- Enable SSH (Secure Shell) for remote access.
- Update the operating system and install necessary security patches.
Secure Connection Methods
Securing remote IoT connections involves using reliable and secure communication protocols. Some of the most commonly used methods include:
SSL/TLS Encryption
SSL/TLS encryption ensures that data transmitted between IoT devices and the VPC is secure and protected from unauthorized access. Implementing SSL/TLS involves obtaining digital certificates and configuring your devices to use encrypted communication.
Read also:Understanding Federal Reserve Interest Rates A Comprehensive Guide
VPN Tunnels
Virtual Private Networks (VPNs) create encrypted tunnels between devices, ensuring that all data transmitted is secure. Setting up a VPN for your Raspberry Pi involves configuring the client and server settings and establishing a secure connection.
IoT Security Challenges
IoT devices present unique security challenges due to their widespread deployment and varying levels of security capabilities. Some of the key challenges include:
- Limited processing power and memory on IoT devices.
- Difficulty in updating firmware and software on deployed devices.
- Vulnerability to cyberattacks such as DDoS and malware.
Remote Access Solutions
Remote access solutions are essential for managing IoT devices securely. Tools such as SSH, Remote Desktop Protocol (RDP), and cloud-based management platforms can facilitate secure access to your devices.
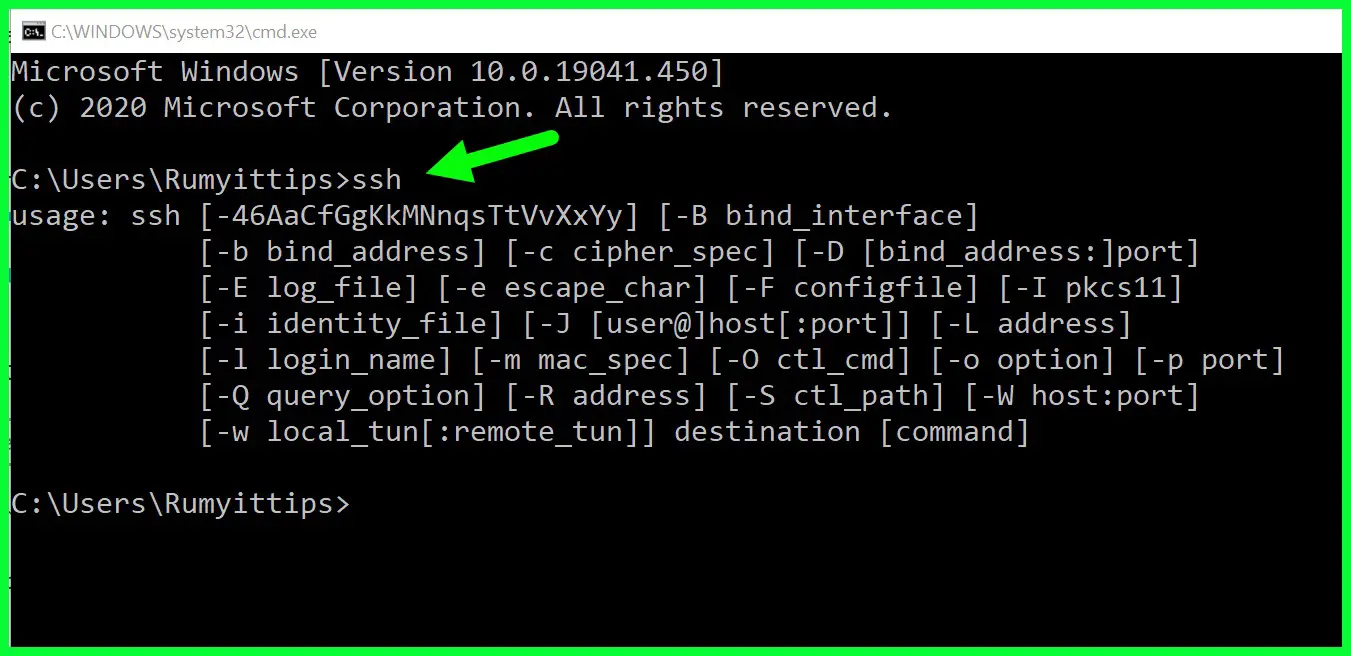
SSH for Secure Access
SSH is a widely used protocol for secure remote access. To use SSH with your Raspberry Pi:
- Enable SSH in the Raspberry Pi configuration settings.
- Generate SSH keys for authentication.
- Connect to your Raspberry Pi using an SSH client.
Software Downloads
Downloading the necessary software is a crucial step in setting up your Raspberry Pi for secure IoT connections. Some of the essential software includes:
- Raspberry Pi OS
- OpenSSL for encryption
- OpenVPN for secure connections
Ensure that you download software from official and trusted sources to avoid security risks.
Optimizing VPC Security
To optimize the security of your VPC, consider implementing the following best practices:
- Use network access control lists (ACLs) to restrict traffic.
- Regularly monitor and audit VPC activity for suspicious behavior.
- Implement multi-factor authentication (MFA) for added security.
Troubleshooting Tips
When troubleshooting secure IoT connections, consider the following tips:
- Check network configurations for errors or misconfigurations.
- Verify that all devices are running the latest firmware and software updates.
- Test connections using diagnostic tools such as ping and traceroute.
Best Practices
Adopting best practices for securing IoT devices and VPC connections is essential for maintaining robust security. Some recommended practices include:
- Regularly update and patch all devices and software.
- Implement strong password policies and use MFA where possible.
- Segment your network to isolate IoT devices from critical systems.
Conclusion
Securing remote IoT connections to a VPC using Raspberry Pi requires a combination of technical skills, knowledge of security best practices, and the right tools. By following the steps outlined in this guide, you can ensure that your IoT devices are securely connected and protected from potential threats.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with your network. For more in-depth guides and resources, explore our other articles on IoT security and Raspberry Pi configurations.