In today's digital age, remote IoT SSH example has become a crucial aspect for maintaining secure connections in IoT devices. As more organizations adopt IoT technology, understanding how to establish secure communication channels through SSH has never been more important. This article will provide a detailed exploration of remote IoT SSH examples, helping you grasp the fundamentals and best practices for secure remote access.
SSH, or Secure Shell, plays a vital role in securing communication between devices. Whether you're managing a network of IoT devices or simply ensuring that your remote access is protected, SSH offers an effective solution. This guide aims to break down the complexities of SSH and IoT integration, providing actionable insights for users at all levels.
Throughout this article, we will explore real-world examples, step-by-step instructions, and expert tips to help you implement SSH securely in your IoT infrastructure. By the end, you'll have a clear understanding of how to leverage SSH to protect your devices and networks.
Read also:Anna Malygon Leak A Comprehensive Analysis Of The Controversy
Table of Contents
- Introduction to RemoteIoT SSH
- Understanding SSH Basics
- Setting Up SSH for RemoteIoT
- Securing Your SSH Connection
- Common SSH Commands for RemoteIoT
- Troubleshooting SSH Connections
- Real-World RemoteIoT SSH Example
- Best Practices for RemoteIoT SSH
- Frequently Asked Questions
- Conclusion and Next Steps
Introduction to RemoteIoT SSH
In the rapidly evolving landscape of IoT, secure communication is paramount. RemoteIoT SSH example provides a practical way to ensure that your IoT devices remain secure while allowing for remote access. SSH offers an encrypted connection, making it a preferred method for managing IoT devices remotely.
Understanding the basics of SSH and its application in IoT can significantly enhance your ability to manage and maintain your devices. This section will explore why SSH is essential for IoT and how it contributes to secure remote access.
Why SSH is Essential for IoT
SSH serves as a secure protocol for connecting to remote devices, ensuring that data transmitted between the client and server remains encrypted and protected. For IoT devices, this encryption is vital in preventing unauthorized access and potential cyberattacks.
Understanding SSH Basics
To fully grasp remote IoT SSH example, it's important to understand the fundamentals of SSH. SSH operates on a client-server model, where the client requests access to the server through an encrypted connection.
How SSH Works
- Client-Server Model: The SSH client initiates a connection request to the SSH server.
- Authentication: Users must authenticate themselves using credentials such as passwords or public key authentication.
- Encryption: All data transmitted between the client and server is encrypted, ensuring secure communication.
Setting Up SSH for RemoteIoT
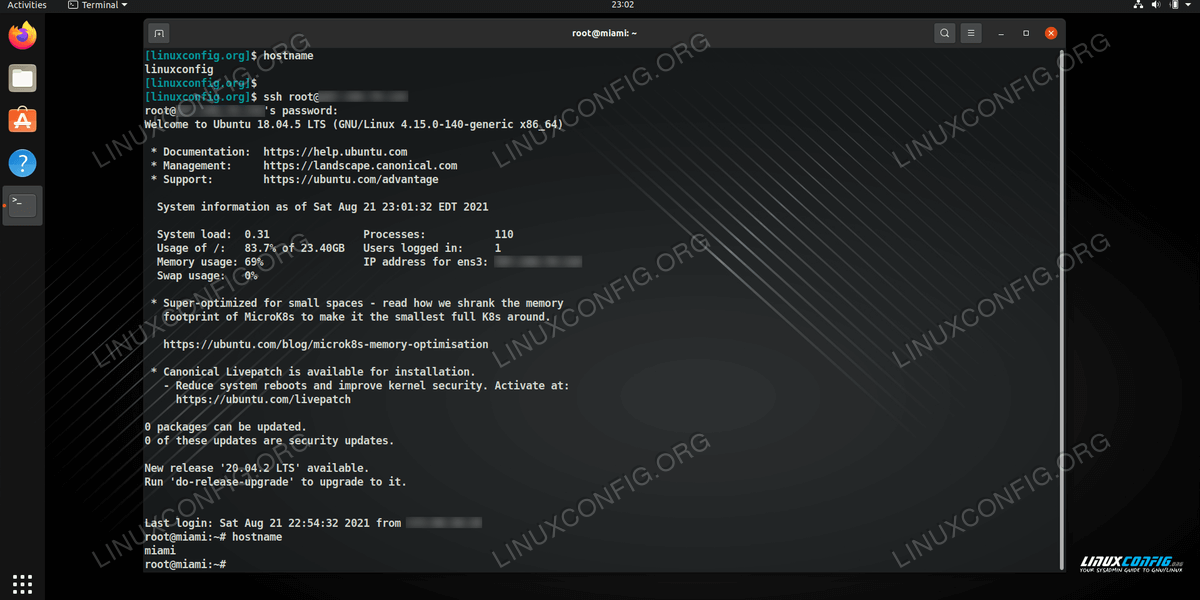
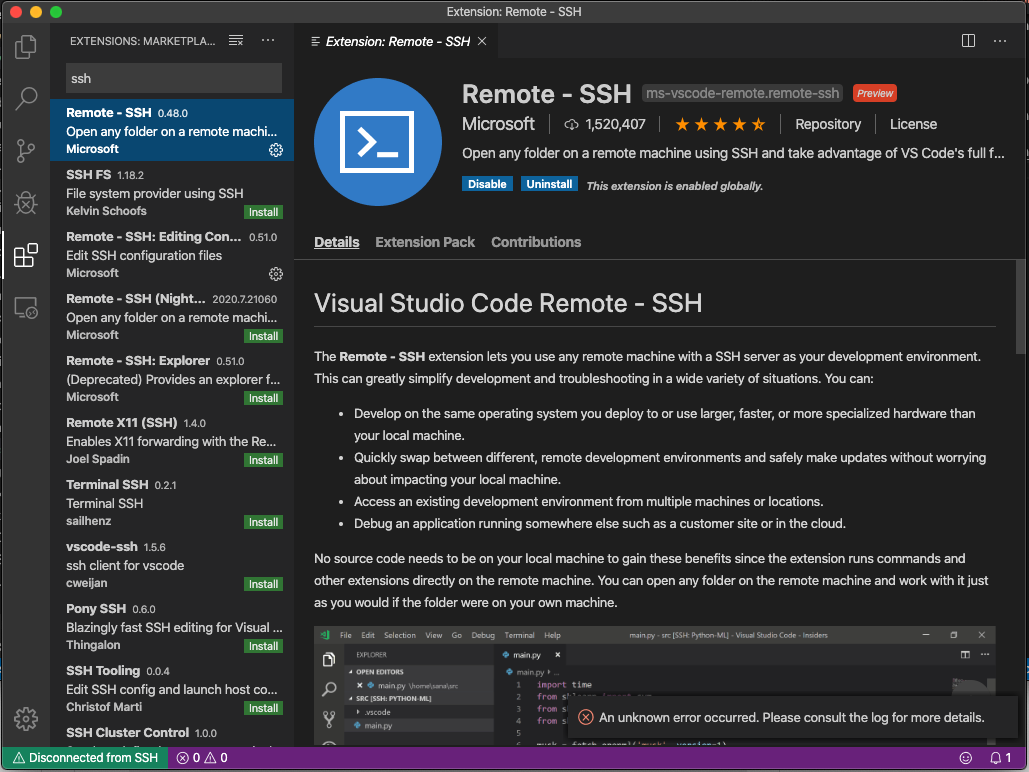
Setting up SSH for RemoteIoT involves several steps, from installing the necessary software to configuring security settings. This section will walk you through the process step-by-step, ensuring that your IoT devices are securely connected.
Step-by-Step Guide to Setting Up SSH
- Install SSH Software: Begin by installing SSH software on both the client and server devices.
- Configure SSH Settings: Adjust SSH settings to meet your security requirements, including port configuration and authentication methods.
- Test the Connection: Verify that the SSH connection is functioning correctly by attempting to connect to the server from the client.
Securing Your SSH Connection
While SSH inherently provides a secure connection, additional measures can further enhance security. This section will cover advanced techniques for securing your SSH connection, including using public key authentication and disabling password authentication.
Read also:Rui Hachimura Rising Star In The Nba
Advanced Security Measures
- Public Key Authentication: Use public key authentication to eliminate the need for password-based logins.
- Disable Password Authentication: Disable password authentication to reduce the risk of brute-force attacks.
- Limit SSH Access: Restrict SSH access to specific IP addresses or networks to enhance security.
Common SSH Commands for RemoteIoT
Familiarizing yourself with common SSH commands is essential for managing your IoT devices effectively. This section will provide a list of frequently used SSH commands, along with explanations and examples.
Essential SSH Commands
- ssh user@hostname: Connect to a remote server using SSH.
- scp file user@hostname:/path: Copy files to a remote server securely.
- ssh-keygen: Generate a public-private key pair for authentication.
Troubleshooting SSH Connections
Even with proper setup, SSH connections can sometimes fail. This section will address common issues and provide solutions to help you troubleshoot SSH connections effectively.
Common Issues and Solutions
- Connection Refused: Check firewall settings and ensure the SSH service is running on the server.
- Authentication Failure: Verify that the correct credentials are being used and that authentication methods are properly configured.
- Timeout Errors: Increase the timeout settings or check network connectivity.
Real-World RemoteIoT SSH Example
To better understand the practical application of remote IoT SSH example, let's explore a real-world scenario. Imagine managing a network of IoT sensors deployed in a remote location. By using SSH, you can securely access these sensors and retrieve data without compromising security.
Case Study: Secure Sensor Management
In this case study, a company uses SSH to manage a network of environmental sensors. By implementing SSH with public key authentication, they ensure that only authorized personnel can access the sensors, protecting sensitive data and preventing unauthorized access.
Best Practices for RemoteIoT SSH
Adopting best practices for RemoteIoT SSH can significantly improve the security and efficiency of your IoT infrastructure. This section will outline key best practices to consider when implementing SSH for IoT devices.
Key Best Practices
- Regularly Update SSH Software: Keep your SSH software up to date to protect against vulnerabilities.
- Monitor SSH Logs: Regularly review SSH logs to detect and respond to suspicious activities.
- Use Strong Authentication Methods: Implement strong authentication mechanisms, such as multi-factor authentication, to enhance security.
Frequently Asked Questions
This section addresses common questions related to remote IoT SSH example, providing clear and concise answers to help you better understand the topic.
FAQs
- What is SSH? SSH, or Secure Shell, is a protocol used for secure communication between devices.
- Why is SSH important for IoT? SSH ensures secure communication and remote access to IoT devices, protecting them from unauthorized access.
- How do I set up SSH for my IoT devices? Follow the step-by-step guide in the "Setting Up SSH for RemoteIoT" section of this article.
Conclusion and Next Steps
In conclusion, understanding remote IoT SSH example is crucial for anyone involved in IoT management. By implementing SSH effectively, you can secure your IoT devices and ensure that your remote access remains protected. Remember to follow best practices and regularly update your SSH configurations to maintain optimal security.
Call to Action: We encourage you to share your thoughts and experiences with SSH in IoT by leaving a comment below. Additionally, explore our other articles for more insights into IoT security and management.
References: