RemoteIoT VPC SSH download has become an essential topic for IT professionals, network administrators, and anyone dealing with secure cloud-based environments. As more businesses move toward remote operations, understanding how to securely manage virtual private clouds (VPCs) and implement SSH for data transfer is critical. This guide will provide you with an in-depth understanding of RemoteIoT VPC SSH download, ensuring you have the tools to enhance your cybersecurity and operational efficiency.
In today’s digital age, secure communication and data transfer are vital. RemoteIoT VPC SSH download enables seamless and secure connections between devices, servers, and networks. This technology empowers users to access remote systems while maintaining high levels of security, making it indispensable for modern cloud-based infrastructures.
This article will explore everything you need to know about RemoteIoT VPC SSH download, including its applications, setup procedures, troubleshooting tips, and best practices. Whether you're a beginner or an advanced user, this guide will provide valuable insights to enhance your skills and knowledge in this domain.
Read also:Exploring The Thrilling World Of Smu Basketball A Comprehensive Guide
Table of Contents
- Introduction to RemoteIoT VPC SSH
- Benefits of RemoteIoT VPC SSH
- Setting Up RemoteIoT VPC SSH
- Enhancing Security with RemoteIoT VPC SSH
- Common Issues and Troubleshooting
- Applications of RemoteIoT VPC SSH
- Best Practices for RemoteIoT VPC SSH
- Downloading and Installing RemoteIoT VPC SSH
- Optimizing Performance
- Future of RemoteIoT VPC SSH
Introduction to RemoteIoT VPC SSH
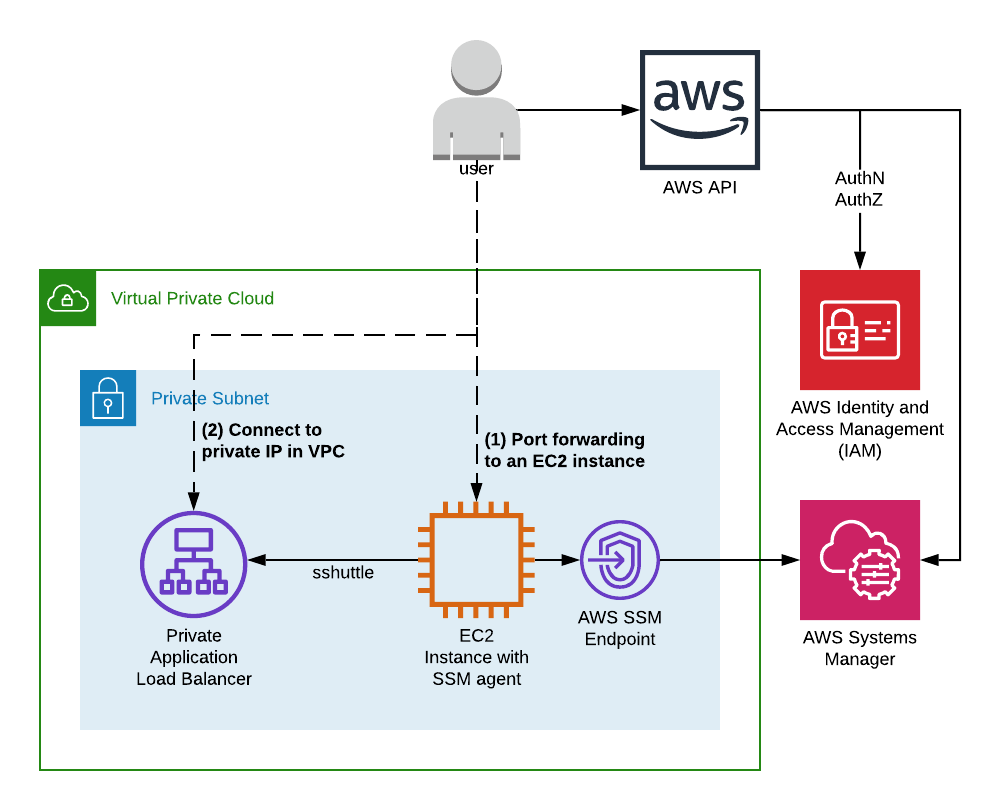
RemoteIoT VPC SSH is a powerful tool designed to facilitate secure communication between devices and networks in a virtual private cloud environment. It leverages the Secure Shell (SSH) protocol to establish encrypted connections, ensuring data integrity and confidentiality. Understanding the basics of RemoteIoT VPC SSH is crucial for anyone managing cloud-based infrastructures.
Understanding VPC and SSH
A Virtual Private Cloud (VPC) provides a secure and isolated environment for running applications and storing data. SSH, on the other hand, is a cryptographic network protocol that secures communication over untrusted networks. Combining these technologies creates a robust framework for remote access and data transfer.
Key Features of RemoteIoT VPC SSH
- End-to-end encryption
- Secure authentication mechanisms
- Scalability for large-scale deployments
- Integration with cloud platforms
Benefits of RemoteIoT VPC SSH
Implementing RemoteIoT VPC SSH offers numerous advantages for businesses and individuals alike. From enhanced security to improved operational efficiency, this technology addresses many challenges associated with remote operations.
Read also:Lee Min Ho The Iconic South Korean Actor Redefining Stardom
Enhanced Security
RemoteIoT VPC SSH ensures that all communication is encrypted, protecting sensitive data from unauthorized access. This is particularly important for industries dealing with confidential information, such as healthcare and finance.
Improved Efficiency
By streamlining remote access and data transfer processes, RemoteIoT VPC SSH allows users to focus on more critical tasks. Automation and integration capabilities further enhance productivity and reduce manual intervention.
Setting Up RemoteIoT VPC SSH
Setting up RemoteIoT VPC SSH involves several steps, from configuring the VPC environment to establishing SSH connections. Below is a step-by-step guide to help you get started.
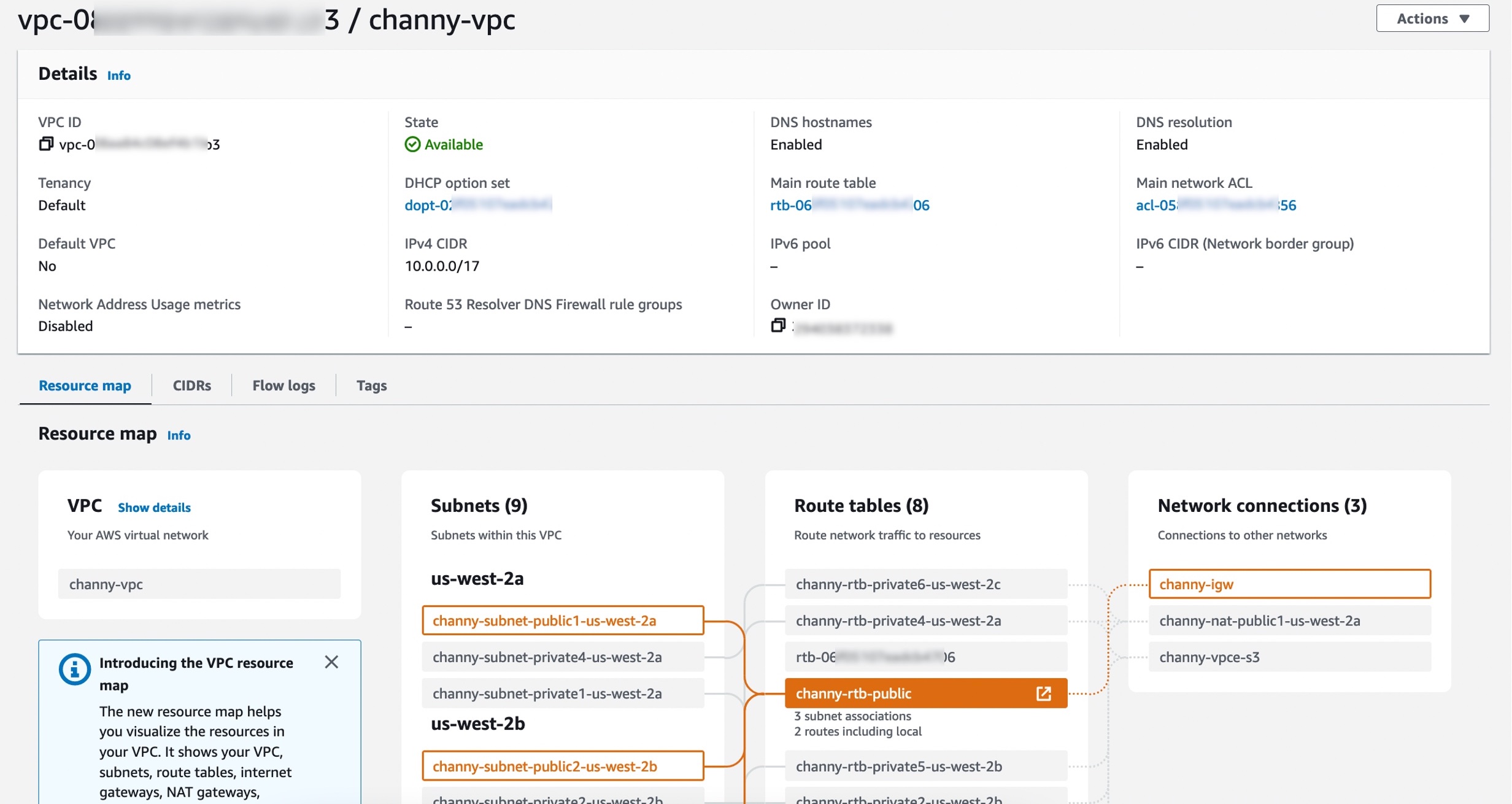
Step 1: Configure Your VPC Environment
- Create a new VPC in your cloud provider's console
- Set up subnets and routing tables
- Configure security groups and access control lists
Step 2: Install and Configure SSH
- Install an SSH client on your local machine
- Generate SSH keys for authentication
- Configure SSH settings to connect to your VPC
Enhancing Security with RemoteIoT VPC SSH
Security is a top priority when working with RemoteIoT VPC SSH. Implementing best practices can significantly reduce the risk of data breaches and unauthorized access.
Implementing Strong Authentication
Use strong passwords and multi-factor authentication (MFA) to secure your SSH connections. Additionally, regularly update and rotate SSH keys to minimize the risk of key compromise.
Monitoring and Auditing
Regularly monitor SSH activity and audit logs to detect any suspicious behavior. This proactive approach helps identify and mitigate potential security threats before they escalate.
Common Issues and Troubleshooting
Even with the best setup, issues can arise when using RemoteIoT VPC SSH. Understanding common problems and how to resolve them can save you time and frustration.
Connection Errors
Connection errors are often caused by misconfigured settings or network issues. Check your SSH configuration, firewall settings, and network connectivity to resolve these problems.
Authentication Failures
Authentication failures can occur due to incorrect SSH keys or expired credentials. Verify your keys and update them if necessary to ensure smooth authentication.
Applications of RemoteIoT VPC SSH
RemoteIoT VPC SSH has a wide range of applications across various industries. From remote system management to secure data transfer, its versatility makes it an invaluable tool for modern businesses.
Remote System Management
IT professionals use RemoteIoT VPC SSH to manage servers and devices remotely, ensuring smooth operations without the need for physical presence.
Secure Data Transfer
Organizations rely on RemoteIoT VPC SSH to transfer sensitive data securely, maintaining compliance with industry regulations and standards.
Best Practices for RemoteIoT VPC SSH
Adopting best practices is essential for maximizing the benefits of RemoteIoT VPC SSH. These practices ensure optimal performance and security while minimizing potential risks.
Regular Updates and Maintenance
Keep your SSH client and server software up to date to benefit from the latest security patches and features. Regular maintenance also helps identify and address potential issues proactively.
Documentation and Training
Document your setup and configuration processes and provide training to your team. This ensures consistency and reduces the likelihood of errors during implementation and operation.
Downloading and Installing RemoteIoT VPC SSH
Downloading and installing RemoteIoT VPC SSH is a straightforward process. Follow these steps to get started:
Step 1: Download the Software
Visit the official website or your cloud provider's portal to download the latest version of RemoteIoT VPC SSH software.
Step 2: Install and Configure
Run the installation wizard and follow the prompts to configure your SSH settings. Ensure you follow security guidelines during the setup process.
Optimizing Performance
Optimizing the performance of RemoteIoT VPC SSH involves fine-tuning various parameters to achieve the best results. Below are some tips to enhance performance:
Optimize Network Configuration
Ensure your network is configured for optimal performance, with low latency and high bandwidth. This improves the speed and reliability of SSH connections.
Compress Data Transfers
Enable data compression to reduce the size of transferred files, speeding up the transfer process and minimizing bandwidth usage.
Future of RemoteIoT VPC SSH
The future of RemoteIoT VPC SSH looks promising, with ongoing advancements in technology and increasing demand for secure remote operations. Emerging trends such as quantum computing and AI-driven cybersecurity will further enhance its capabilities.
As more businesses adopt cloud-based solutions, the role of RemoteIoT VPC SSH will continue to grow, providing robust security and seamless connectivity for remote environments.
Conclusion
RemoteIoT VPC SSH download is a critical component of modern cloud-based infrastructures, offering secure and efficient solutions for remote operations. By understanding its features, benefits, and best practices, you can harness its full potential to enhance your cybersecurity and operational efficiency.
We encourage you to explore the resources mentioned in this article and apply the knowledge gained to your projects. Don't forget to share your thoughts and experiences in the comments section below. For more insightful articles, visit our website regularly and stay updated with the latest trends in technology and cybersecurity.