In today's digital age, finding the best SSH remoteIoT free service is essential for secure and efficient remote access to your devices. Whether you're a tech enthusiast, a small business owner, or an IT professional, understanding SSH remoteIoT can significantly enhance your network security and productivity. In this comprehensive guide, we'll explore everything you need to know about SSH remoteIoT free options, including their benefits, setup processes, and security considerations.
SSH (Secure Shell) has become a cornerstone for secure communication between devices. With the rise of IoT (Internet of Things), the demand for reliable remote access solutions has grown exponentially. This article will delve into the world of SSH remoteIoT free services, helping you make informed decisions about your network infrastructure.
From understanding the basics of SSH to exploring the top free options available, this guide will equip you with the knowledge to leverage SSH remoteIoT effectively. Let's dive in and discover how you can secure your devices and streamline your operations.
Read also:Western Conference Standings A Comprehensive Guide To The Nbas Most Competitive Region
Table of Contents
- Introduction to SSH RemoteIoT Free
- What is SSH and Why is It Important?
- Integrating SSH with IoT Devices
- Benefits of Using SSH RemoteIoT Free
- Top SSH RemoteIoT Free Options
- Step-by-Step Guide to Setting Up SSH RemoteIoT
- Enhancing Security with SSH RemoteIoT
- Common Issues and Troubleshooting Tips
- Future Trends in SSH and IoT
- Conclusion and Next Steps
Introduction to SSH RemoteIoT Free
SSH remoteIoT free services have gained popularity due to their ability to provide secure and cost-effective remote access solutions. As more devices become connected through IoT, the need for robust security measures has become paramount. This section will introduce you to the concept of SSH remoteIoT and its significance in modern networking.
SSH (Secure Shell) is a cryptographic network protocol that enables secure communication between devices over an unsecured network. When combined with IoT devices, SSH ensures that data transmitted between devices remains encrypted and protected from unauthorized access. Free SSH remoteIoT services offer a viable option for individuals and businesses looking to enhance their network security without breaking the bank.
Why Choose SSH RemoteIoT?
SSH remoteIoT is preferred by many due to its reliability, ease of use, and strong security features. It allows users to remotely manage IoT devices securely, making it an ideal solution for home automation, industrial IoT, and other applications. By leveraging free SSH remoteIoT services, you can enjoy these benefits without incurring additional costs.
What is SSH and Why is It Important?
SSH, or Secure Shell, is a network protocol designed to provide secure communication between devices. It encrypts data transmitted between a client and server, ensuring that sensitive information remains protected from potential threats. Understanding SSH is crucial for anyone looking to implement secure remote access solutions.
SSH operates on port 22 by default and uses public-key cryptography to authenticate users and encrypt data. This makes it an essential tool for managing remote servers, IoT devices, and other networked systems. Its importance lies in its ability to safeguard data integrity, confidentiality, and authenticity.
Key Features of SSH
- Encryption: SSH encrypts all data transmitted between devices, preventing eavesdropping and data theft.
- Authentication: It uses public-key cryptography to authenticate users, ensuring secure access to devices.
- Command Execution: SSH allows users to execute commands on remote devices, making it a powerful tool for system administration.
Integrating SSH with IoT Devices
Integrating SSH with IoT devices is a straightforward process that enhances the security of your IoT ecosystem. By enabling SSH on your IoT devices, you can remotely manage and monitor them with confidence. This section will explore the steps involved in integrating SSH with IoT devices and the benefits it offers.
Read also:Suzy The Rising Star In The Entertainment Industry
IoT devices often lack robust security measures, making them vulnerable to attacks. SSH provides an additional layer of security by encrypting communication between devices and ensuring secure authentication. This integration is particularly useful for managing IoT devices in remote locations or monitoring them from a central control point.
Steps to Enable SSH on IoT Devices
- Install an SSH server on your IoT device.
- Configure the SSH server to use strong encryption protocols.
- Set up user authentication using public keys for enhanced security.
Benefits of Using SSH RemoteIoT Free
Using SSH remoteIoT free services offers numerous advantages, including cost savings, enhanced security, and improved productivity. This section will highlight the key benefits of leveraging SSH remoteIoT free solutions in your network infrastructure.
One of the primary benefits of SSH remoteIoT free services is their cost-effectiveness. By opting for free solutions, you can reduce operational expenses while maintaining high levels of security. Additionally, SSH remoteIoT free services are highly reliable, ensuring seamless connectivity and minimal downtime.
Top Benefits
- Cost-Effective: Free SSH remoteIoT services eliminate the need for paid subscriptions.
- Secure: SSH encrypts all data transmissions, protecting sensitive information from unauthorized access.
- Flexible: Supports a wide range of devices and platforms, making it versatile for various use cases.
Top SSH RemoteIoT Free Options
Several SSH remoteIoT free options are available, each offering unique features and capabilities. In this section, we will explore some of the top SSH remoteIoT free services that you can consider for your network needs.
Option 1: OpenSSH
OpenSSH is a widely used SSH implementation that provides robust security features and is compatible with a variety of platforms. It is open-source and free to use, making it an excellent choice for individuals and organizations looking to secure their IoT devices.
Option 2: Bitvise SSH
Bitvise SSH offers a user-friendly interface and supports advanced security features such as two-factor authentication. While it offers a free version for personal use, its enterprise edition is available for businesses requiring additional functionality.
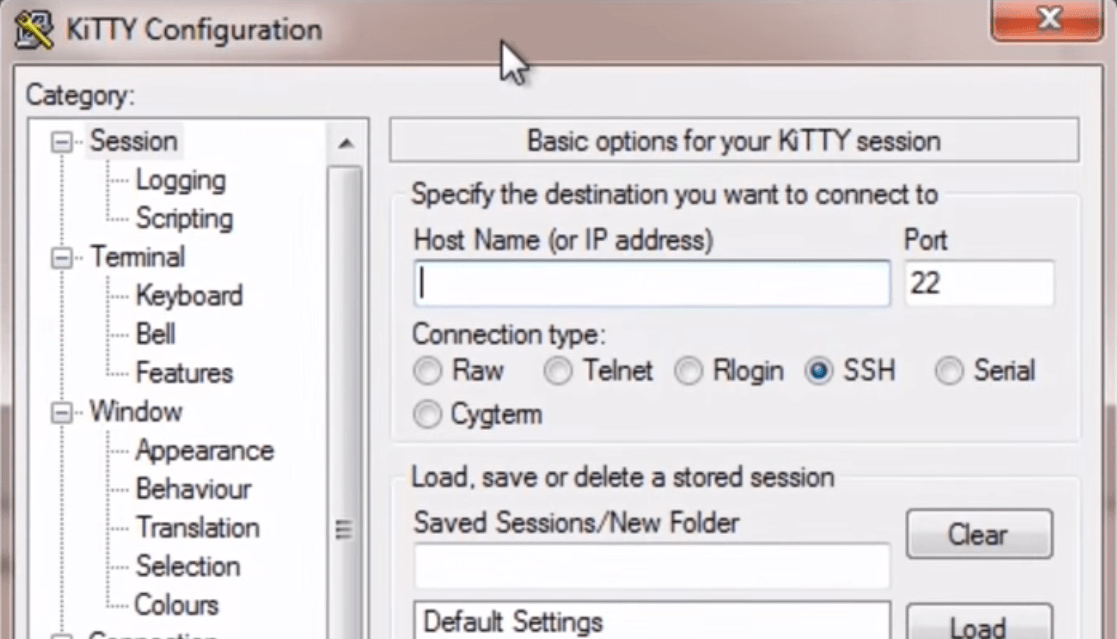
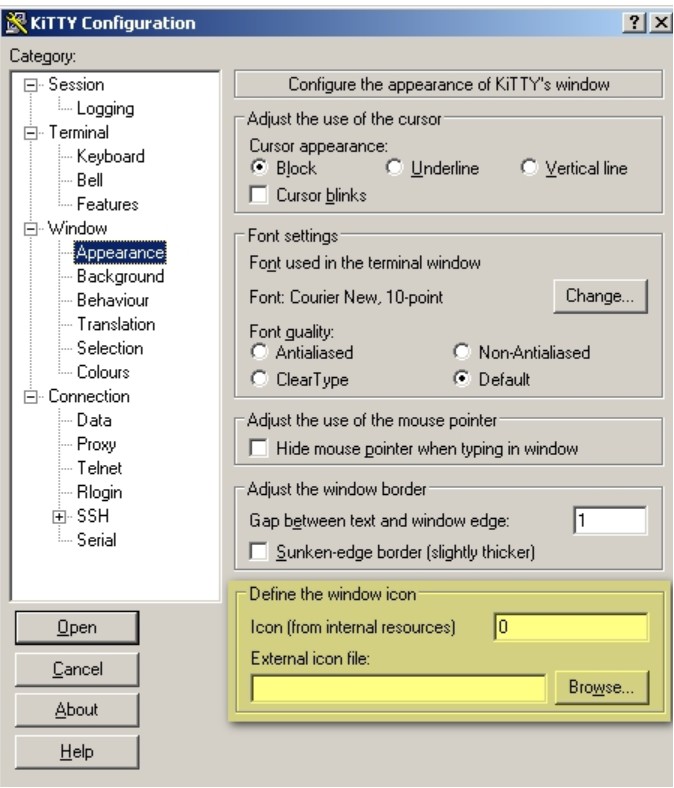
Option 3: PuTTY
PuTTY is a lightweight SSH client that is easy to use and supports multiple platforms. It is an ideal choice for beginners who want to explore SSH remoteIoT without investing in expensive software solutions.
Step-by-Step Guide to Setting Up SSH RemoteIoT
Setting up SSH remoteIoT involves several steps, including installing an SSH server, configuring security settings, and testing connectivity. This section will provide a detailed guide to help you set up SSH remoteIoT effectively.
Step 1: Install an SSH Server
Begin by installing an SSH server on your IoT device. Popular options include OpenSSH for Linux-based systems and Bitvise SSH for Windows-based systems. Ensure that the server is configured to use strong encryption protocols and secure authentication methods.
Step 2: Configure Security Settings
Once the SSH server is installed, configure its security settings to enhance protection. Disable password-based authentication and enable public-key authentication for added security. Additionally, consider using a non-standard port to reduce the risk of brute-force attacks.
Step 3: Test Connectivity
After configuring the SSH server, test its connectivity by connecting to it from a remote client. Use an SSH client such as PuTTY or OpenSSH to establish a secure connection and verify that all settings are functioning correctly.
Enhancing Security with SSH RemoteIoT
Security is a critical consideration when using SSH remoteIoT. This section will discuss various strategies to enhance the security of your SSH remoteIoT setup and protect your devices from potential threats.
Implementing strong security measures is essential to safeguard your IoT devices and prevent unauthorized access. Regularly update your SSH server and client software to ensure that you have the latest security patches and features. Additionally, monitor your network for suspicious activity and take immediate action if any threats are detected.
Best Practices for SSH Security
- Use strong, unique passwords and enable two-factor authentication.
- Regularly update your SSH software to address security vulnerabilities.
- Monitor your network for unusual activity and respond promptly to any threats.
Common Issues and Troubleshooting Tips
While SSH remoteIoT is generally reliable, you may encounter issues during setup or operation. This section will address common problems and provide troubleshooting tips to help you resolve them quickly.
Some common issues include connection failures, authentication errors, and configuration problems. By following the troubleshooting steps outlined below, you can address these issues and ensure smooth operation of your SSH remoteIoT setup.
Troubleshooting Tips
- Check your network settings and ensure that the SSH server is accessible.
- Verify that your SSH client is configured correctly and supports the required protocols.
- Review your SSH server logs for any error messages or warnings.
Future Trends in SSH and IoT
The future of SSH and IoT looks promising, with advancements in technology driving innovation in secure communication. This section will explore emerging trends in SSH and IoT and how they may impact the way we manage and secure our devices.
As IoT continues to evolve, the demand for secure and efficient remote access solutions will increase. SSH is expected to play a vital role in this landscape, providing robust security features and seamless connectivity for IoT devices. Additionally, advancements in encryption technologies and authentication methods will further enhance the security of SSH remoteIoT solutions.
Conclusion and Next Steps
In conclusion, SSH remoteIoT free services offer a cost-effective and secure solution for managing IoT devices remotely. By understanding the basics of SSH and exploring the top free options available, you can enhance your network security and productivity. Remember to implement best practices for SSH security and regularly update your software to address potential vulnerabilities.
We encourage you to take action by exploring the SSH remoteIoT free options discussed in this guide and implementing them in your network infrastructure. Don't forget to share your thoughts and experiences in the comments section below. For more insightful articles on technology and networking, visit our website regularly and stay updated with the latest trends and developments.