RemoteIoT monitoring SSH has become a crucial component for businesses and individuals seeking to manage IoT devices securely from a distance. With the rapid growth of IoT technology, ensuring secure and efficient remote access is more important than ever. This article will explore the best practices, tools, and strategies for remote IoT monitoring using SSH, particularly focusing on free downloadable tools for Mac users.
As the Internet of Things (IoT) continues to expand, the need for secure remote access solutions increases. RemoteIoT monitoring through SSH offers a robust way to manage devices without compromising security. Whether you're a tech enthusiast, a small business owner, or an enterprise IT professional, this article will provide valuable insights into leveraging SSH for remote IoT monitoring.
In this guide, we'll delve into the significance of SSH in IoT management, the best tools available for Mac users, and how to set up and use these tools effectively. By the end of this article, you'll have a comprehensive understanding of how to implement secure remote IoT monitoring using SSH on your Mac.
Read also:Tre Johnson The Rising Star In The Music Industry
Table of Contents
- Introduction to RemoteIoT Monitoring SSH
- What is SSH and Why is It Important?
- Benefits of RemoteIoT Monitoring with SSH
- Top Tools for RemoteIoT Monitoring SSH on Mac
- Step-by-Step Setup Guide
- Security Best Practices for RemoteIoT Monitoring
- Common Issues and Troubleshooting
- Performance Optimization Tips
- Future Trends in RemoteIoT Monitoring
- Conclusion
Introduction to RemoteIoT Monitoring SSH
RemoteIoT monitoring SSH is a powerful solution for managing IoT devices securely from anywhere in the world. Secure Shell (SSH) is a cryptographic network protocol that allows users to access remote systems securely over an unsecured network. This technology is widely used in IoT environments to ensure data integrity, confidentiality, and availability.
For Mac users, there are numerous free tools available that enable remote IoT monitoring through SSH. These tools provide a user-friendly interface and robust security features, making them ideal for both beginners and advanced users. In this section, we'll explore the basics of SSH and its role in IoT management.
What is SSH and Why is It Important?
Secure Shell (SSH) is a protocol that facilitates secure communication between two networked devices. It is widely used for remote command-line login and other secure network services. SSH encrypts all data transmitted between the client and server, ensuring that sensitive information remains protected from unauthorized access.
Key Features of SSH
- Data Encryption: SSH uses strong encryption algorithms to protect data during transmission.
- Authentication: It provides robust authentication mechanisms to verify the identity of users and devices.
- Integrity: SSH ensures that data is not tampered with during transmission.
SSH is particularly important in IoT environments, where devices are often deployed in remote locations and require secure access for management and maintenance.
Benefits of RemoteIoT Monitoring with SSH
Implementing SSH for remote IoT monitoring offers several advantages:
- Enhanced Security: SSH provides end-to-end encryption, ensuring that sensitive data is protected from cyber threats.
- Scalability: It can handle large-scale IoT deployments, making it suitable for enterprise-level applications.
- Reliability: SSH connections are stable and reliable, even in challenging network conditions.
These benefits make SSH an essential tool for anyone managing IoT devices remotely.
Read also:Southern University A Comprehensive Guide To One Of Americas Premier Institutions
Top Tools for RemoteIoT Monitoring SSH on Mac
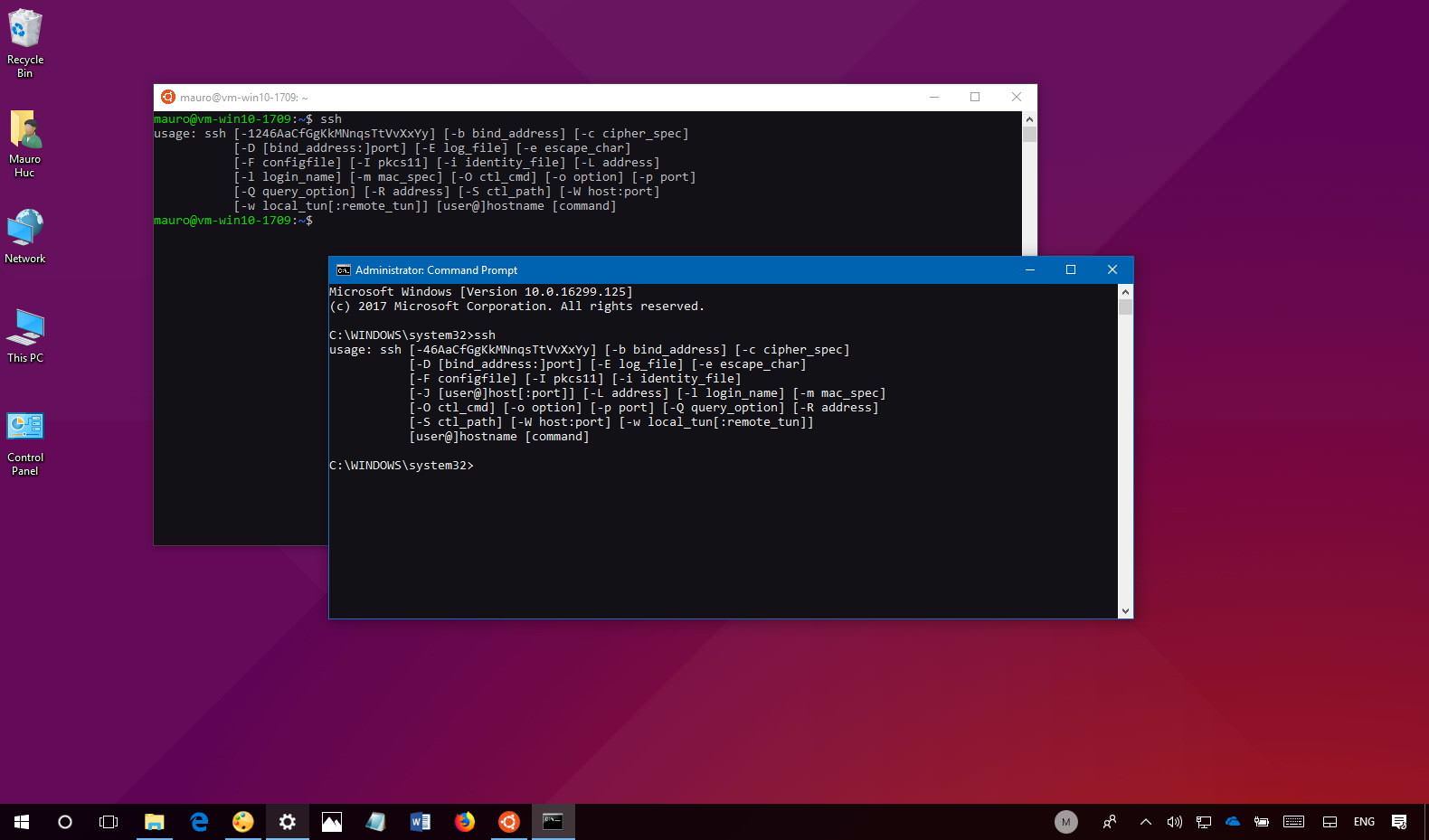
There are several free tools available for Mac users who want to implement remote IoT monitoring using SSH. Below are some of the most popular options:
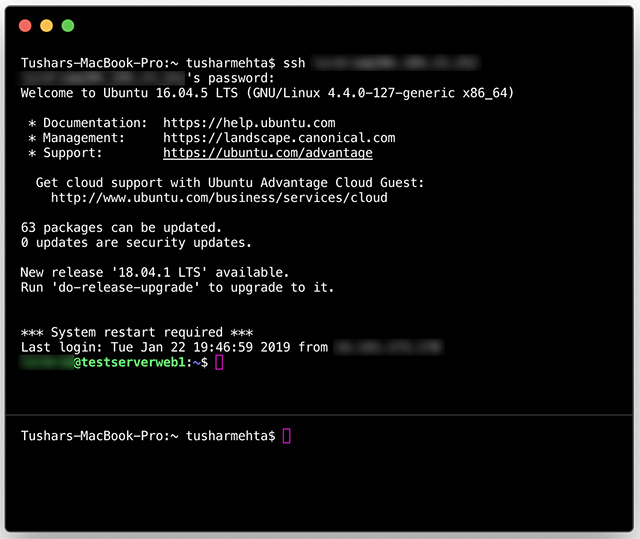
1. Terminal
Terminal is a built-in application on macOS that allows users to connect to remote servers via SSH. It is lightweight, easy to use, and offers all the necessary features for secure remote access.
2. iTerm2
iTerm2 is an enhanced terminal emulator for macOS that offers additional features such as split panes, autocomplete, and advanced customization options. It is a popular choice among developers and power users.
3. Mosh
Mosh (Mobile Shell) is an alternative to SSH that is optimized for unreliable network connections. It allows users to maintain a stable connection even when switching networks or experiencing high latency.
These tools provide a solid foundation for remote IoT monitoring on Mac, ensuring secure and efficient access to IoT devices.
Step-by-Step Setup Guide
Setting up remote IoT monitoring using SSH on Mac is a straightforward process. Follow these steps to get started:
Step 1: Install the Necessary Tools
Ensure that you have the required tools installed on your Mac. For most users, Terminal will suffice, but you can also install iTerm2 or Mosh for additional features.
Step 2: Configure SSH on the IoT Device
Enable SSH on the IoT device you wish to monitor. This typically involves accessing the device's settings and enabling the SSH service.
Step 3: Connect to the Device
Open Terminal or your preferred SSH client and enter the following command:
ssh username@device-ip-address
Replace "username" with your IoT device's username and "device-ip-address" with the device's IP address.
Step 4: Verify the Connection
Once connected, verify that you can access the device's files and execute commands. This ensures that the SSH setup is functioning correctly.
Security Best Practices for RemoteIoT Monitoring
While SSH provides robust security features, it is essential to follow best practices to maximize protection. Below are some recommendations:
- Use Strong Passwords: Ensure that all user accounts have strong, unique passwords.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by enabling 2FA for SSH access.
- Regularly Update Software: Keep your SSH client and server software up to date to protect against vulnerabilities.
By implementing these practices, you can significantly reduce the risk of unauthorized access to your IoT devices.
Common Issues and Troubleshooting
While SSH is a reliable protocol, users may encounter issues during setup or operation. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH service is enabled on the IoT device and that the IP address is correct.
- Authentication Failed: Verify that the username and password are correct and that the account has SSH access privileges.
- Timeout Errors: Check the network connection and ensure that there are no firewall rules blocking SSH traffic.
If these solutions do not resolve the issue, consult the device's documentation or seek assistance from the manufacturer's support team.
Performance Optimization Tips
To ensure optimal performance when using SSH for remote IoT monitoring, consider the following tips:
- Use Compression: Enable compression to reduce the amount of data transmitted over the network.
- Limit Bandwidth Usage: Configure SSH settings to limit bandwidth usage, especially on slower connections.
- Optimize SSH Configuration: Fine-tune SSH settings to improve connection speed and reliability.
These optimizations can help improve the efficiency of your remote IoT monitoring setup.
Future Trends in RemoteIoT Monitoring
The field of remote IoT monitoring is rapidly evolving, with new technologies and innovations emerging regularly. Some of the key trends to watch include:
- AI Integration: Artificial intelligence is being used to enhance IoT monitoring by providing predictive analytics and automated decision-making.
- Edge Computing: Processing data closer to the source reduces latency and improves overall performance.
- Quantum Cryptography: This emerging technology promises to provide even stronger security for IoT communications.
Staying informed about these trends will help you stay ahead in the rapidly changing landscape of IoT technology.
Conclusion
In conclusion, remote IoT monitoring using SSH is a powerful and secure solution for managing IoT devices from a distance. By leveraging the tools and best practices outlined in this article, you can ensure that your IoT devices remain secure and accessible at all times.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT technology and related topics. Together, let's build a safer and more connected world!
References: