SSH remote device is an essential tool for securely managing and accessing remote systems. Whether you're a developer, network administrator, or IT professional, understanding SSH and its applications can significantly enhance your workflow. This guide will walk you through everything you need to know about SSH remote connections, from the basics to advanced configurations.
In today's interconnected world, where remote work and cloud computing are becoming increasingly prevalent, secure communication between devices is crucial. SSH (Secure Shell) serves as a robust protocol for encrypted communication, protecting sensitive data and ensuring secure access to remote servers and devices.
This article aims to provide in-depth insights into SSH remote device management, covering everything from its fundamental principles to practical implementations. By the end of this guide, you'll have a solid understanding of how to leverage SSH for secure and efficient remote operations.
Read also:Man City Vs Chelsea A Thrilling Rivalry In The Premier League
Table of Contents
- Introduction to SSH Remote Device
- How SSH Works
- Benefits of Using SSH for Remote Connections
- Setting Up SSH
- Securing SSH Connections
- Common SSH Commands
- Troubleshooting SSH Issues
- Best Practices for SSH Remote Device Management
- Alternatives to SSH for Remote Access
- Conclusion
Introduction to SSH Remote Device
SSH remote device management is a fundamental aspect of modern IT infrastructure. SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication between a client and a server over an unsecured network. It provides a secure channel for file transfers, command execution, and remote administration.
What is SSH?
SSH is more than just a protocol; it's a powerful tool that ensures the confidentiality and integrity of data transmitted between devices. It uses encryption algorithms to protect sensitive information, making it a preferred choice for remote access solutions.
Why Use SSH for Remote Devices?
Compared to other protocols like Telnet, SSH offers unparalleled security features. It encrypts all data exchanges, authenticates users securely, and protects against unauthorized access. These attributes make SSH ideal for managing remote devices, especially in environments where security is paramount.
How SSH Works
Understanding how SSH operates is crucial for effectively utilizing it in your workflows. The protocol establishes a secure connection between a client and a server through a series of steps:
- Connection Initiation: The client sends a request to the server to initiate a connection.
- Key Exchange: The client and server exchange encryption keys to establish a secure channel.
- User Authentication: The user is authenticated using passwords, public keys, or other methods.
- Secure Session: Once authenticated, a secure session is established, allowing encrypted communication.
This process ensures that all data transmitted between the client and server remains confidential and tamper-proof.
Benefits of Using SSH for Remote Connections
SSH offers numerous advantages for remote device management:
Read also:Nba Standings A Comprehensive Guide To Tracking Your Favorite Teams
- Security: SSH encrypts all data exchanges, protecting sensitive information from interception.
- Flexibility: It supports various authentication methods, including passwords, public keys, and certificates.
- Reliability: SSH ensures stable connections even over unstable networks.
- Automation: It facilitates automated tasks through scripting and integration with other tools.
These benefits make SSH a versatile and dependable solution for remote access and management.
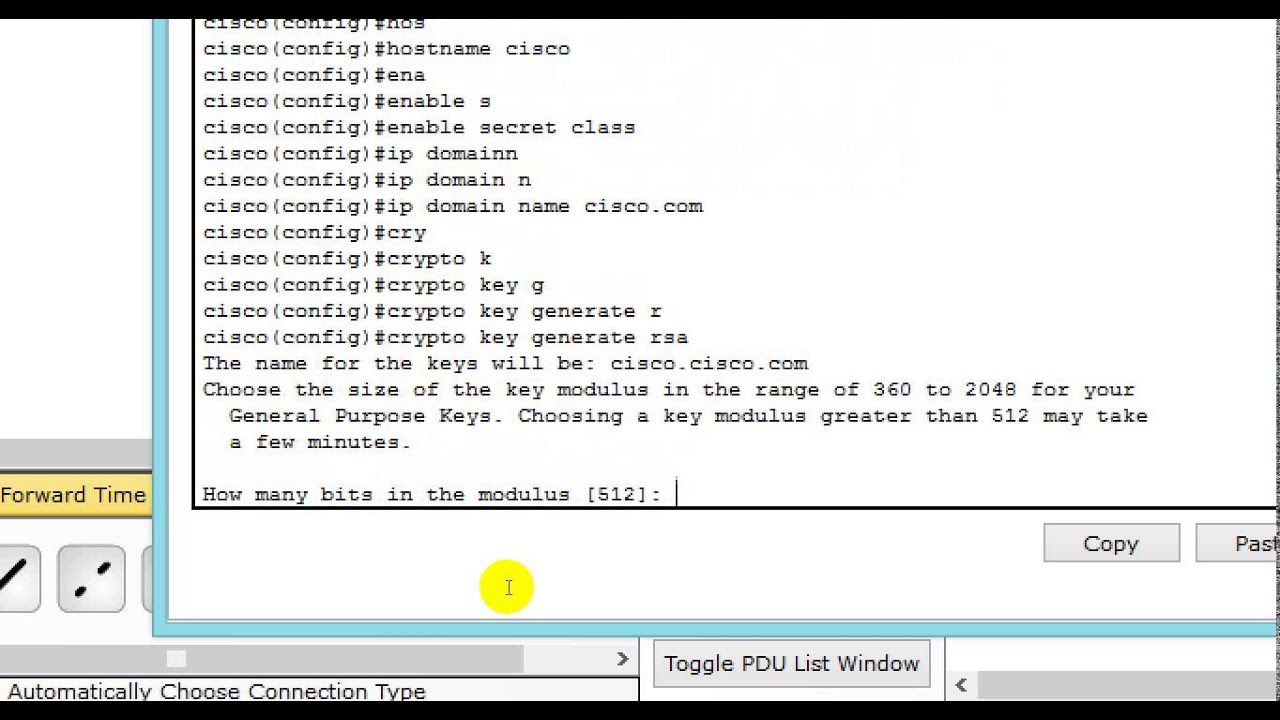
Setting Up SSH
Setting up SSH involves configuring both the client and server components. Below are the steps to get started:
Installing SSH Client and Server
On most Linux and macOS systems, SSH is pre-installed. For Windows, you may need to install an SSH client like OpenSSH or PuTTY. To install the SSH server on a Linux machine, use the following command:
sudo apt-get install openssh-server
Configuring SSH
Once installed, you can configure SSH by editing the /etc/ssh/sshd_config file. Key configurations include:
- Port number for SSH connections.
- Authentication methods (passwords, public keys).
- Permitted users or groups.
After making changes, restart the SSH service to apply them:
sudo systemctl restart ssh
Securing SSH Connections
While SSH is inherently secure, additional measures can further enhance its protection:
Use Strong Passwords
Ensure that all user accounts have strong, complex passwords to prevent unauthorized access.
Disable Password Authentication
Switch to public key authentication to eliminate the risk of brute-force attacks:
sudo nano /etc/ssh/sshd_config
Set PasswordAuthentication no and restart the SSH service.
Implement Firewall Rules
Restrict SSH access to specific IP addresses or networks using firewall rules:
sudo ufw allow from 192.168.1.0/24 to any port 22
This limits potential attack vectors and enhances security.
Common SSH Commands
Mastering SSH commands is essential for efficient remote device management. Below are some frequently used commands:
- ssh user@hostname: Connect to a remote server.
- scp file user@hostname:/path: Copy files to a remote server.
- ssh-keygen: Generate public and private keys for authentication.
- ssh-copy-id user@hostname: Copy your public key to a remote server.
These commands streamline remote operations and improve productivity.
Troubleshooting SSH Issues
Despite its reliability, SSH connections can occasionally encounter problems. Here are some common issues and their solutions:
Connection Refused
This error typically occurs when the SSH service is not running or the port is blocked. Check the SSH service status and firewall settings to resolve the issue.
Authentication Failed
Ensure that the username, password, or key file is correct. Verify the server's configuration file for authentication settings.
Timeout Errors
Timeouts may result from network instability or excessive connection attempts. Adjust the server's timeout settings to address this problem.
Best Practices for SSH Remote Device Management
To maximize the effectiveness and security of SSH, follow these best practices:
- Regularly Update SSH: Keep your SSH client and server software up to date with the latest security patches.
- Monitor Logs: Review SSH logs for suspicious activities and potential security breaches.
- Limit User Access: Restrict SSH access to authorized users and disable root login.
- Use Non-Standard Ports: Change the default SSH port (22) to reduce automated attack attempts.
Implementing these practices ensures a secure and efficient SSH environment.
Alternatives to SSH for Remote Access
While SSH is the gold standard for remote device management, other tools and protocols exist:
Remote Desktop Protocol (RDP)
RDP is commonly used for graphical remote access on Windows systems. It provides a user-friendly interface but lacks the command-line flexibility of SSH.
Virtual Network Computing (VNC)
VNC allows remote control of graphical interfaces across platforms. However, it is less secure than SSH and requires additional configuration for encryption.
Web-Based Solutions
Cloud-based platforms like AWS Systems Manager offer web-based remote access, eliminating the need for SSH clients. These solutions are convenient but may introduce latency and dependency on third-party services.
Conclusion
SSH remote device management is a powerful and secure solution for accessing and managing remote systems. By understanding its principles, configurations, and best practices, you can harness its full potential to enhance your IT operations. Remember to prioritize security, regularly update your SSH setup, and explore alternatives when appropriate.
We invite you to share your thoughts and experiences with SSH in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IT and networking topics. Together, let's build a safer and more efficient digital world!