In today's interconnected world, securely connecting remote IoT devices has become a critical task for businesses and individuals alike. With the rise of cloud computing and edge devices, understanding how to set up a Virtual Private Cloud (VPC) and integrate it with a Raspberry Pi for seamless communication is essential. Moreover, downloading and using Windows for free in certain scenarios can significantly reduce costs while enhancing security.
This guide will walk you through the process of securely connecting remote IoT devices, configuring a VPC, and leveraging a Raspberry Pi as a bridge. Whether you're a developer, hobbyist, or IT professional, this article will provide you with actionable insights and practical steps to achieve your goals.
From understanding the fundamentals of IoT security to exploring advanced configurations, we'll cover everything you need to know. By the end of this guide, you'll have the knowledge and tools to set up a secure and efficient system that aligns with modern cybersecurity standards.
Read also:Eliminatorias Conmebol The Ultimate Guide To South Americas Road To The World Cup
Table of Contents
- Introduction
- Understanding IoT Security
- VPC Configuration for Remote IoT Devices
- Setting Up Raspberry Pi for IoT
- Secure Connection Methods for IoT Devices
- Windows Free Download Options
- Best Practices for Securing IoT Devices
- Troubleshooting Common Issues
- Case Studies: Real-World Applications
- Conclusion
Introduction
The Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices are becoming increasingly prevalent. However, with this growth comes the challenge of ensuring secure communication between devices, especially when they are located remotely.
One of the most effective ways to secure remote IoT devices is by leveraging a Virtual Private Cloud (VPC). A VPC allows you to create an isolated network environment where your IoT devices can communicate securely. Additionally, integrating a Raspberry Pi into your setup can provide a cost-effective and flexible solution for managing these devices.
Understanding IoT Security
Why IoT Security Matters
IoT security is critical because connected devices often handle sensitive data. Whether it's personal information from smart home devices or operational data from industrial sensors, ensuring the security of this information is paramount. Without proper security measures, IoT devices can become vulnerable to cyberattacks, data breaches, and unauthorized access.
Common IoT Security Threats
- Data breaches: Unauthorized access to sensitive information.
- Device hijacking: Attackers gaining control of IoT devices.
- Denial of Service (DoS) attacks: Overloading devices or networks to disrupt operations.
- Firmware vulnerabilities: Exploiting outdated or poorly configured firmware.
VPC Configuration for Remote IoT Devices
What is a Virtual Private Cloud (VPC)?
A Virtual Private Cloud (VPC) is a virtual network dedicated to your AWS environment. It enables you to launch resources in a logically isolated section of the cloud, providing you with complete control over your network configuration. By setting up a VPC, you can enhance the security of your remote IoT devices by isolating them from the public internet.
Steps to Configure a VPC
Configuring a VPC involves several key steps:
- Create a VPC in your preferred cloud provider (e.g., AWS).
- Set up subnets to divide your network into smaller segments.
- Configure security groups to control inbound and outbound traffic.
- Assign Elastic IP addresses to ensure consistent communication.
Setting Up Raspberry Pi for IoT
Why Use Raspberry Pi for IoT?
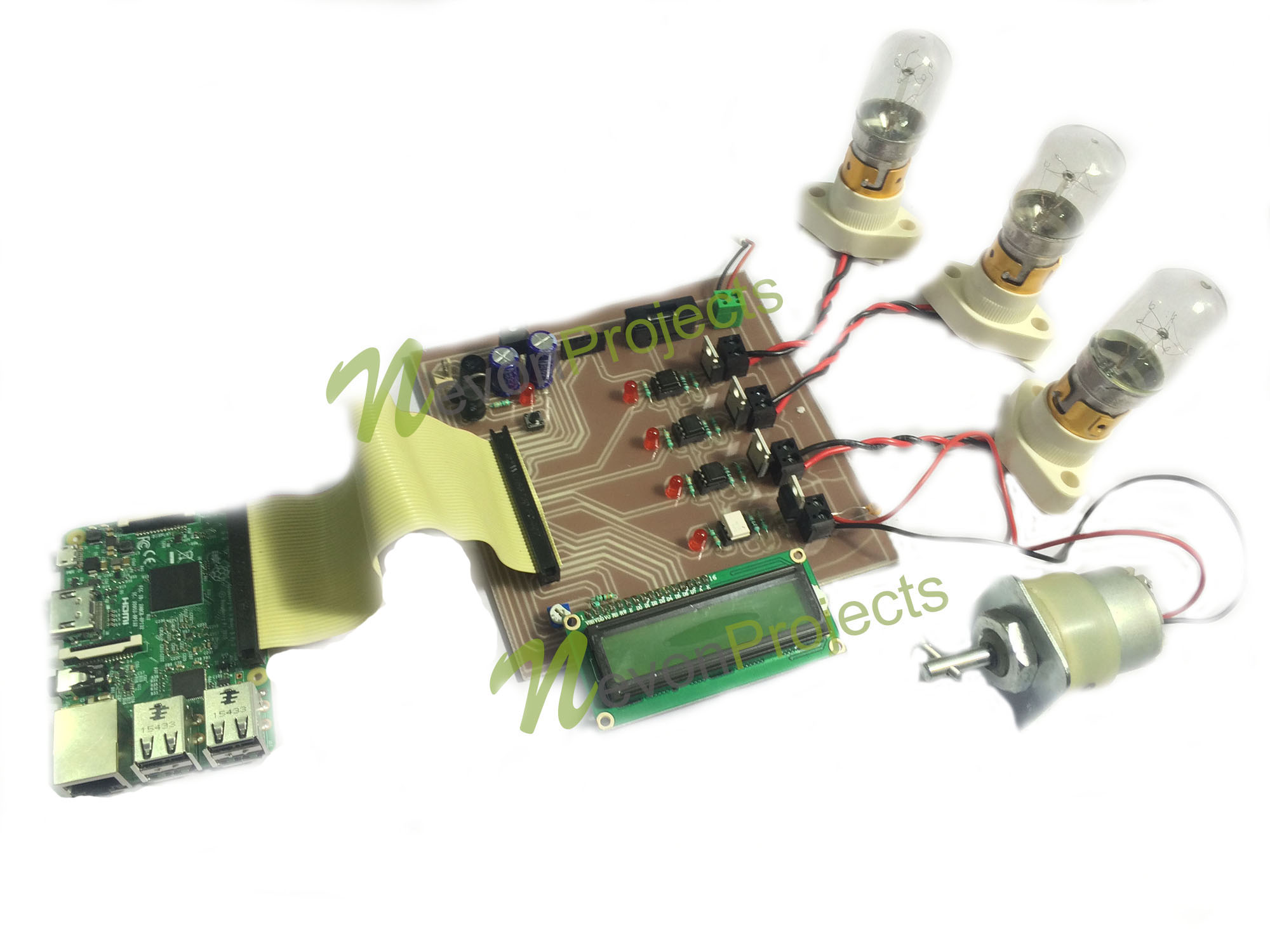
The Raspberry Pi is a versatile and affordable single-board computer that is perfect for IoT projects. Its small size, low power consumption, and wide range of connectivity options make it ideal for managing remote IoT devices.
Read also:Knicks Vs Spurs A Deep Dive Into The Rivalry And Key Matchups
Steps to Set Up Raspberry Pi
- Download and install the Raspberry Pi OS on an SD card.
- Connect your Raspberry Pi to your network via Ethernet or Wi-Fi.
- Install necessary software and libraries for IoT communication.
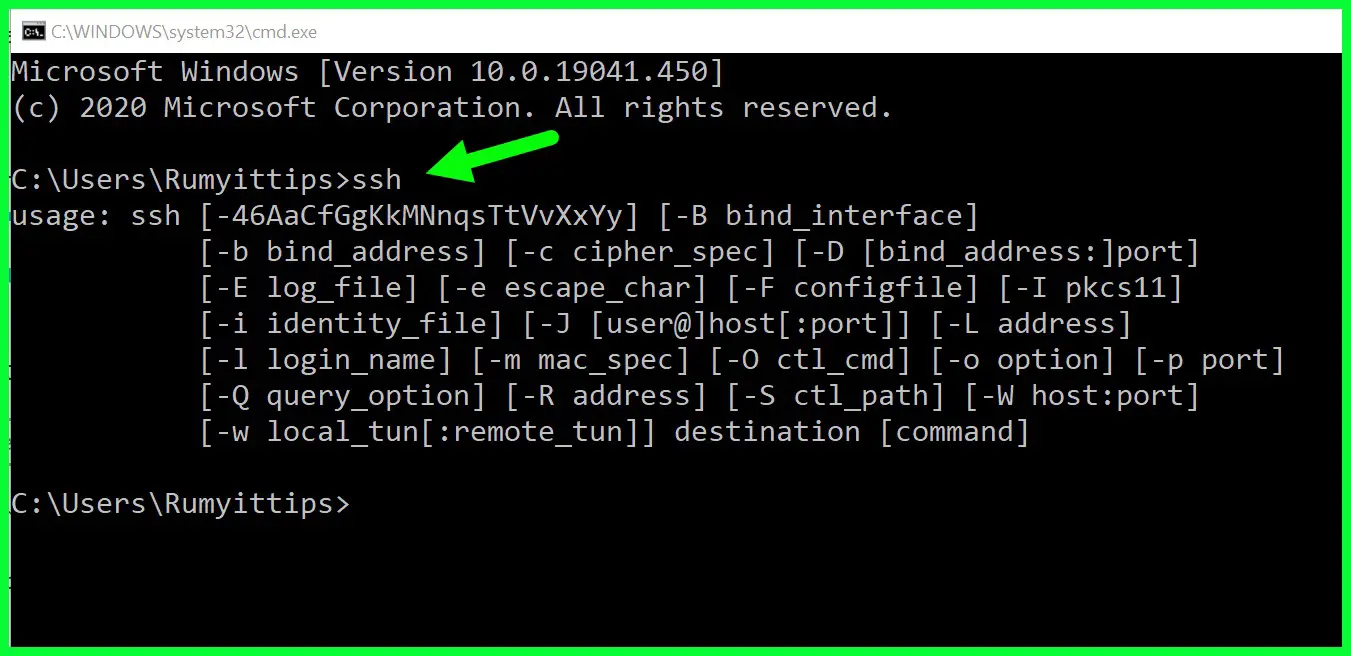
- Configure SSH for remote access and management.
Secure Connection Methods for IoT Devices
Using SSL/TLS for Encryption
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) are cryptographic protocols designed to provide secure communication over a network. By implementing SSL/TLS, you can encrypt data transmitted between your IoT devices and the cloud, ensuring that it cannot be intercepted or tampered with.
Implementing Authentication Protocols
Authentication is a crucial aspect of IoT security. By using protocols such as OAuth 2.0 or JSON Web Tokens (JWT), you can ensure that only authorized devices and users can access your system.
Windows Free Download Options
Free Windows for Raspberry Pi
Windows IoT Core is a lightweight version of Windows designed specifically for IoT devices. It can be downloaded and installed on a Raspberry Pi for free, providing a familiar environment for developers who prefer working with Windows.
Legal Considerations
When downloading any software for free, it's important to ensure that it is from a legitimate source. Always verify the authenticity of the download link and check for any licensing restrictions that may apply.
Best Practices for Securing IoT Devices
Regular Firmware Updates
Keeping your IoT devices up to date with the latest firmware is essential for maintaining security. Manufacturers frequently release updates to address vulnerabilities and improve performance.
Network Segmentation
Segmenting your network can help isolate IoT devices from other systems, reducing the risk of a breach spreading throughout your network. By creating separate subnets for different types of devices, you can enhance overall security.
Troubleshooting Common Issues
Connection Problems
Connection issues can arise due to a variety of factors, including network configuration, hardware malfunctions, or software errors. To troubleshoot these problems, start by checking your network settings and ensuring that all devices are properly connected.
Security Alerts
If you receive security alerts from your IoT devices, it's important to investigate them promptly. These alerts could indicate potential vulnerabilities or unauthorized access attempts. Use your security logs to identify the source of the issue and take appropriate action.
Case Studies: Real-World Applications
Smart Agriculture
In the agricultural sector, IoT devices are used to monitor soil moisture, temperature, and other environmental factors. By securely connecting these devices to a VPC and managing them with a Raspberry Pi, farmers can optimize their operations and improve crop yields.
Industrial Automation
Manufacturing plants rely on IoT devices for monitoring and controlling equipment. Implementing secure connection methods and best practices can help prevent costly downtime and ensure smooth operations.
Conclusion
Securing remote IoT devices is a complex but essential task in today's digital landscape. By leveraging a Virtual Private Cloud (VPC), integrating a Raspberry Pi, and using secure connection methods, you can create a robust and secure system for managing your IoT devices.
We encourage you to take action by implementing the strategies outlined in this guide. Whether you're setting up a VPC, configuring a Raspberry Pi, or downloading Windows for free, each step brings you closer to a secure and efficient IoT ecosystem. Don't forget to share your thoughts and experiences in the comments below, and explore other articles on our site for more valuable insights.