In the age of interconnected devices, securely connecting remote IoT VPC Raspberry Pi to Android for free has become a critical skill for tech enthusiasts and professionals alike. As IoT devices proliferate, ensuring secure communication between devices is more important than ever. This guide will walk you through the process of setting up a secure connection, step by step, while maintaining optimal performance.
With billions of IoT devices expected to be deployed globally in the coming years, the need for secure and efficient remote connections has never been greater. In this article, we'll explore the best practices for securely connecting remote IoT VPC Raspberry Pi to Android devices without incurring unnecessary costs. Whether you're a beginner or an advanced user, this guide has something for everyone.
Our focus will be on creating a secure environment that ensures data integrity, privacy, and accessibility. By following the steps outlined in this article, you'll be able to connect your Raspberry Pi to your Android device through a Virtual Private Cloud (VPC) while maintaining the highest standards of security.
Read also:Paul Walker The Legacy Of A Hollywood Icon
Table of Contents
- Introduction to IoT VPC
- Raspberry Pi Overview
- Android Connection Basics
- Setting Up VPC
- Securing Remote Connections
- Free Tools and Software
- Best Practices for Security
- Troubleshooting Common Issues
- Advanced Techniques
- Conclusion and Next Steps
Introduction to IoT VPC
The Internet of Things (IoT) has revolutionized how we interact with technology, but it also introduces new challenges, particularly in terms of security. A Virtual Private Cloud (VPC) provides a secure and isolated environment for your IoT devices to operate within. By using a VPC, you can protect sensitive data and ensure that only authorized devices can communicate with each other.
Why is VPC important? A VPC acts as a secure network layer that separates your IoT devices from the public internet, reducing the risk of unauthorized access and cyberattacks. This is especially crucial when dealing with remote connections, where data is transmitted over potentially insecure networks.
Key Benefits of Using VPC for IoT
- Enhanced security through network isolation
- Controlled access to devices and resources
- Scalability for growing IoT deployments
- Improved performance through optimized routing
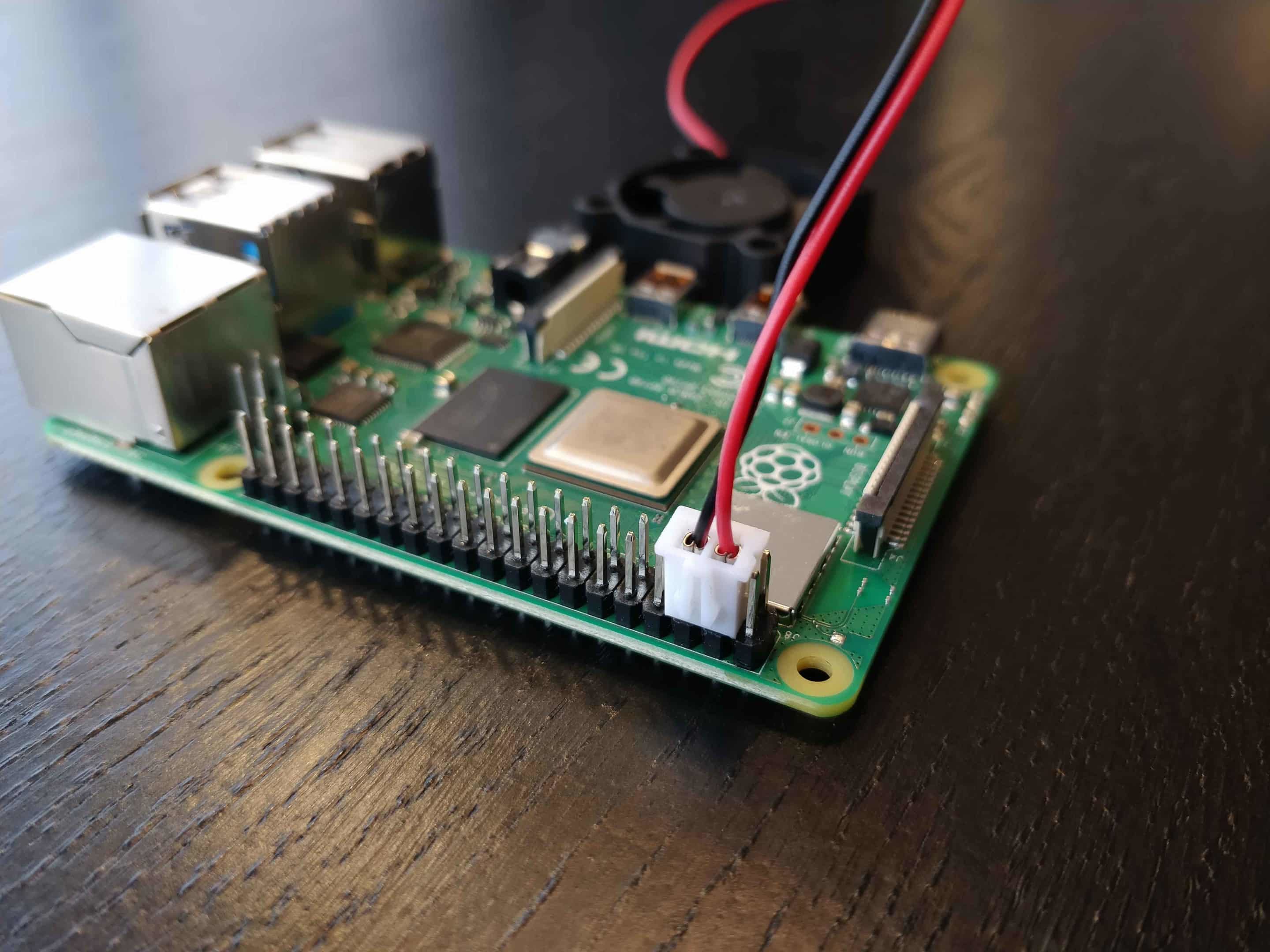
Raspberry Pi Overview
The Raspberry Pi is a versatile single-board computer that has become a favorite among hobbyists and professionals alike. Its affordability, compact size, and powerful capabilities make it an ideal choice for IoT projects. Whether you're building a smart home system or a remote monitoring solution, the Raspberry Pi can handle it with ease.
For this guide, we'll focus on using the Raspberry Pi as the central hub for your IoT devices. By connecting it to a VPC, you can securely manage and monitor your devices from anywhere in the world.
Key Features of Raspberry Pi
- Low power consumption
- Support for multiple operating systems
- Extensive GPIO capabilities
- Wide range of community support and resources
Android Connection Basics
Connecting your Android device to a remote IoT VPC Raspberry Pi setup is a straightforward process, but it requires careful planning and execution. Android devices offer a variety of tools and apps that can facilitate secure connections, making them an excellent choice for managing IoT devices on the go.
Why choose Android? Android's open-source nature and vast ecosystem of apps make it highly customizable and compatible with a wide range of IoT devices. Additionally, many Android devices come with built-in features that enhance security, such as encryption and two-factor authentication.
Read also:Tyus Jones The Rising Star In Professional Basketball
Steps to Connect Android to Raspberry Pi
- Install a secure SSH client on your Android device
- Configure the Raspberry Pi to accept remote connections
- Set up port forwarding on your router
- Test the connection using a secure tunnel
Setting Up VPC
Setting up a Virtual Private Cloud (VPC) is a critical step in securing your IoT devices. A VPC allows you to create a private network within the public cloud, providing an additional layer of security for your devices. By following the steps below, you can set up a VPC that meets your specific needs.
Step-by-Step Guide to Setting Up VPC
- Choose a cloud provider that supports VPC (e.g., AWS, Google Cloud)
- Create a new VPC and configure its settings
- Set up subnets and routing tables
- Configure security groups and access control lists
- Deploy your IoT devices within the VPC
Securing Remote Connections
Securing remote connections is essential to protecting your IoT devices from unauthorized access. By implementing strong security measures, you can ensure that only authorized devices and users can access your VPC and Raspberry Pi setup.
Best practices for securing remote connections:
- Use strong passwords and enable two-factor authentication
- Encrypt all data transmissions using SSL/TLS
- Regularly update firmware and software
- Monitor network activity for suspicious behavior
Encryption Protocols for IoT
Encryption is a key component of secure IoT communication. By using protocols such as SSL/TLS, you can ensure that all data transmitted between your devices is encrypted and secure.
Free Tools and Software
There are several free tools and software available that can help you securely connect your IoT VPC Raspberry Pi to Android devices. These tools range from SSH clients to network monitoring software, providing everything you need to manage your IoT setup without breaking the bank.
Recommended free tools:
- Termius (SSH client for Android)
- Wireshark (network monitoring tool)
- OpenSSH (secure shell software)
- WireGuard (VPN software)
Why Choose Free Tools?
Free tools offer a cost-effective way to secure your IoT devices without sacrificing quality or functionality. Many of these tools are developed by open-source communities and are regularly updated to address security vulnerabilities.
Best Practices for Security
Implementing best practices for security is essential to protecting your IoT devices and ensuring the integrity of your data. By following these guidelines, you can minimize the risk of cyberattacks and unauthorized access.
Key Security Best Practices
- Regularly update all software and firmware
- Use strong, unique passwords for all devices
- Enable two-factor authentication wherever possible
- Limit access to sensitive data and resources
- Monitor network activity for suspicious behavior
Troubleshooting Common Issues
Even with the best planning and execution, issues can arise when setting up a secure IoT VPC Raspberry Pi connection. Below are some common issues and their solutions:
Common Issues and Solutions
- Connection problems: Check your network settings and ensure that port forwarding is correctly configured.
- Authentication errors: Verify that your credentials are correct and that two-factor authentication is properly set up.
- Performance issues: Optimize your network settings and ensure that your devices are up to date.
Advanced Techniques
For users looking to take their IoT security to the next level, there are several advanced techniques that can enhance the security and performance of your setup. These techniques include using containerization, implementing zero-trust architecture, and leveraging machine learning for threat detection.
Containerization for IoT
Containerization allows you to isolate your IoT applications and services, reducing the risk of vulnerabilities spreading across your network. By using tools like Docker, you can create secure and portable containers for your IoT applications.
Conclusion and Next Steps
Securing remote IoT VPC Raspberry Pi connections to Android devices is a critical task that requires careful planning and execution. By following the steps outlined in this guide, you can create a secure and efficient setup that meets your needs while maintaining optimal performance.
Key takeaways:
- Use a VPC to isolate your IoT devices from the public internet
- Implement strong security measures, such as encryption and two-factor authentication
- Regularly update your software and firmware to address vulnerabilities
- Monitor network activity for suspicious behavior
We encourage you to share your thoughts and experiences in the comments below. Additionally, feel free to explore our other articles for more insights into IoT security and technology. Together, we can build a safer and more connected world.
References: